A new information wiper malware has been observed deployed from an unnamed Ukrainian government network, a working day following damaging cyber attacks struck various entities in the country preceding the begin of Russia’s army invasion.
Slovak cybersecurity organization ESET dubbed the new malware “IsaacWiper,” which it said was detected on February 24 in an group that was not affected by HermeticWiper (aka FoxBlade), yet another facts wiping malware that qualified many companies on February 23 as element of a sabotage procedure aimed at rendering the equipment inoperable.
Further more assessment of the HermeticWiper attacks, which contaminated at least 5 Ukrainian businesses, have exposed a worm constituent that propagates the malware throughout the compromised network and a ransomware module that acts as a “distraction from the wiper assaults,” corroborating a prior report from Symantec.
“These destructive attacks leveraged at least three parts: HermeticWiper for wiping the facts, HermeticWizard for spreading on the nearby network, and HermeticRansom performing as a decoy ransomware,” the organization stated.
In a separate analysis of the new Golang-based mostly ransomware, Russian cybersecurity corporation Kaspersky, which codenamed the malware “Elections GoRansom,” characterised it as a past-minute operation, introducing it was “probably applied as a smokescreen for the HermeticWiper attack owing to its non-sophisticated fashion and inadequate implementation.”
As an anti-forensic measure, HermeticWiper is also made to hinder analysis by erasing by itself from the disk by overwriting its personal file with random bytes.
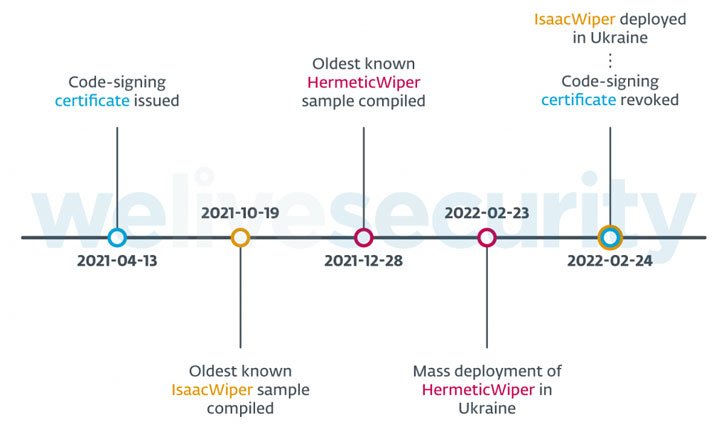
ESET claimed it did not find “any tangible connection” to attribute these attacks to a recognised threat actor, with the malware artifacts implying that the intrusions experienced been planned for various months, not to point out the simple fact that the specific entities suffered compromises properly in advance to the wiper’s deployment.
“This is dependent on several specifics: the HermeticWiper PE compilation timestamps, the oldest becoming December 28, 2021 the code-signing certificate issue date of April 13, 2021 and the deployment of HermeticWiper via the default area plan in at minimum one occasion, suggesting the attackers had prior entry to a single of that victim’s Energetic Directory servers,” explained Jean-Ian Boutin, ESET head of threat analysis.

Also not known are the preliminary accessibility vectors utilized to deploy both of those the wipers, while it is really suspected that the attackers leveraged instruments like Impacket and RemCom, a remote access software package, for lateral movement and malware distribution.
Also, IsaacWiper shares no code-amount overlaps with HermeticWiper and is considerably a lot less advanced, even as it sets out to enumerate all the bodily and sensible drives before continuing to have out its file wiping functions.
“On February 25, 2022, attackers dropped a new version of IsaacWiper with debug logs,” the researchers said. “This may well suggest that the attackers ended up not able to wipe some of the specific devices and extra log messages to have an understanding of what was occurring.”
Located this write-up attention-grabbing? Abide by THN on Facebook, Twitter and LinkedIn to read through extra unique content we put up.
Some parts of this article are sourced from:
thehackernews.com


 Ukraine raises over $13 million in crypto to help fight Russian invasion
Ukraine raises over $13 million in crypto to help fight Russian invasion