A new Golang-based mostly information and facts stealer malware dubbed Titan Stealer is becoming advertised by danger actors by way of their Telegram channel.
“The stealer is capable of stealing a wide range of information from contaminated Windows equipment, together with credential information from browsers and crypto wallets, FTP client facts, screenshots, process facts, and grabbed files,” Uptycs security researchers Karthickkumar Kathiresan and Shilpesh Trivedi mentioned in a recent report.
Particulars of the malware have been to start with documented by cybersecurity researcher Will Thomas (@BushidoToken) in November 2022 by querying the IoT research engine Shodan.
Titan is available as a builder, enabling buyers to customise the malware binary to involve particular functionalities and the type of information and facts to be exfiltrated from a victim’s machine.
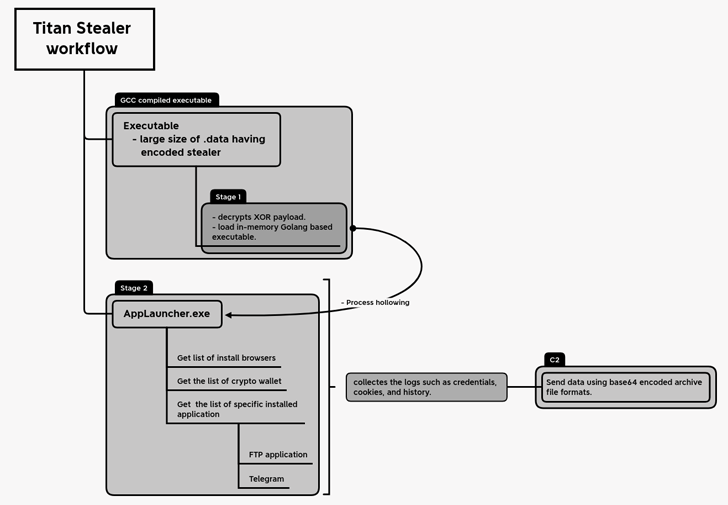
The malware, on execution, employs a procedure known as approach hollowing to inject the malicious payload into the memory of a legitimate system regarded as AppLaunch.exe, which is the Microsoft .NET ClickOnce Start Utility.
Some of the main web browsers qualified by Titan Stealer incorporate Google Chrome, Mozilla Firefox, Microsoft Edge, Yandex, Opera, Courageous, Vivaldi, 7 Star Browser, Iridium Browser, and other individuals. The crypto wallets singled out are Armory, Armory, Bytecoin, Coinomi, Edge Wallet, Ethereum, Exodus, Guarda, Jaxx Liberty, and Zcash.
It is really also capable of collecting the record of mounted apps on the compromised host and capturing data involved with the Telegram desktop application.
The amassed data is subsequently transmitted to a remote server underneath the attacker’s management as a Foundation64-encoded archive file. In addition, the malware will come with a web panel that permits adversaries to entry the stolen information.
The correct modus operandi utilised to distribute the malware is unclear as yet, but usually threat actors have leveraged a variety of approaches, this sort of as phishing, malicious adverts, and cracked computer software.
“One of the most important explanations [threat actors] may well be working with Golang for their facts stealer malware is simply because it lets them to very easily build cross-system malware that can operate on multiple working units, these kinds of as Windows, Linux, and macOS,” Cyble explained in its very own analysis of Titan Stealer.
“In addition, the Go compiled binary information are smaller in sizing, earning them extra complicated to detect by security program.”
The progress comes a tiny more than two months immediately after SEKOIA in-depth a different Go-centered malware referred to as Aurora Stealer that’s staying put to use by quite a few criminal actors in their strategies.
The malware is usually propagated by using lookalike internet sites of popular software package, with the very same domains actively up-to-date to host trojanized variations of different apps.
It has also been observed getting gain of a system recognised as padding to artificially inflate the size of the executables to as substantially as 260MB by incorporating random details so as to evade detection by antivirus program.
The conclusions appear close on the heels of a malware marketing campaign that has been noticed offering Raccoon and Vidar working with hundreds of fake internet sites masquerading as authentic program and game titles.
Crew Cymru, in an evaluation revealed before this thirty day period, noted that “Vidar operators have split their infrastructure into two areas 1 devoted to their typical customers and the other for the management crew, and also most likely premium / important consumers.”
Uncovered this short article fascinating? Adhere to us on Twitter and LinkedIn to study far more special written content we put up.
Some parts of this article are sourced from:
thehackernews.com


 Fake Money Apps Garner Millions of Android Downloads
Fake Money Apps Garner Millions of Android Downloads