It is a double-extortion play that works by using the command-line password ‘KissMe’ to hide its nasty acts and adorns its ransom take note with cutesy ASCII bunny art.
A new ransomware family, White Rabbit, chewed by way of a neighborhood U.S. financial institution past thirty day period — and it may be related to the monetarily determined highly developed persistent menace (APT) group known as FIN8, researchers explained.
In a Tuesday report, Trend Micro researchers said that this twicky wabbit is familiar with how to burrow away the place it just can’t be spotted. In fact, it appears to be like like the operators behind the White Rabbit ransomware have taken a web site from the additional proven ransomware loved ones known as Egregor when it comes to hiding their malicious action, scientists said.
Egregor, which claimed obligation for a nicely-publicized cyberattack on Barnes & Noble in October 2020, is a ransomware-as-a-service (RaaS) player that sparked an FBI warning after compromising far more than 150 organizations in shorter buy immediately after its birth.
White Rabbit could be sneaky, but it leaves tracks. The ransomware was spotted by multiple security outfits, and was first detected on Dec. 14 by the Lodestone Forensic Investigations staff, which reported that it experienced viewed some White Rabbit exercise a couple of times previously, on Dec. 11.
But the earliest stirrings day back to July 10, when a PowerShell script was executed – a script that held script blocks that matched individuals explained in a July 27 Bitdefender posting on FIN8.
The Dec. 14 White Rabbit attack was also publicly disclosed on Twitter that same day by security researcher Michael Gillespie (@demonslay355).
🔒 #Ransomware Hunt: “White Rabbit” with extension “.scrypt”, drops note for each encrypted file with “
— Michael Gillespie (@demonslay335) December 14, 2021
Gillespie involved a backlink to the ransom take note, which incorporates cutesy bunny ASCII art. The notice warns victims that if they are studying it, their network infrastructure has been compromised, their critical info has leaked and their files are encrypted. In other text, the newcomer is employing the same double-extortion shtick employed by a skyrocketing quantity of RaaS players, threatening targets that their stolen details isn’t just encrypted but will also be printed or offered.
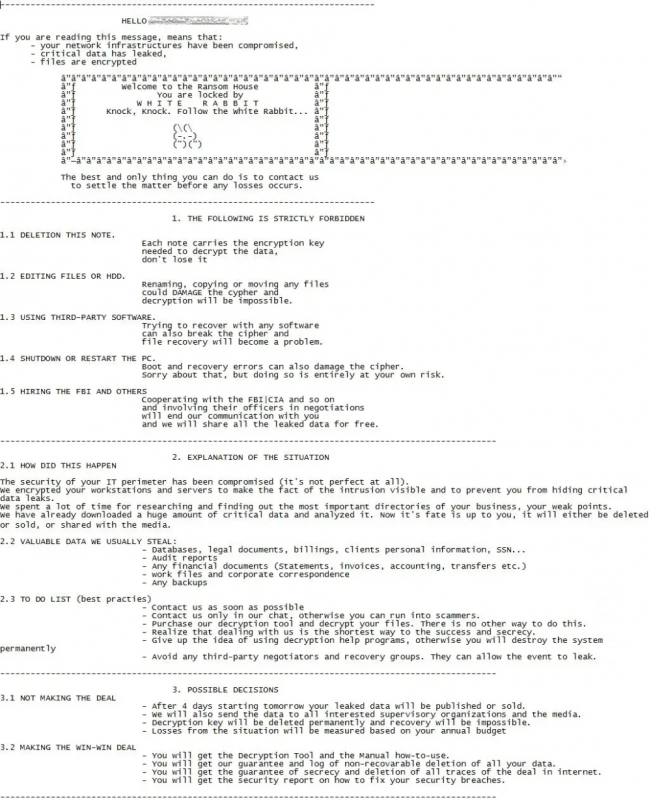
Ransom observe. Source: Gillespie’s add to PasteBin.
Command-Line Password ‘KissMe’ Utilized to Conceal Poor Acts
It gets cutesy-wutesy-er: Development Micro researchers reported that 1 of the most notable elements of the new ransomware’s attack is the use of a distinct command-line password to decrypt its internal configuration and start its ransomware regimen. In the individual situation that they came across, that password is “KissMe,” as demonstrated in the SysTracer screen capture below. SysTracer is a technique utility resource that sniffs out altered info in a system’s registry and data files.
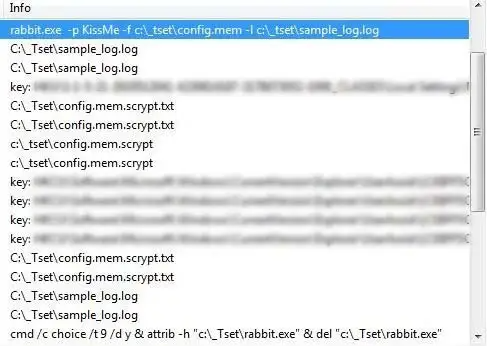
Command line, exhibiting the password “KissMe,” made use of to execute the ransomware. Supply: Trend Micro.
