The developer of the WeSteal cryptocurrency stealer can not be bothered with extravagant talk: they say flat-out that it is “the top way to make money in 2021”.
Some cybercriminals try, at the very least, to cover their soiled do the job with a threadbare “this will throw off the lawsuits” blanket of legitimacy. For example, phone-tracking resources that silently put in and run and which are supposedly intended for mom and dad to (legally) observe out for their little ones (in actuality, stalkerware), ransomware gangs that blab rationalizations about “helping” by recognizing zero times right before their victims do, or the other coverups employed to hawk anti-malware evasion resources, cryptocurrency miners, password crackers or webcam-light disablers.
But who has time to waste on these kinds of pretense?
Not WeSteal. As the title on your own tends to make distinct, the developers of WeSteal can’t be bothered with the flimflam. Whoever authored the new cryptocurrency-thieving tool says flat-out that it is “the leading way to make income in 2021”.
Sign up for Threatpost for “Fortifying Your Small business Towards Ransomware, DDoS & Cryptojacking Attacks” a Reside roundtable event on Wednesday, Might 12 at 2:00 PM EDT for this Absolutely free webinar sponsored by Zoho ManageEngine.
“There is no … pretense by ComplexCodes with WeSteal. There is the title of the malware by itself. Then there is the website, ‘WeSupply,’ owned by a co-conspirator, proudly stating ‘WeSupply – You profit’”, a Palo Alto Networks group says about the new device they located being peddled on the underground.
In a write-up on Thursday, the researchers picked aside the WeSteal cryptocurrency wallet-pickpocketing device and a similar remote-access trojan (RAT) termed WeControl, saying that it’s “shameless” the way the builders aren’t even hoping to hide the tools’ legitimate intent.
“WeSteal is a shameless piece of commodity malware with a solitary, illicit purpose,” they say. “Its simplicity is matched by a probable basic usefulness in the theft of cryptocurrency. The very low-sophistication actors who purchase and deploy this malware are intruders, no a lot less so than avenue pickpockets. Their crimes are as true as their victims.”
WeSteal, Nee WeSupply, Nee And so forth. And many others. And so forth.
What is new about this cryptocurrency ripper-supply? From what scientists can ascertain, generally, the name. A danger actor named ComplexCodes began marketing WeSteal on the underground in mid-February, but ahead of that, they began promoting a WeSupply Crypto Stealer in Could 2020. Code samples position to WeSteal having developed from that earlier resource.
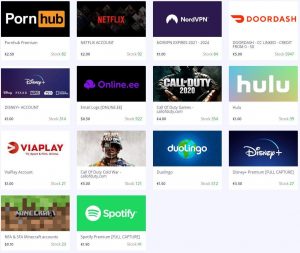
The tool’s writer also previously churned out the Zodiac Crypto Stealer, as very well as malware identified as Spartan Crypter that’s applied to toss antivirus detection off the path. Also, the Palo Alto Network analysts located proof linking ComplexCodes to a web site that sells stolen accounts for solutions this kind of as Netflix, Disney+, Pornhub, Spotify, Hulu and more.
Neither did this malware developer mince terms about a distributed denial-of-assistance (DDoS) device they made available: fittingly enough, it was dubbed Web site Killah: a tool that carried guarantees of obtaining Unbeatable Costs, Rapid Attacks and Incredible Assist.
In circumstance there were being any doubters still left in the home, WeSupply’s discussion board posts also boost assistance for zero-day exploits and “Antivirus Bypassing”. WeSteal also delivers a “Victim tracker panel” that tracks Bacterial infections, “Leaving no doubt about the context,” the researchers say.
With These Very low, Low Charges, We Will have to Be Nuts
For all that badness, ComplexCodes charges a mere $24 for each thirty day period, $60 for a few months and $125 for one 12 months.
We really don’t essentially have to worry about ComplexCodes generating lease, even though. In an email on Friday, Dr. John Michener, main scientist of Casaba Security, observed that the Palo Alto Networks report reported that it is surprising that the criminal purchasers of the malware truly have faith in the malware to steal for them, and not for the authors of the malware alone.
