An unknown risk actor has been joined to a new Android malware strain that options the skill to root smartphones and consider total regulate in excess of contaminated smartphones whilst at the same time having techniques to evade detection.
The malware has been named “AbstractEmu” owing to its use of code abstraction and anti-emulation checks to steer clear of operating though below investigation. Notably, the worldwide cell marketing campaign is engineered to concentrate on people and infect as numerous units as attainable indiscriminately.

Lookout Risk Labs said it discovered a full of 19 Android apps that posed as utility applications and process instruments like password professionals, income professionals, app launchers, and data saving apps, seven of which contained the rooting features. Only just one of the rogue apps, identified as Lite Launcher, designed its way to the official Google Participate in Store, attracting a complete of 10,000 downloads before it was purged.
The applications are said to have been prominently dispersed by way of third-get together outlets these as the Amazon Appstore and the Samsung Galaxy Retail outlet, as perfectly as other lesser-identified marketplaces like Aptoide and APKPure.
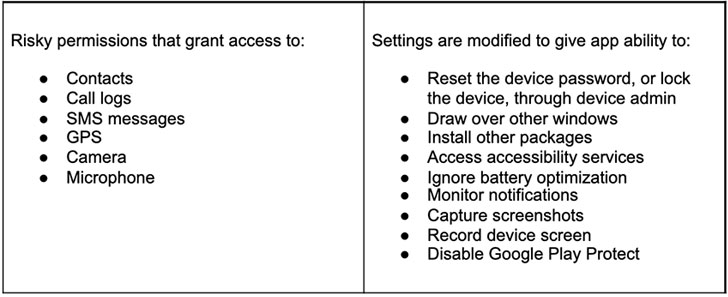
“While scarce, rooting malware is really hazardous. By making use of the rooting procedure to acquire privileged accessibility to the Android working system, the risk actor can silently grant themselves unsafe permissions or put in extra malware — ways that would generally require person interaction,” Lookout researchers reported. “Elevated privileges also give the malware obtain to other apps’ delicate data, anything not possible below ordinary situation.”
When put in, the attack chain is developed to a person of 5 exploits for older Android security flaws that would allow it to attain root permissions and take around the machine, extract sensitive facts, and transmit to a distant attack-controlled server —
- CVE-2015-3636 (PongPongRoot)
- CVE-2015-1805 (iovyroot)
- CVE-2019-2215 (Qu1ckr00t)
- CVE-2020-0041, and
- CVE-2020-0069
Lookout attributed the mass dispersed rooting malware marketing campaign to a “nicely-resourced group with money drive,” with telemetry knowledge revealing that Android device customers in the U.S. ended up the most impacted. The best objective of the infiltrations stays unclear as nonetheless.
“Rooting Android or jailbreaking iOS units are continue to the most invasive ways to totally compromise a mobile machine,” the researchers claimed, including “mobile gadgets are great equipment for cyber criminals to exploit, as they have countless functionalities and keep an enormous amount of money of sensitive information.”
Discovered this post intriguing? Observe THN on Fb, Twitter and LinkedIn to examine more exceptional information we put up.
Some parts of this article are sourced from:
thehackernews.com


 FCC proposes text support for the National Suicide Prevention Lifeline
FCC proposes text support for the National Suicide Prevention Lifeline