The threat actors stole details and utilized Clop’s leaks website to demand cash in an extortion scheme, even though no ransomware was deployed.
Scientists have determined a established of threat actors (dubbed UNC2546 and UNC2582) with connections to the FIN11 and the Clop ransomware gang as the cybercriminal group powering the worldwide zero-day assaults buyers of the Accellion legacy File Transfer Appliance item.
Simply click to Register
Multiple Accellion FTA shoppers, which include the Jones Day Law Firm, Kroger and Singtel, have all been attacked by the team, getting extortion emails threatening to publish stolen details on the “CL0P^_- LEAKS” .onion web page, in accordance to an investigation from Accellion and FireEye Mandiant. Around 100 companies have been victims of the attack, analysts discovered, with all-around 25 suffering “significant details theft.” No ransomware was employed in the attacks.
“Notably, the range of victims on the “CL0P^_- LEAKS” shaming website has amplified in February 2021 with companies in the United States, Singapore, Canada and the Netherlands not too long ago outed by these danger actors,” in accordance to the Mandiant results, issued on Monday.
4 Accellion FTA Zero-Times
As famous, the place of entry for the assaults was Accellion FTA, a 20-yr-outdated legacy product or service utilised by big companies about the entire world. Accellion claimed that it became knowledgeable of a zero-day security vulnerability in FTA in mid-December, which it scrambled to patch promptly. But that turned out to be just one of a cascade of zero-days in the system that the corporation uncovered only following they came less than attack from cyber-adversaries.
“This preliminary incident was the starting of a concerted cyberattack on the Accellion FTA merchandise that ongoing into January 2021,” the enterprise spelled out. “Accellion identified further exploits in the ensuing weeks, and fast developed and introduced patches to shut every vulnerability.”
Four zero-working day security holes ended up exploited in the assaults, according to the investigation:
- CVE-2021-27101 – SQL injection through a crafted Host header
- CVE-2021-27102 – OS command execution via a community web provider phone
- CVE-2021-27103 – SSRF through a crafted Submit ask for
- CVE-2021-27104 – OS command execution through a crafted Put up request
And, the released sufferer info seems to have been stolen working with a unique “DEWMODE” web shell, according to Mandiant, which additional, “The exfiltration activity has afflicted entities in a wide assortment of sectors and nations.”
DEWMODE Web Shell for Thieving Details
Mandiant found that a precise web shell, which it calls DEWMODE, was employed to exfiltrate facts from Accellion FTA devices. The adversaries 1st exploited one of the zero-times, then used that accessibility to install DEWMODE.
“Across these incidents, Mandiant noticed typical infrastructure use and TTPs [tactics, techniques and procedures], including exploitation of FTA gadgets to deploy the DEWMODE web shell,” Mandiant decided. “A widespread risk actor we now keep track of as UNC2546 was liable for this activity. Though finish facts of the vulnerabilities leveraged to install DEWMODE are continue to staying analyzed, evidence from many client investigations has proven multiple commonalities in UNC2546’s activities.”
The agency is continue to examining the zero-working day exploitation, but it did say that in the early attacks in December, UNC2546 leveraged an SQL injection vulnerability in the Accellion FTA as its main intrusion vector. SQL injection was then followed by subsequent requests to more resources.
“UNC2546 has leveraged this SQL injection vulnerability to retrieve a important which appears to be made use of in conjunction with a ask for to the file sftp_account_edit.php,” according to the analysis. “Immediately right after this ask for, the constructed-in Accellion utility admin.pl was executed, resulting in an eval web shell remaining created to oauth.api. Almost straight away following this sequence, the DEWMODE web shell is written to the method.”
DEWMODE, once embedded, extracts a list of offered data files from a MySQL databases on the FTA and lists people information and corresponding metadata—file ID, path, filename, uploader and recipient—on an HTML page. UNC2546 then makes use of the introduced listing to obtain information via the DEWMODE web shell.
In a subset of incidents, Mandiant noticed UNC2546 requesting a file named cache.js.gz – an archive that probably contained a dump of a database.
Extortion by means of Clop Leaks Website
As soon as DEWMODE was put in, victims commenced to acquire extortion e-mails from an actor claiming association with the Clop ransomware group gang.
These are tailored to every sufferer and sent from a free email account, to a tiny number of addresses at the victim firm. If the victim did not answer in a timely manner, much more e-mails are sent, this time to hundreds or hundreds of various email accounts, employing diverse SMTP infrastructure.
