A destructive actor has been linked to a cloud credential thieving campaign in June 2023 that is focused on Azure and Google Cloud Platform (GCP) solutions, marking the adversary’s enlargement in focusing on outside of Amazon Web Services (AWS).
The results occur from SentinelOne and Permiso, which mentioned the “campaigns share similarity with tools attributed to the notorious TeamTNT cryptojacking crew,” whilst it emphasised that “attribution stays difficult with script-dependent instruments.”
They also overlap with an ongoing TeamTNT marketing campaign disclosed by Aqua referred to as Silentbob that leverages misconfigured cloud products and services to drop malware as element of what is explained to be a tests energy, when also linking SCARLETEEL attacks to the menace actor, citing infrastructure commonalities.
“TeamTNT is scanning for credentials across multiple cloud environments, such as AWS, Azure, and GCP,” Aqua observed.
The assaults, which solitary out community-struggling with Docker circumstances to deploy a worm-like propagation module, are a continuation of an intrusion set that previously focused Jupyter Notebooks in December 2022.
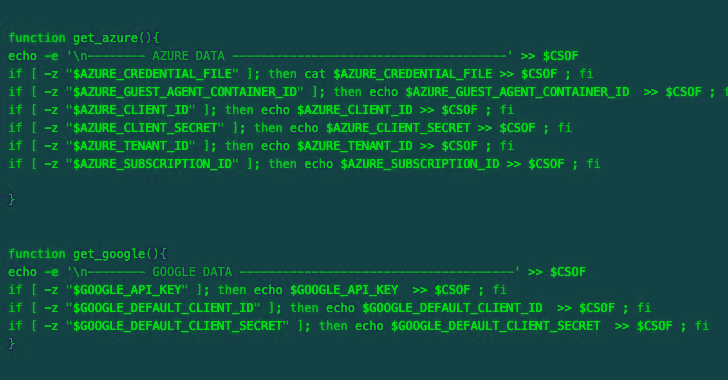
As quite a few as eight incremental variations of the credential harvesting script have been found among June 15, 2023, and July 11, 2023, indicating an actively evolving campaign.
The more recent versions of the malware are created to acquire qualifications from AWS, Azure, Google Cloud Platform, Censys, Docker, Filezilla, Git, Grafana, Kubernetes, Linux, Ngrok, PostgreSQL, Redis, S3QL, and SMB. The harvested credentials are then exfiltrated to a remote server below the danger actor’s control.
Future WEBINARShield Versus Insider Threats: Learn SaaS Security Posture Management
Worried about insider threats? We’ve received you lined! Be part of this webinar to explore functional strategies and the insider secrets of proactive security with SaaS Security Posture Management.
Join Now
SentinelOne mentioned the credentials collection logic and the files specific bears similarities to a Kubelet-targeting campaign undertaken by TeamTNT in September 2022.
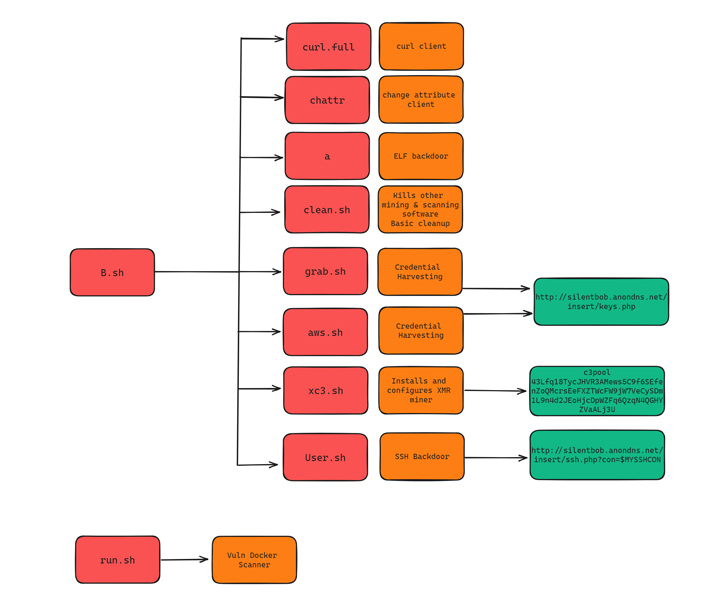
Together with the shell script malware, the danger actor has also been observed distributing a Golang-based mostly ELF binary that acts as a scanner to propagate the malware to susceptible targets. The binary further more drops a Golang network scanning utility called Zgrab.
“This campaign demonstrates the evolution of a seasoned cloud actor with familiarity across quite a few systems,” security scientists Alex Delamotte, Ian Ahl, and Daniel Bohannon mentioned. “The meticulous consideration to depth implies the actor has evidently skilled a great deal of demo and error.”
“This actor is actively tuning and improving upon their applications. Dependent on the tweaks observed throughout the earlier numerous months, the actor is very likely getting ready for larger sized scale strategies.”
Found this post exciting? Comply with us on Twitter and LinkedIn to browse extra unique content we write-up.
Some parts of this article are sourced from:
thehackernews.com

 New SOHO Router Botnet AVrecon Spreads to 70,000 Devices Across 20 Countries
New SOHO Router Botnet AVrecon Spreads to 70,000 Devices Across 20 Countries