The highly developed persistent menace (APT) actor acknowledged as Winter Vivern is now targeting officials in Europe and the U.S. as portion of an ongoing cyber espionage marketing campaign.
“TA473 due to the fact at the very least February 2023 has constantly leveraged an unpatched Zimbra vulnerability in publicly struggling with webmail portals that makes it possible for them to obtain entry to the email mailboxes of authorities entities in Europe,” Proofpoint said in a new report.
The company security company is monitoring the activity under its have moniker TA473 (aka UAC-0114), describing it as an adversarial crew whose functions align with that of Russian and Belarussian geopolitical goals.
What it lacks in sophistication, it helps make up for in persistence. In latest months, the team has been joined to attacks focusing on point out authorities of Ukraine and Poland as very well as federal government officials in India, Lithuania, Slovakia, and the Vatican.
The NATO-related intrusion wave entails the exploitation of CVE-2022-27926 (CVSS rating: 6.1), a now-patched medium-severity security flaw in Zimbra Collaboration that could allow unauthenticated attackers to execute arbitrary JavaScript or HTML code.
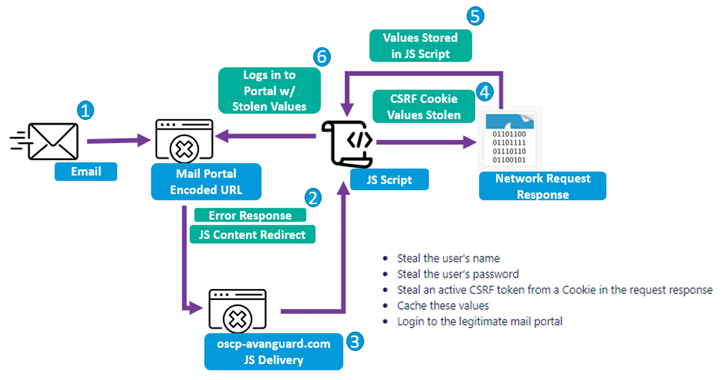
This also involves utilizing scanning instruments like Acunetix to recognize unpatched webmail portals belonging to qualified businesses with the purpose of sending phishing email under the guise of benign government organizations.
The messages occur with booby-trapped URLs that exploit the cross-internet site scripting (XSS) flaw in Zimbra to execute personalized Foundation64-encoded JavaScript payloads inside the victims’ webmail portals to exfiltrate usernames, passwords, and accessibility tokens.
It truly is well worth noting that every JavaScript payload is customized to the focused webmail portal, indicating that the risk actor is keen to spend time and resources to decrease the likelihood of detection.
“TA473’s persistent approach to vulnerability scanning and exploitation of unpatched vulnerabilities impacting publicly going through webmail portals is a critical aspect in this actor’s good results,” Proofpoint claimed.
“The group’s emphasis on sustained reconnaissance and painstaking analyze of publicly exposed webmail portals to reverse engineer JavaScript able of thieving usernames, passwords, and CSRF tokens demonstrates its financial investment in compromising precise targets.”
The results appear amid revelations that at least 3 Russian intelligence businesses, together with FSB, GRU (joined to Sandworm), and SVR (linked to APT29), probably use software and hacking instruments produced by a Moscow-centered IT contractor named NTC Vulkan.
THN WEBINARBecome an Incident Response Pro!
Unlock the insider secrets to bulletproof incident response – Master the 6-Phase approach with Asaf Perlman, Cynet’s IR Leader!
Do not Miss out on Out – Help save Your Seat!
This contains frameworks like Scan (to aid substantial-scale information selection), Amesit (to carry out data operations and manipulate public view), and Krystal-2B (to simulate coordinated IO/OT assaults towards rail and pipeline management systems).
“Krystal-2B is a schooling platform that simulates OT attacks in opposition to distinctive kinds of OT environments in coordination with some IO factors by leveraging Amesit ‘for the goal of disruption,'” Google-owned Mandiant explained.
“The contracted tasks from NTC Vulkan supply insight into the financial commitment of Russian intelligence expert services into establishing capabilities to deploy far more economical functions within just the commencing of the attack lifecycle, a piece of functions typically concealed from our view,” the danger intelligence business explained.
Uncovered this write-up appealing? Comply with us on Twitter and LinkedIn to go through additional special material we put up.
Some parts of this article are sourced from:
thehackernews.com

 GCHQ Updates Security Guidance for Boards
GCHQ Updates Security Guidance for Boards