“This process of hiding destructive action is a trick that the ransomware household Egregor takes advantage of to disguise malware techniques from assessment,” the Craze Micro researchers pointed out, introducing that “other samples might use a various password” than KissMe.
The SysTracer picture also exhibits the arguments recognized by the ransomware, which, researchers surmised, stand in for:
- -p: password/passphrase
- -f: file to be encrypted
- -l: logfile
- -t: malware’s get started time
Cobalt Strike Connection to FIN8
Trend Micro picked up on traces of Cobalt Strike commands – the PowerShell .exe, as shown underneath – that its researchers feel “might have been used to reconnoiter, infiltrate and fall the destructive payload into the afflicted technique,” according to the report.
Traces of Cobalt Strike commands. Resource: Development Micro.
Lodestone’s evaluation of the ransomware group’s strategies, strategies, and methods (TTPs) details to the White Rabbit group most likely getting affiliated with FIN8.
FIN8 has typically made use of social engineering and spear-phishing to go following money companies and payment-card information from stage-of-sale (PoS) techniques – significantly those of merchants, dining establishments and the lodge sector. Additional just lately, it has extra ransomware to its bag of vehicles. It is been lively considering the fact that at the very least January 2016 and periodically pops in and out of dormancy in purchase to good-tune its TTPs so as to evade detection and ramp up its good results rate.
Just one instance was in August, when the most recent refinement of the APT’s BadHatch backdoor proved ready to leverage new malware on the fly with no redeployment, earning it potent and nimble.
Apart from BadHatch, FIN8’s effectively-stocked arsenal has integrated malware variants this sort of as ShellTea – a backdoor also known as PunchBuggy –and the memory-scraping malware PunchTrack.
In the December attack, White Rabbit dragged in a beforehand unseen edition of BadHatch that, based on characteristics of the malware sample acquired, Lodestone named F5.
“The precise connection in between the White Rabbit group and FIN8 is now unknown,” Lodestone stipulated. “However, Lodestone recognized a variety of TTPs suggesting that White Rabbit, if functioning independently of FIN8, has a near partnership with the much more established threat group or is mimicking them.”
White Rabbit’s Ransomware Route
As Craze Micro tells it, the White Rabbit ransomware creates a note for each file it encrypts. “Each note bears the title of the encrypted file and is appended with ‘.scrypt.txt,’” researchers explained. “Prior to the ransomware program, the malware also terminates several procedures and expert services, notably antivirus-relevant ones.”
Upcoming, if the -f argument is not given, it attempts to encrypt data files in mounted, removable and network drives, as perfectly as in methods. Development Micro furnished the checklist beneath of the paths and directories the ransomware tries to skip, “to stay clear of crashing the method and destroying its possess notes.”
- *.scrypt.txt
- *.scrypt
- c:windows*
- *:sysvol*
- *:netlogon*
- c:filesource*
- *.exe
- *.dll
- *desktop.ini
- *:windows*
- c:programdata*
- *:programfiles*
- *:plan documents (x86)*
- *:system documents (x64)*
- *.lnk
- *.iso
- *.msi
- *.sys
- *.inf
- %Person Temp%*
- *thumbs.db
FIN8 Relationship However a Bit Sketchy
FIN8 and White Rabbit may perhaps be connected, or they may well really share the exact same creator: It’s not a sound phone just still, Craze Micro stated.
It could be that this is just another sign of how the team is undertaking what it’s identified for: increasing its arsenal, previous the infiltration and reconnaissance tools for which it is effectively-regarded, to add ransomware to the toolkit. “So significantly, White Rabbit’s targets have been couple of, which could imply that they are continue to tests the waters or warming up for a large-scale attack,” Trend Micro scientists pointed out.
It has an “uncomplicated” ransomware schedule, which likely means that it’s even now under progress, they said. Inspite of becoming a very simple piece of malware, it’s still dangerous: “Despite being in this early stage, nonetheless, it is crucial to emphasize that it bears the troublesome traits of contemporary ransomware: It is, after all, hugely qualified and uses double extortion approaches,” according to Craze Micro’s writeup. “As such, it is worth checking.”
Blocking White Rabbit Attacks
Both Lodestone and Pattern Micro bundled indicators of compromise in their White Rabbit writeups.
Development Micro also had the subsequent solutions for placing up a multilayered protection to “help guard towards modern day ransomware and avert the achievements of the evasion methods they employ”:
- Deploy cross-layered detection and response solutions. Obtain alternatives that can anticipate and reply to ransomware things to do, techniques, and actions prior to the threat culminates.
- Create a playbook for attack prevention and restoration. The two an incident-reaction (IR) playbook and IR frameworks permit businesses to plan for different assaults, including ransomware.
- Carry out attack simulations. Expose workers to a realistic cyberattack simulation that can support conclusion-makers, security personnel, and IR teams recognize and put together for probable security gaps and assaults.
Picture courtesy of PxHere. Licensing aspects.
Check out out our cost-free future reside and on-need on the internet city halls – exclusive, dynamic conversations with cybersecurity gurus and the Threatpost neighborhood.
Some parts of this article are sourced from:
threatpost.com