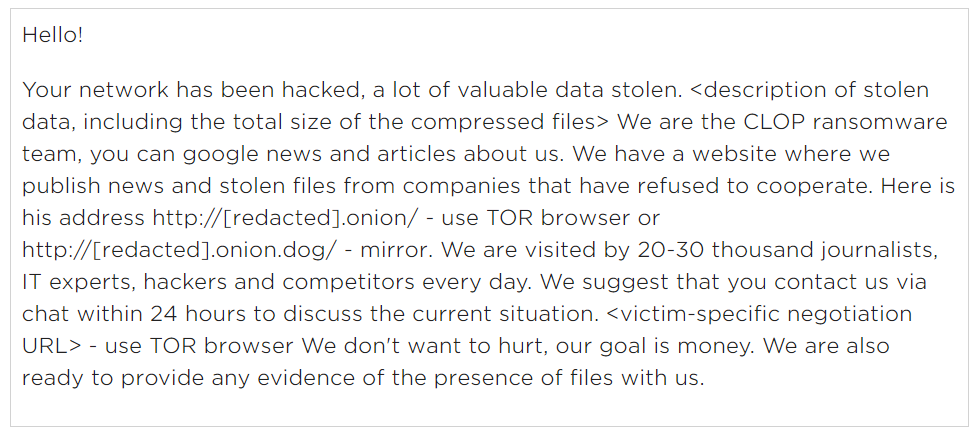
The preliminary extortion be aware despatched to victims of the Accellion FTA assaults. Source: FireEye Mandiant.
“In at least a person situation, UNC2582 also despatched email messages to associates of the sufferer firm that incorporated inbound links to the stolen knowledge and negotiation chat,” according to Mandiant.
The company also discovered via monitoring the CL0P^_- LEAKS shaming web page that UNC2582 has adopted by way of on threats to publish stolen facts.
“Several new victims have appeared on the internet site in modern months, like at the very least one particular business that has publicly verified that their Accellion FTA system experienced been not long ago specific,” in accordance to Mandiant.
FIN11, Clop and UNC2546
FIN11 is a fiscally inspired group that has been close to for at least 4 years, conducting common phishing campaigns. Nevertheless, it proceeds to evolve. It additional the use of Clop (which emerged in February 2019) and double extortion in October and included stage-of-sale (POS) malware to its arsenal in 2018. In 2019, it begun conducting run-of-the-mill ransomware assaults.
Mandiant has earlier located that FIN11 threatened to write-up stolen victim data on the same .onion site employed in the Accellion FTA attacks, commonly in a double-extortion need adhering to the deployment of Clop ransomware. On the other hand, researchers found that the cybercriminals associated in these hottest assaults are probably unique from FIN11 by itself despite sharing some overlaps.
“We are now monitoring the exploitation of the zero-day Accellion FTA vulnerabilities and information theft from providers running the legacy FTA product or service as UNC2546, and the subsequent extortion action as UNC2582,” according to Mandiant. “We have discovered overlaps among UNC2582, UNC2546 and prior FIN11 operations, and we will carry on to appraise the interactions involving these clusters of action.”
Some of the overlaps amongst UNC2582’s facts-theft extortion exercise and prior FIN11 operations incorporate prevalent email senders.
“Some UNC2582 extortion emails noticed in January 2021 were sent from IP addresses and/or email accounts utilized by FIN11 in various phishing campaigns between August and December 2020, including some of the very last campaigns that were being clearly attributable to the group,” according to the investigation.
FIN11 has also made use of identical the CL0P^_- LEAKS shaming web site and is recognised for deploying Clop ransomware.
“The UNC2582 extortion email messages contained a link to the CL0P^_- LEAKS web-site and/or a victim particular negotiation webpage,” in accordance to Mandiant. “The connected web-sites had been the same kinds used to assist historic Clop operations, a sequence of ransomware and facts theft extortion campaigns we suspect can be solely attributed to FIN11.”
When it will come to the zero-working day cluster of action, attributed to UNC2546, there are also constrained overlaps with FIN11. Exclusively, a lot of of the corporations compromised by UNC2546 have been earlier focused by FIN11.
And, “an IP handle that communicated with a DEWMODE web shell was in the ‘Fortunix Networks L.P.’ netblock, a network routinely utilized by FIN11 to host obtain and FRIENDSPEAK command-and-manage (C2) domains.”
There is also a link in between UNC2546 and UNC2582, the agency observed: In at least one case, the UNC2546 attackers interacted with DEWMODE from a host that was made use of to mail UNC2582-attributed extortion email.
“The overlaps in between FIN11, UNC2546 and UNC2582 are powerful, but we go on to track these clusters independently even though we consider the character of their associations,” Mandiant concluded. “One of the particular issues is that the scope of the overlaps with FIN11 is constrained to the later on levels of the attack lifestyle cycle. UNC2546 takes advantage of a distinct an infection vector and foothold, and unlike FIN11, we have not noticed the actors increasing their existence across impacted networks.”
Also, using SQL injection to deploy DEWMODE would characterize a important change in FIN11 TTPs, “given the team has traditionally relied on phishing strategies as its original infection vector and we have not formerly noticed them use zero-working day vulnerabilities,” Mandiant additional.
Is your tiny- to medium-sized small business an quick mark for attackers?
Threatpost WEBINAR: Preserve your place for “15 Cybersecurity Gaffes SMBs Make,” a FREE Threatpost webinar on Feb. 24 at 2 p.m. ET. Cybercriminals count on you making these problems, but our experts will aid you lock down your smaller- to mid-sized business enterprise like it was a Fortune 100. Register NOW for this LIVE webinar on Wed., Feb. 24.
Some parts of this article are sourced from:
threatpost.com


 Silicon Valley VC Firm Phished
Silicon Valley VC Firm Phished