A recently disclosed vulnerability influencing Intel processors could be abused by an adversary to obtain entry to delicate data stored within enclaves and even run arbitrary code on vulnerable programs.
The vulnerability (CVE-2021-0186, CVSS rating: 8.2) was found out by a group of teachers from ETH Zurich, the Countrywide University of Singapore, and the Chinese Countrywide College of Protection Technology in early May 2021, who made use of it to phase a private information disclosure attack named “SmashEx” that can corrupt personal data housed in the enclave and split its integrity.

Launched with Intel’s Skylake processors, SGX (short for Application Guard eXtensions) allows builders to operate selected application modules in a completely isolated safe compartment of memory, called an enclave or a Reliable Execution Surroundings (TEE), which is built to be secured from procedures managing at better privilege levels like the functioning method. SGX ensures that details is safe even if a computer’s functioning method has been tampered with or is less than attack.
“For normal functioning, the SGX style allows the OS to interrupt the enclave execution via configurable components exceptions at any point,” the scientists outlined. “This aspect enables enclave runtimes (e.g., Intel SGX SDK and Microsoft Open Enclave) to aid in-enclave exception or signal handling, but it also opens up enclaves to re-entrancy bugs. SmashEx is an attack which exploits enclave SDKs which do not carefully cope with re-entrancy in their exceptional handling properly.”
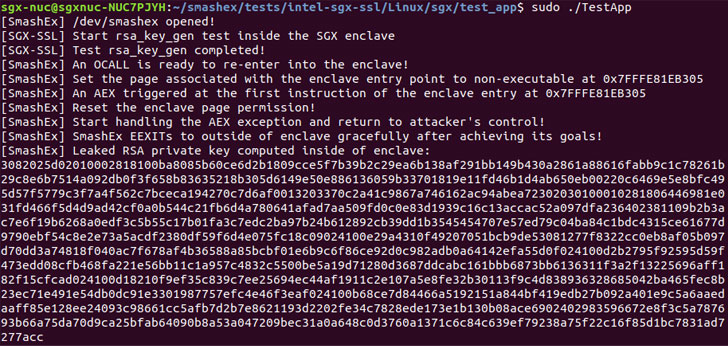
It’s well worth noting that an enclave could also have Outside Phone calls, or OCALLS, which make it possible for enclave functions to call out to the untrusted software and then return to the enclave. But when the enclave is also managing in-enclave exceptions (e.g., timer interrupt or division-by-zero), the vulnerability supplies a temporary window for a local attacker to hijack the regulate stream of execution by injecting an asynchronous exception instantly right after the enclave is entered.
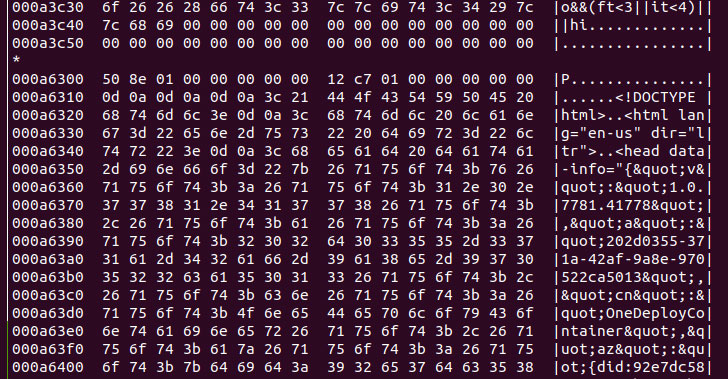
Armed with this ability, the adversary can then corrupt the in-enclave memory to leak sensitive details these types of as RSA non-public keys or execute malicious code.
Because SmashEx affects runtimes that aid in-enclave exception handling, the scientists pointed out that “this kind of OCALL return flow and the exception managing flow should really be created with treatment to guarantee that they interleave properly,” and that “when the OCALL return movement is interrupted, the enclave should really be in a regular point out for the exception managing flow to development accurately, and when the exception handling circulation completes, the enclave state must also be ready for the enclave to resume.”

Intel has because produced software program updates to mitigate this vulnerability with SGX SDK versions 2.13 and 2.14 for Windows and Linux respectively. Microsoft, for its portion, addressed the issue (CVE-2021-33767) in its July 2021 Patch Tuesday updates with Open Enclave model .17.1 of the SDK. The analysis team’s results are anticipated to be offered following month at the ACM Meeting on Personal computer and Communications Security.
“Asynchronous exception managing is a commodity features for authentic-entire world programs nowadays, which are more and more using enclaves,” the researchers explained, adding the study highlights “the importance of furnishing atomicity guarantees at the OS-enclave interface for this kind of exceptions.”
Found this write-up fascinating? Abide by THN on Fb, Twitter and LinkedIn to go through a lot more exclusive information we write-up.
Some parts of this article are sourced from:
thehackernews.com


 81% of UK Healthcare Organizations Hit by Ransomware in Last Year
81% of UK Healthcare Organizations Hit by Ransomware in Last Year