As many as seven destructive Android applications learned on the Google Engage in Retail store masqueraded as antivirus options to deploy a banking trojan termed SharkBot.
“SharkBot steals qualifications and banking information,” Check Place scientists Alex Shamshur and Raman Ladutska mentioned in a report shared with The Hacker Information. “This malware implements a geofencing function and evasion strategies, which will make it stand out from the rest of malwares.”

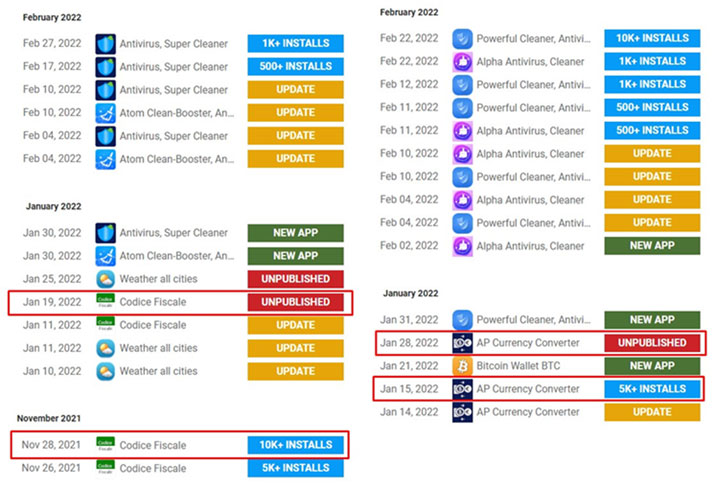
Particularly, the malware is designed to ignore consumers from China, India, Romania, Russia, Ukraine, and Belarus. The rogue applications are explained to have been mounted additional than 15,000 situations prior to their removal, with most of the victims located in Italy and the U.K.
The report enhances previous findings from NCC Group, which identified the bankbot posing as antivirus apps to have out unauthorized transactions by way of Automated Transfer Units (ATS).
SharkBot requires advantage of the Accessibility Companies permissions to present bogus overlay windows on best of genuine banking applications. Consequently when unsuspecting users enter their usernames and passwords in the windows that mimic benign credential enter varieties, the captured details is sent to a destructive server.

One particular new notable characteristic of SharkBot is its capability to car reply to notifications from Fb Messenger and WhatsApp to distribute a phishing hyperlink to the antivirus application, hence propagating the malware in a worm-like vogue. A related element was included in FluBot previously this February.
The newest results appear as Google took techniques to banish 11 applications from the Play Retail outlet on March 25 after they had been caught incorporating an invasive SDK to discreetly harvest consumer facts, like specific spot information and facts, email and phone quantities, nearby units, and passwords.
“What’s also noteworthy in this article is that the danger actors push messages to victims that contains destructive hyperlinks, which sales opportunities to widespread adoption,” Alexander Chailytko, cyber security, research and innovation supervisor at Check out Point Software, mentioned.
“All in all, the use of push-messages by the risk actors requesting an respond to from users is an strange spreading technique.”
Observed this post exciting? Adhere to THN on Fb, Twitter and LinkedIn to browse far more unique written content we publish.
Some parts of this article are sourced from:
thehackernews.com


 Meta won't host its F8 developer conference this year
Meta won't host its F8 developer conference this year