A new malware pressure has been observed covertly focusing on small business office/house business (SOHO) routers for far more than two years, infiltrating around 70,000 equipment and making a botnet with 40,000 nodes spanning 20 nations.
Lumen Black Lotus Labs has dubbed the malware AVrecon, producing it the 3rd this sort of pressure to target on SOHO routers right after ZuoRAT and HiatusRAT above the past yr.
“This would make AVrecon a single of the biggest SOHO router-focusing on botnets ever noticed,” the corporation explained. “The function of the campaign appears to be the creation of a covert network to quietly enable a assortment of prison routines from password spraying to digital promoting fraud.”
A the greater part of the bacterial infections are positioned in the U.K. and the U.S., followed by Argentina, Nigeria, Brazil, Italy, Bangladesh, Vietnam, India, Russia, and South Africa, among the other individuals.
AVrecon was initial highlighted by Kaspersky senior security researcher Ye (Seth) Jin in May possibly 2021, indicating that the malware has managed to keep away from detection until finally now.
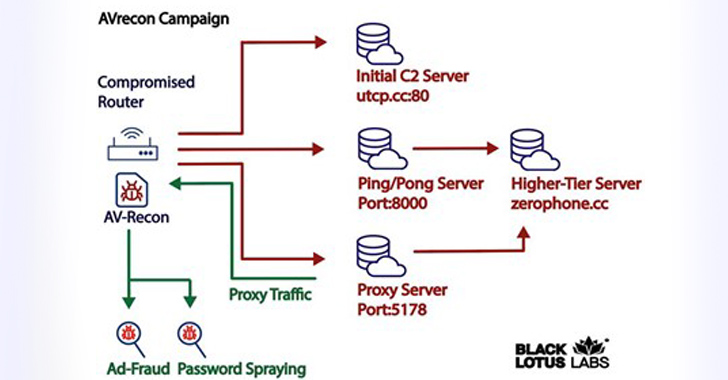
In the attack chain comprehensive by Lumen, a effective an infection is adopted by enumerating the victim’s SOHO router and exfiltrating that data back to an embedded command-and-regulate (C2) server.
It also checks if other circumstances of malware are previously operating on the host by seeking for current procedures on port 48102 and opening a listener on that port. A procedure certain to that port is terminated.

The up coming phase involves the compromised process setting up call with a different server, referred to as the secondary C2 server, to await further more commands. Lumen stated it discovered 15 these special servers that have been energetic since at the very least October 2021.
It’s really worth noting that tiered C2 infrastructure is widespread between infamous botnets like Emotet and QakBot.
Impending WEBINARShield In opposition to Insider Threats: Grasp SaaS Security Posture Administration
Worried about insider threats? We have obtained you lined! Sign up for this webinar to explore realistic strategies and the secrets and techniques of proactive security with SaaS Security Posture Management.
Sign up for These days
AVrecon is published in the C programming language, creating it quick to port the malware for various architectures. What is far more, a very important motive why this kind of attacks get the job done is since they leverage infrastructure dwelling on the edge that ordinarily lacks support for security remedies.
Evidence collected so far points to the botnet being employed for clicking on many Fb and Google ads, and to interact with Microsoft Outlook. This probable implies a two-pronged work to carry out advertising fraud and details exfiltration.
“The method of attack seems to focus predominantly on stealing bandwidth – without the need of impacting finish-users – in order to generate a residential proxy company to assist launder destructive activity and keep away from attracting the exact same stage of attention from Tor-concealed providers or commercially obtainable VPN providers,” the researchers stated.
Discovered this short article intriguing? Observe us on Twitter and LinkedIn to browse far more distinctive articles we article.
Some parts of this article are sourced from:
thehackernews.com

 Zimbra Warns of Critical Zero-Day Flaw in Email Software Amid Active Exploitation
Zimbra Warns of Critical Zero-Day Flaw in Email Software Amid Active Exploitation