The threat actors behind the Windows-based Grandoreiro banking trojan have returned in a global campaign since March 2024 following a law enforcement takedown in January.
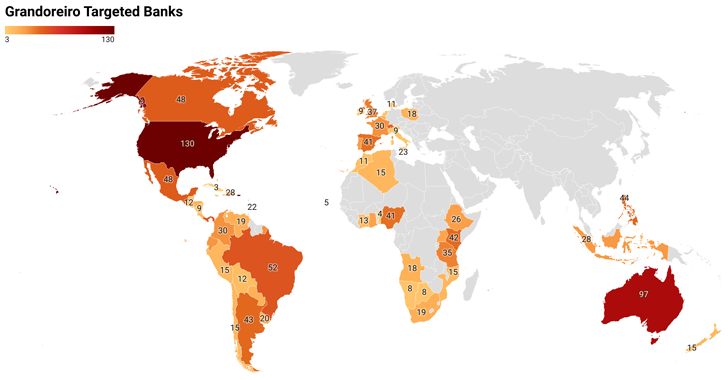
The large-scale phishing attacks, likely facilitated by other cybercriminals via a malware-as-a-service (MaaS) model, target over 1,500 banks across the world, spanning more than 60 countries in Central and South America, Africa, Europe, and the Indo-Pacific, IBM X-Force said.
While Grandoreiro is known primarily for its focus in Latin America, Spain, and Portugal, the expansion is likely a shift in strategy after attempts to shut down its infrastructure by Brazilian authorities.
Going hand-in-hand with the broader targeting footprint are significant improvements to the malware itself, which indicates active development.

“Analysis of the malware revealed major updates within the string decryption and domain generating algorithm (DGA), as well as the ability to use Microsoft Outlook clients on infected hosts to spread further phishing emails,” security researchers Golo Mühr and Melissa Frydrych said.
The attacks commence with phishing emails that instruct recipients to click on a link to view an invoice or make a payment depending on the nature of the lure and the government entity impersonated in the messages.
Users who end up clicking on the link are redirected to an image of a PDF icon, ultimately leading to the download of a ZIP archive with the Grandoreiro loader executable.
The custom loader is artificially inflated to more than 100 MB to bypass anti-malware scanning software. It’s also responsible for ensuring that the compromised host is not in a sandboxed environment, gathering basic victim data to a command-and-control (C2) server, and downloading and executing the main banking trojan.
It’s worth pointing out that the verification step is also done to skip systems geolocated to Russia, Czechia, Poland, and the Netherlands, as well as Windows 7 machines based in the U.S. with no antivirus installed.
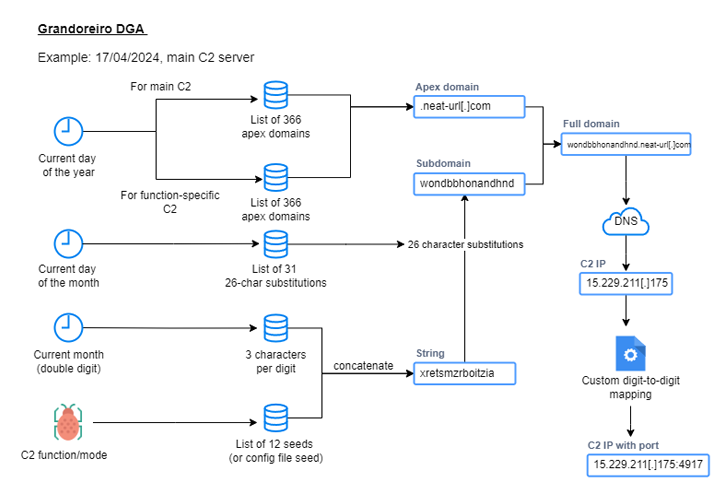
The trojan component begins its execution by establishing persistence via the Windows Registry, after which it employs a reworked DGA to establish connections with a C2 server to receive further instructions.

Grandoreiro supports a variety of commands that allow the threat actors to remotely commandeer the system, carry out file operations, and enable special modes, including a new module that gathers Microsoft Outlook data and abuses the victim’s email account to blast spam messages to other targets.
“In order to interact with the local Outlook client, Grandoreiro uses the Outlook Security Manager tool, a software used to develop Outlook add-ins,” the researchers said. “The main reason behind this is that the Outlook Object Model Guard triggers security alerts if it detects access on protected objects.”
“By using the local Outlook client for spamming, Grandoreiro can spread through infected victim inboxes via email, which likely contributes to the large amount of spam volume observed from Grandoreiro.”
Found this article interesting? Follow us on Twitter and LinkedIn to read more exclusive content we post.
Some parts of this article are sourced from:
thehackernews.com


 Kinsing Hacker Group Exploits More Flaws to Expand Botnet for Cryptojacking
Kinsing Hacker Group Exploits More Flaws to Expand Botnet for Cryptojacking