On the contrary, Dr. Michener explained to Threatpost: The malware is probably established up to surreptitiously line its author’s pockets. “It’s really most likely that the malware starts thieving a sizeable fraction of the sufferer cash for the malware authors alternatively than for the malware purchasers immediately after a fair trial and screening interval,” he mentioned.
Here’s how it will work: WeSteal utilizes a straightforward but productive way to swipe cryptocurrency-obtaining addresses: It rummages via clipboards, browsing for strings matching Bitcoin and Ethereum wallet identifiers. When it finds them, WeSteal swaps out the legit wallet IDs in the clipboard with its very own IDs. When a target attempts to paste the swapped wallet ID for a transaction, the resources get whisked off to the attacker’s wallet.
Snooping on clipboard articles isn’t new, by any implies. It goes back again at least as much as 1999 with the launch of the Sub7 trojan application, which could check the contents of the clipboard and modify its contents “at the attacker’s whim,” in accordance to Randy Pargman, VP of Menace Searching and Counterintelligence at Binary Defense. “It’s so effortless for attackers to pull off this trick since it does not require any distinctive permissions for apps to study and improve the contents of the clipboard – immediately after all, that is what the clipboard is meant for, to trade text and graphics amongst programs,” he informed Threatpost in an email on Friday.
In December, RubyGems, an open up-source package deal repository and supervisor for the Ruby web programming language, took two program deals offline after they ended up observed to be laced with malware that pulled the identical trick. Just before that, in September 2020, we noticed KryptoCibule: clipboard-sniffing malware that spreads by means of pirated software program and activity torrents. Even “legitimate” applications do it, albeit not automatically for cryptocurrency mining for each se: For a person, in June 2020, TikTok experienced to lay off immediately after Apple’s privacy element exposed how it was snooping on clipboards.
How WeSteal Does Its Dirty Cryptocurrency-Thieving Do the job
In real crimeware-as-a-service manner, WeSteal is actually making use of a hosted command-and-manage (C2) assistance, which it ambitiously describes as a RAT Panel. The researchers didn’t uncover any distant entry trojan (RAT) attributes out there, though: for case in point, they did not uncover keylogging, credential exfiltration, or webcam hijacking capabilities.
The device is, even so, distributed as a Python-primarily based trojan in a script named “westeal.py”.
Quickly immediately after the researchers’ report was printed, they noticed that a RAT termed WeControl was also additional to the developer’s roster. As of Thursday, they have been even now organizing to analyze that just one.
How to Guard Your Cryptocurrency Wallet
As the price tag goes up and more persons jump on the bandwagon, we can hope the thieves to get the job done that a great deal tougher to steal it, Pargman notes. “The exorbitant value gains throughout quite a few cryptocurrencies this year are most likely to gas an ever expanding number of crypto-stealing attacks and cons. An additional issue that could include to this issue is the enhance in beginner crypto traders, who may possibly be a lot more inclined to malware, malicious apps and social engineering attacks,” he explained.
Dr. Michener recommends that all those who use cryptocurrency ought to also be making use of a hardware wallet and a devoted technique that’s made use of for nothing else. “Do not mix your banking technique with your particular system,” he claims: Assistance that’s most effective observe for regular on-line banking as properly as cryptocurrency exercise.
Be part of Threatpost for “Fortifying Your Organization Against Ransomware, DDoS & Cryptojacking Attacks” – a Live roundtable function on Wed, May 12 at 2:00 PM EDT. Sponsored by Zoho ManageEngine, Threatpost host Becky Bracken moderates an professional panel talking about most effective defense strategies for these 2021 threats. Inquiries and Reside audience participation encouraged. Be a part of the lively discussion and Sign-up Listed here for no cost.
Some parts of this article are sourced from:
threatpost.com


 Samsung Galaxy A52 5G: Can just ‘good’ be good enough?
Samsung Galaxy A52 5G: Can just ‘good’ be good enough?