The flaws are in the ubiquitous open-resource PJSIP multimedia interaction library, made use of by the Asterisk PBX toolkit that is identified in a huge quantity of VoIP implementations.
WhatsApp and BlueJeans are just two of the world’s most well-liked communication apps that are employing an open up-supply library riddled with newfound security holes.
One particular detail this open up-resource, flawed library shares with the Apache Log4J logging library fiasco that started out in December: It’s ubiquitous.
The library, PJSIP – an open-supply multimedia interaction library – is also utilized by Asterisk. Asterisk is an organization-course, open up-source PBX (non-public branch exchange) toolkit which is applied in voice-above-IP (VoIP) solutions in a significant amount of implementations.
In accordance to the Asterisk web site, the program is downloaded 2M times each year and operates on 1M servers in 170 countries. Asterisk powers IP PBX systems, VoIP gateways and conference servers, and it’s used by SMBs, enterprises, simply call facilities, carriers and governments.
On Monday, devops system service provider JFrog Security disclosed five memory-corruption vulnerabilities in PJSIP, which provides an API that can be used by IP telephony programs this kind of as voice-more than-IP (VoIP) telephones and conference applications.
An attacker who productively triggers the vulnerabilities can flip the change on remote code execution (RCE) in an software that utilizes the PJSIP library, JFrog scientists discussed.
Subsequent JFrog’s disclosure, PJSIP’s maintainers have fixed the five CVEs, depicted under.
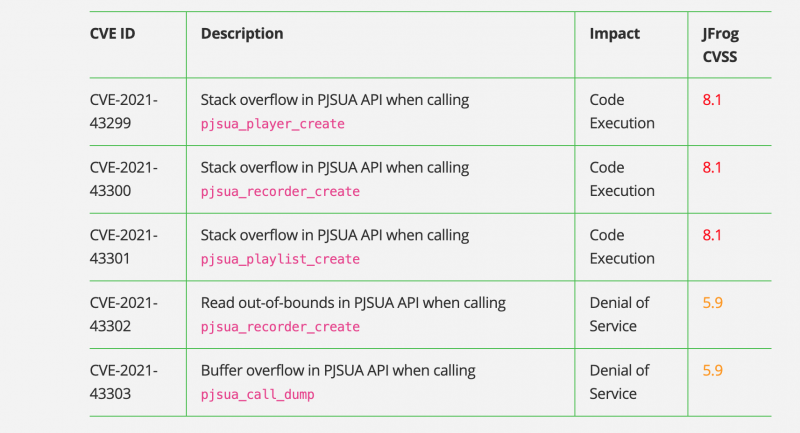
The disclosed PJSIP security vulnerabilities. Source: JFrog Security.
What Went Erroneous
In its complex breakdown, JFrog researchers discussed that the PJSIP framework presents a library named PJSUA that provides an API for SIP apps.
“The basic PJSUA APIs are also wrapped by item-oriented APIs. PJSUA offers a loaded Media Manipulation API, where by we have spotted the [five] vulnerabilities,” they explained.
A few of the flaws are stack overflow vulnerabilities that can lead to RCE and which are rated 8.1 on the CVSS severity-rating scale.
The remaining two involve a examine out-of-bounds vulnerability and a buffer overflow weak spot in the PJSUA API, each of which can guide to denial-of-services (DoS) and equally of which are rated at CVSS 5.9.
Vulnerable Assignments
JFrog mentioned that jobs that use the PJSIP library ahead of version 2.12 and which move attacker-controlled arguments to any of the subsequent APIs are vulnerable:
- pjsua_participant_generate – filename argument will have to be attacker-controlled
- pjsua_recorder_produce – filename argument need to be attacker-controlled
- pjsua_playlist_build – file_names argument must be (partially) attacker-controlled
- pjsua_get in touch with_dump – buffer argument capability ought to be scaled-down than 128 bytes
JFrog proposed upgrading PJSIP to version 2.12 to handle the vulnerabilities.
Not the To start with Time
Pockmarks in PJSIP and other typical videoconferencing architecture implementations are nothing new. In August 2018, Google Project Zero researcher Natalie Silvanovich disclosed critical vulnerabilities in most of the typical ones, which include WebRTC (utilised by Chrome, Safari, Firefox, Fb Messenger, Signal and many others), PJSIP (which, yet again, is utilized by WhatsApp, BlueJeans and hundreds of thousands of implementations of Asterisk) and Apple’s proprietary library for FaceTime.
“If exploited, these vulnerabilities would have allow attackers crash applications working with the implementation, by just positioning a video clip simply call,” mentioned Ronen Slavin, then head of study at Reason Cybersecurity and presently the co-founder and CTO at the resource code manage, detection, and response system Cycode, back in 2019. “This would have then brought on a memory heap overflow which could make it possible for the attacker to choose over the victim’s video clip calling account.”
Apps this sort of as Skype, Google Hangouts and WhatsApp “have built it straightforward to have meaningful facial area-to-face interactions throughout between two factors any where on the world,” he wrote.
It was accurate then. But due to the fact, the pandemic has been fuel on the hearth when it will come to virtual connections: all the additional cause to heed JFrog’s advice and patch ASAP.
Going to the cloud? Find emerging cloud-security threats along with reliable advice for how to defend your assets with our Absolutely free downloadable Ebook, “Cloud Security: The Forecast for 2022.” We check out organizations’ major threats and worries, finest tactics for defense, and information for security achievement in these kinds of a dynamic computing atmosphere, together with handy checklists.
Some parts of this article are sourced from:
threatpost.com

 Green chemistry: Scientists develop new process for more eco-friendly liquid crystals
Green chemistry: Scientists develop new process for more eco-friendly liquid crystals