TrickBot rises to leading threat in February, overtaking Emotet in Look at Point’s new index.
A significant destructive spam marketing campaign, along with the global takedown of Emotet, has vaulted the TrickBot trojan to the leading of the Examine Point’s record of the most popular malware among cybercriminals for February.
In January, TrickBot was rated third on Examine Point’s listing, and it was fourth general for 2020, though the No. 1 malware, Emotet, remained ascendant. But subsequent the around the world law-enforcement exertion to get down Emotet in January, cybercriminals have pivoted to TrickBot, the report described. Each strains are most typically used as very first-phase loaders for fetching extra malware.
“Even when a big menace is taken out, there are many other individuals that go on to pose a high risk on networks throughout the world, so businesses have to guarantee they have sturdy security systems in location to avoid their networks from getting compromised and reduce pitfalls,” in accordance to the Check out Stage report.
On the other hand, TrickBot hasn’t quite attained the similar stage of achievements as Emotet liked in advance of the crackdown, Check out Point’s Omer Dembinsky advised Threatpost.
“Although we nevertheless do not see an additional solitary threat achieving the scale of Emotet’s action, the general wide range and volume of possible threats continues to pose an exceptionally significant risk on networks and devices, and we have no question that the void still left by Emotet’s takedown will be crammed,” he claimed.
TrickBot Spam Marketing campaign
TrickBot was made use of in a spam campaign in February targeting people performing in the insurance and lawful industries, which tried to get them to simply click on a malicious .ZIP archive, the report included. Cybercriminals probably picked TrickBot as their new instrument of alternative mainly because of its history of achievements with other superior-profile strategies, like the 2020 attack on Universal Health Services, which used the malware to exfiltrate stolen info and provide Ryuk ransomware to the program, Test Stage included.
It is overall flexibility is an additional component of TrickBot which helps make it an attractive option for cybercriminals, Check out Place claimed.
Very first designed in 2016 as banking trojan, TrickBot’s hallmark is its capability to evolve modularly to increase its capabilities and evade detection. Final December, a new module of TrickBot known as “TrickBoot” emerged that authorized it to examine UEFI/BIOS firmware of the focused programs.
TrickBot Disrupted, But Recovered
TrickBot was also very seriously disrupted by just take-down motion led by Microsoft previous Oct in an hard work to control its distribute.
“We disrupted TrickBot as a result of a court docket buy we acquired, as effectively as specialized motion we executed in partnership with telecommunications suppliers close to the planet,” wrote Tom Burt, company vice president, Client Security & Belief, at Microsoft, at the time. “We have now minimize off vital infrastructure, so people operating TrickBot will no extended be in a position to initiate new infections or activate ransomware previously dropped into laptop or computer programs.”
Obviously, TrickBot was equipped to not just get well, but return with a vengeance.
The next-most common malware among risk actors in February, in accordance to Check out Position, was XMRing, which is at this time staying utilised in a marketing campaign using a bogus advertisement blocker to deliver both the XMRing cryptominer, as nicely as ransomware, for a double-whammy attack. In overall, the XMRing cryptominer/ransomware attack has infected extra than 20,000 people in the previous two months, Kaspersky warned in a current report.
Top Vulnerabilities, Mobile Threats
The most exploited vulnerability for February was “Web Server Uncovered Git Repository Facts Disclosure,” which impacted 48 p.c of organizations globally, Check out Point’s report explained. 2nd was “HTTP Headers Distant Code Execution (CVE-2020-13756),” which impacted 46 percent of all over the world orgs, and “MVPower DVR Distant Code Execution” was 3rd, affecting 45 per cent.
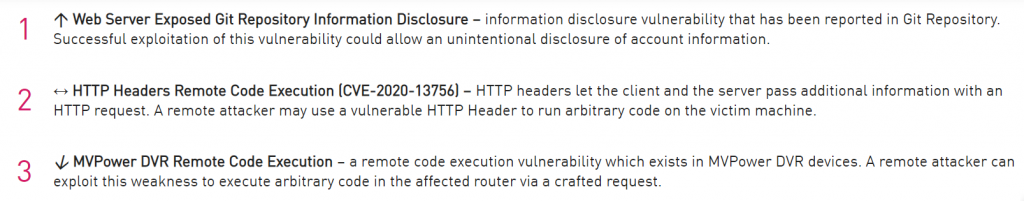
Resource: Look at Issue
No. 1 on the cellular malware listing is Hiddad, followed by xHelper destructive application with ad stuffer and the FurBall cellular distant accessibility trojan (MRAT).
Besides common patching and updates to secure from recognised vulnerabilities, Verify Stage suggests consumer instruction as the very best signifies of protecting any organization from cybersecurity breaches.
“Comprehensive training for all workers is vital, so they are outfitted with the techniques essential to identify the types of malicious email messages which distribute Trickbot and other malware,” Test Stage stated.
Look at out our free upcoming reside webinar events – exclusive, dynamic conversations with cybersecurity authorities and the Threatpost group:
- March 24: Economics of -Day Disclosures: The Good, Terrible and Unpleasant (Discover far more and sign-up!)
- April 21: Underground Marketplaces: A Tour of the Dark Financial system (Discover additional and sign up!)
Some parts of this article are sourced from:
threatpost.com


 Cybersecurity researchers build a better ‘canary trap’
Cybersecurity researchers build a better ‘canary trap’