Performing oil pumps are viewed from a sunset sky. Intezer uncovered a calendar year-extensive spear-phishing marketing campaign against energy corporations. (Getty Illustrations or photos)
An unknown group has been conducting a 12 months-long spear-phishing campaign in opposition to vitality firms and other industries close to the globe.
The campaign has been taking place for at minimum a yr and targets providers and staff in the gas and oil, strength, information technology, media and electronics industries close to the environment, according to new analysis from Intezer, although a lot of of the affected enterprises are situated in South Korea. The spear-phish email messages leverage each typosquatting and spoofing to make the incoming e-mails glance like they are coming from proven corporations. They also reference executives from the corporation by name and consist of authentic enterprise addresses and enterprise logos.
A lot of of the spear-phishing emails display how the danger actor seems to have done their homework, crammed with procurement language jargon, referencing genuine ongoing initiatives the impersonated enterprise is doing the job on and inviting the goal to bid for a portion of the function by clicking on an attachment.
That attachment – which is designed to mimic the physical appearance of a PDF but is generally an IMG, ISO or Cab file — consists of info-stealing malware to steal banking information, log keystrokes and acquire searching data. The actors don’t seem to depend on a one kind or loved ones of malware, rather employing a range of remote accessibility applications and other malware-as-a-assistance, like Agent Tesla and Formbook. Like several profitable phishing lures, they are designed to give a monetary incentive to the sufferer to click on on the hyperlink and create a sense of urgency in responding.
“It looks like part of the incentive was that the acquiring component could think that there is some dollars coming their way,” said Ryan Robinson, a security researcher at Intezer, in an interview.
In one particular example, a faux email account pretending to be from Hyundai Engineering Inc. mentions a true electricity plant task in Panama, is filled with procurement jargon and presents limited turnaround deadlines for expressing curiosity in the task (48 hrs from receipt of email) and publishing a bid (March 29). In a different, an employee from Netherlands-centered offshore drilling business GustoMSC asks the concentrate on to signal and return a non-disclosure doc and mentions a wind farm in Dunkirk managed by GustoMSC.
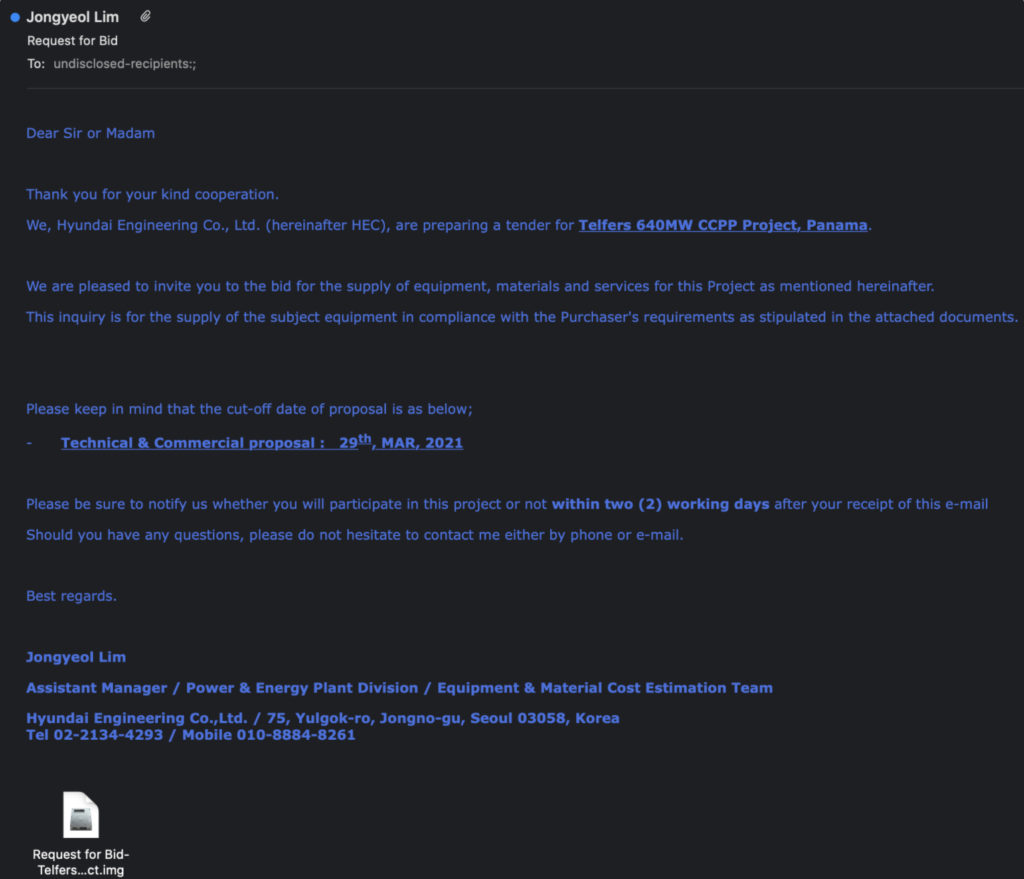 A phishing email impersonating an worker of Hyundai Engineering inviting the concentrate on to simply click on a destructive attachment.
A phishing email impersonating an worker of Hyundai Engineering inviting the concentrate on to simply click on a destructive attachment.
The researchers say most of the firms qualified in the campaign had been South Korean, whilst a variety of targets from other international locations wound up getting some substantial small business connection to South Korea. A single small business that seems to stand out from the rest of the targeted victims is the Korean branch of the Significantly East Broadcasting Corporation, an worldwide Christian radio broadcaster. FEBC is recognised for broadcasting the Gospel and religious packages throughout borders into countries that outlaw or prohibit religious liberty, which include North Korea.
Robinson reported the emails ended up generally in English and are “slightly greater than average” in phrases of their presentation, tending to lack several of the clear typos or language faults that give absent other campaigns, nevertheless they take note they could not thoroughly scrutinize some of the e-mails because they have been in Korean and Intezer does not have a native Korean-speaker on team. A different Intezer researcher, Nicole Fishbein, reported there were being other indicators that the spearphishers did their homework for each goal.
“I feel the language of the email, all the conditions that are related to the business enterprise of oil and fuel, and even engineering phrases, it looks like the persons that are at the rear of it genuinely understand what they’re chatting about,” Fishbein mentioned.
Intezer pointedly does not make or attempt any attribution about the actors or group behind the campaign. Fishbein and Robinson mentioned that is partly owing to the absence of a clear or set up patterns in the sorts of malware deployed, as well as their prevalent use by other threat actors. Robinson claimed they had to cross-reference malware-laced images to e-mail obtained and opened by the sufferer on the similar day, ultimately accumulating facts from hundreds of email messages that they could conclusively tie to the campaign.
The character of the malware strains and the type of information stolen signifies that the action could be the 1st action in a much larger hacking venture.
“I would say that for the reason that we see the malware shipped is an details stealer and not ransomware, they’re right after info, it could be info for the upcoming phase of the marketing campaign,” reported Fishbein.
Intezer’s web site lists Indicators of Compromise for the spear-phishing emails and malware utilized in the campaign, and Robinson explained appropriately configured email security protocols like DMARC and SPF can also assist lessen or get rid of many of the lures that count on spoofing email addresses.
Some parts of this article are sourced from:
www.scmagazine.com


 Online course provider Coursera hit with API issues, with cloud driving additional exposure
Online course provider Coursera hit with API issues, with cloud driving additional exposure