U.S. cybersecurity and intelligence organizations have warned about China-based mostly condition-sponsored cyber actors leveraging network vulnerabilities to exploit general public and personal sector companies because at the very least 2020.
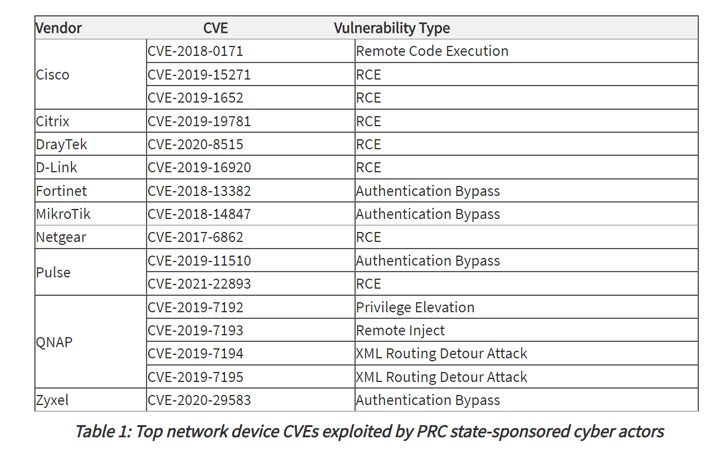
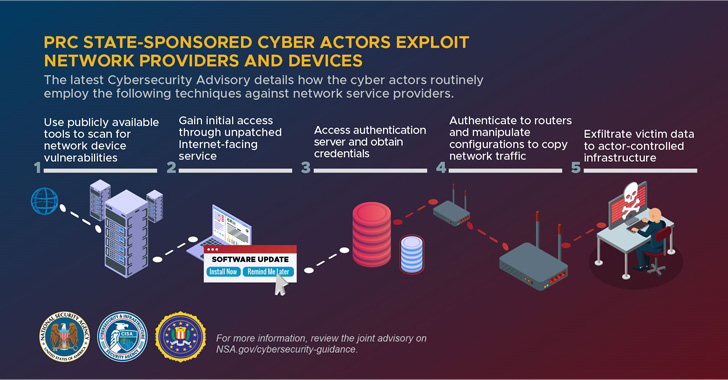
The popular intrusion strategies purpose to exploit publicly determined security flaws in network equipment these kinds of as Compact Office environment/Household Business office (SOHO) routers and Network Connected Storage (NAS) devices with the objective of getting further obtain to target networks.
In addition, the actors made use of these compromised devices as route command-and-management (C2) website traffic to crack into other targets at scale, the U.S. National Security Company (NSA), the Cybersecurity and Infrastructure Security Agency (CISA), and the Federal Bureau of Investigation (FBI) claimed in a joint advisory.

The perpetrators, apart from shifting their tactics in reaction to general public disclosures, are regarded to hire a mix of open-source and custom applications for reconnaissance and vulnerability scanning as perfectly as to obscure and blend their activity.
The attacks on their own are facilitated by accessing compromised servers, which the companies called hop details, from China-primarily based IP addresses, working with them to host C2 domains, email accounts, and communicate with the goal networks.
“Cyber actors use these hop details as an obfuscation approach when interacting with sufferer networks,” the companies famous, detailing the adversary’s sample of weaponizing flaws in telecommunications corporations and network service vendors.
Upon getting a foothold into the network via an unpatched internet-facing asset, the actors have been noticed obtaining qualifications for consumer and administrative accounts, followed by running router instructions to “surreptitiously route, seize, and exfiltrate website traffic out of the network to actor-controlled infrastructure.”
Final but not least, the attackers also modified or removed neighborhood log information to erase evidence of their activity to further conceal their presence and evade detection.
The organizations did not single out a unique threat actor, but famous that the findings reflect Chinese state-sponsored groups’ background of aggressively hanging critical infrastructure to steal sensitive information, emerging important technologies, intellectual residence, and personally identifiable info.
The disclosure also comes less than a month after the cybersecurity authorities disclosed the most routinely exploited initial entry vectors to breach targets, some of which contain misconfigured servers, weak password controls, unpatched program, and failure to block phishing tries.
“Entities can mitigate the vulnerabilities stated in this advisory by implementing the out there patches to their units, replacing conclude-of-everyday living infrastructure, and implementing a centralized patch administration system,” the businesses claimed.
Observed this posting attention-grabbing? Abide by THN on Facebook, Twitter and LinkedIn to read through more special articles we put up.
Some parts of this article are sourced from:
thehackernews.com

 Amazon knocks half off a Nintendo Switch Online and microSD card bundle
Amazon knocks half off a Nintendo Switch Online and microSD card bundle