The flaws are in the ubiquitous open-supply PJSIP multimedia communication library, used by the Asterisk PBX toolkit that is discovered in a large number of VoIP implementations.
Some of the world’s most well-known conversation apps are utilizing an open up-resource library riddled with newfound security holes.
1 point this open-supply, flawed library shares with the Apache Log4J logging library fiasco that begun in December: It is ubiquitous.
The library, PJSIP – an open-source multimedia conversation library – is made use of by Asterisk. Asterisk is an enterprise-class, open-resource PBX (private branch trade) toolkit that is made use of in voice-more than-IP (VoIP) products and services in a enormous quantity of implementations.
In accordance to the Asterisk web-site, the software package is downloaded 2M times per year and operates on 1M servers in 170 nations. Asterisk powers IP PBX methods, VoIP gateways and meeting servers, and it is employed by SMBs, enterprises, contact facilities, carriers and governments.
On Monday, devops system provider JFrog Security disclosed five memory-corruption vulnerabilities in PJSIP, which materials an API that can be applied by IP telephony programs these types of as VoIP phones and convention apps.
An attacker who properly triggers the vulnerabilities can flip the switch on distant code execution (RCE) in an application that utilizes the PJSIP library, JFrog scientists discussed.
Next JFrog’s disclosure, PJSIP’s maintainers have fastened the five CVEs, depicted under.
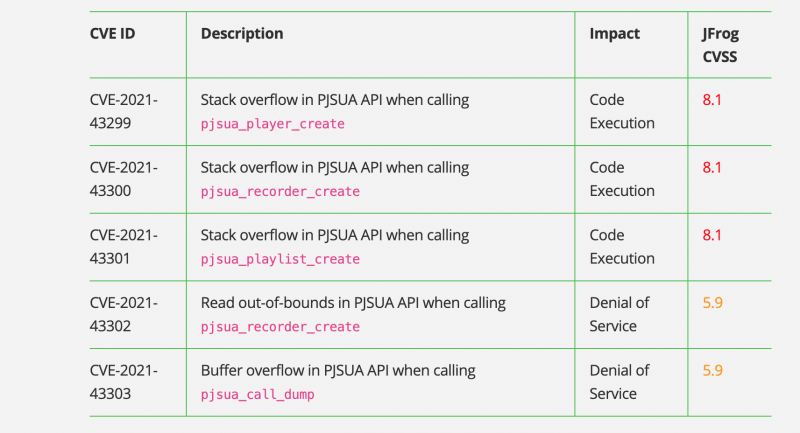
The disclosed PJSIP security vulnerabilities. Supply: JFrog Security.
What Went Wrong
In its technological breakdown, JFrog researchers spelled out that the PJSIP framework gives a library named PJSUA that supplies an API for SIP applications.
“The standard PJSUA APIs are also wrapped by item-oriented APIs. PJSUA features a prosperous Media Manipulation API, the place we have spotted the [five] vulnerabilities,” they reported.
3 of the flaws are stack overflow vulnerabilities that can direct to RCE and which are rated 8.1 on the CVSS severity-score scale.
The remaining two contain a go through out-of-bounds vulnerability and a buffer overflow weak point in the PJSUA API, both of which can lead to denial-of-assistance (DoS) and equally of which are rated at CVSS 5.9.
Vulnerable Projects
JFrog reported that projects that use the PJSIP library right before variation 2.12 and which go attacker-managed arguments to any of the next APIs are vulnerable:
- pjsua_participant_create – filename argument have to be attacker-controlled
- pjsua_recorder_develop – filename argument have to be attacker-managed
- pjsua_playlist_produce – file_names argument will have to be (partly) attacker-controlled
- pjsua_connect with_dump – buffer argument capability ought to be smaller than 128 bytes
JFrog encouraged upgrading PJSIP to version 2.12 to address the vulnerabilities.
Not the 1st Time
Pockmarks in PJSIP and other popular videoconferencing architecture implementations are nothing new. In August 2018, Google Job Zero researcher Natalie Silvanovich disclosed critical vulnerabilities in most of the frequent types, including WebRTC (utilized by Chrome, Safari, Firefox, Fb Messenger, Sign and some others), PJSIP (which, yet again, is used in hundreds of thousands of implementations of Asterisk) and Apple’s proprietary library for FaceTime.
“If exploited, such vulnerabilities would have permit attackers crash applications applying the implementation, by basically placing a video connect with,” noted Ronen Slavin, then head of investigation at Rationale Cybersecurity and at the moment the co-founder and CTO at the resource code control, detection, and reaction platform Cycode, back in 2019. “This would have then induced a memory heap overflow which could allow for the attacker to choose above the victim’s movie contacting account.”
Applications this sort of as Skype, Google Hangouts and WhatsApp “have produced it quick to have significant facial area-to-confront interactions across in between two details everywhere on the world,” he wrote.
It was legitimate then. But because, the pandemic has been fuel on the fire when it arrives to virtual connections: all the extra reason to heed JFrog’s suggestions and patch ASAP.
030222 08:25 UPDATE: A WhatsApp consultant instructed Threatpost that the application does not use the PJSIP library, opposite to unique reporting.
Relocating to the cloud? Learn emerging cloud-security threats alongside with sound advice for how to protect your property with our Free downloadable E-book, “Cloud Security: The Forecast for 2022.” We explore organizations’ leading risks and worries, finest methods for protection, and information for security success in these kinds of a dynamic computing setting, which include helpful checklists.
Some parts of this article are sourced from:
threatpost.com

 Green chemistry: Scientists develop new process for more eco-friendly liquid crystals
Green chemistry: Scientists develop new process for more eco-friendly liquid crystals