Alterations in the way we work have experienced sizeable implications for cybersecurity, not minimum in network monitoring. Employees no longer sit safely and securely side-by-facet on a company network, dev teams consistently spin up and tear down methods, exposing products and services to the internet. Preserving keep track of of these end users, changes and providers is complicated – internet-struggling with attack surfaces not often keep the similar for prolonged.
But a safe performing network is the spine of each and every modern small business, and with so numerous distinct attack vectors and entry points, relying on firewalls and stage-in-time scanning is no longer plenty of. You will need to fully grasp how your firewalls are remaining improved in actual-time, with true-entire world validation of how they’re configured. You require steady network checking.
What requirements preserving in your network?
There is so much sprawl in today’s corporate networks with distant functioning, cloud computing and third-celebration integrations, that it really is no lengthier just the units or techniques that you have in your office and details heart that have to have guarding.
From the hardware and software package of the network by itself, to all the units employed to entry it, from IoT endpoints to laptops and smartphones, network security now demands to search outside of the perimeter to your cloud assets, edge products, 3rd-get together hosted content material, integrations with other hardware or software program, and belongings hosted in dispersed offices.
Just to complicate issues more, some of these products and services, specifically individuals hosted in the cloud, may only be active for a shorter room of time for particular jobs, occasions, deployments, or by style and design. With this sort of a dispersed network, the castle-and-moat design of network security is no for a longer time healthy for goal.
What can go mistaken with your network?
Vulnerabilities can be released to your network in a selection of strategies, such as misconfigurations, expiring certificates, new property additional to cloud environments, missing patches, or unnecessarily exposing solutions to the internet. In addition, there is the ever-current risk of attack from phishing, provide chain compromises and uncovered qualifications.
For instance, a Windows SMB services on your internal network is not a vulnerability, but exposing 1 to the internet is a diverse subject solely – which is what led to the WannaCry ransomware attack that unfold throughout the earth. Equally, Australian telco Optus experienced a devastating knowledge breach in 2022 that uncovered aspects of 11 million buyers. The breach occurred through an unprotected and publicly-exposed API which did not need consumer authentication, so anyone that discovered the API on the internet could hook up to it with out a username or password.
How can you protect your network?
Continual network monitoring supported by common scanning could have picked up equally of these vulnerabilities and prevented these breaches. Checking works by using automation to detect and determine flaws and weak spots in your equipment, application application and operating programs. It does this by sending probes to glance for open up ports and services, and once the record of companies is identified, probing each individual for a lot more info, configuration weaknesses or regarded vulnerabilities.
It’s typical to have a array of techniques in your network, from laptops and workstations in the office environment or at home, to methods in cloud platforms like AWS, Azure, and Google Cloud. Your team could nicely use a range of operating systems much too. Deciding what to incorporate in your network scan can be challenging, but there are a number of ways to tackle it: publicity based, sensitivity centered and protection dependent.
Why do you will need to monitor constantly?
Your network is constantly modifying. New expert services are spun up, web apps updated, permissions modified, devices extra and eradicated. All of these can introduce opportunity vulnerabilities. The objective of steady monitoring is to provide around-fast responses and perception into these modifications, examining and prioritizing vulnerabilities, so you can comprehend the risk across your complete infrastructure.
With this clear photo of what attackers can see and what is actually available in your internet-dealing with infrastructure, you can simply tackle any troubles as before long as they arise. Ongoing monitoring not only supplies visibility into the vulnerabilities in your IT atmosphere and distant gadgets, but also clarity into how all those vulnerabilities translate into enterprise risk, and which are most probably to be specific by attackers.
Continual network checking with Intruder
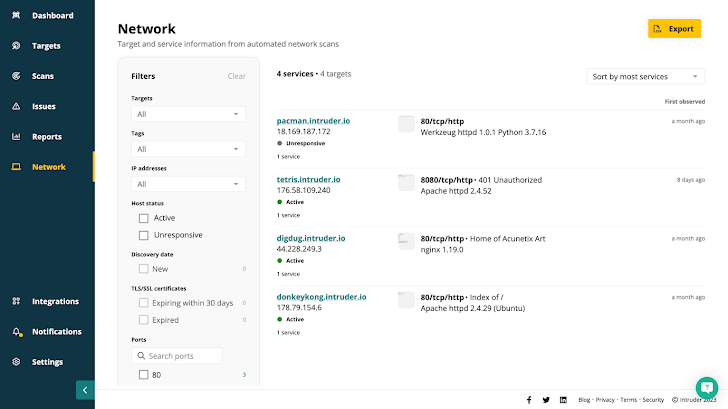
Superior network checking instruments like Intruder operate everyday network scans so your network see is often accurate and up to date – demonstrating active and unresponsive targets, any alterations since your past scan, expiring certificates, and the ports and expert services you anticipate – and far more importantly, you should not expect – to be uncovered to the internet.
 Intruder provides you a true check out of your attack surface combining continual network checking, automated vulnerability scanning, and proactive danger reaction in a person system.
Intruder provides you a true check out of your attack surface combining continual network checking, automated vulnerability scanning, and proactive danger reaction in a person system.
Any targets you incorporate will kick off a scan. After completed, it provides the focus on to the queue for rescanning at typical intervals. Any improvements will instantly kick off a vulnerability scan, with issues prioritized by context so you can repair what matters most.
If you’re lucky ample to have your individual network array, you know how useful it can be but how hard to manage. You want to make sure your entire range is lined, but licensing extensive quantities of inactive IPs can be pricey. Intruder screens your exterior network ranges for lively IPs – but you may only pay for the types in use.
This continual checking gives extensive and up-to-day visibility across your full IT surroundings to choose your network security to yet another degree.
Take a look at Intruder to activate a free 14-day trial and knowledge continuous network checking for on your own.
Observed this write-up fascinating? Comply with us on Twitter and LinkedIn to examine a lot more distinctive written content we post.
Some parts of this article are sourced from:
thehackernews.com


 Russian Hackers Use Zulip Chat App for Covert C&C in Diplomatic Phishing Attacks
Russian Hackers Use Zulip Chat App for Covert C&C in Diplomatic Phishing Attacks