The Pakistan-based superior persistent menace (APT) actor regarded as Clear Tribe utilized a two-component authentication (2FA) tool utilized by Indian government businesses as a ruse to provide a new Linux backdoor called Poseidon.
“Poseidon is a 2nd-stage payload malware involved with Transparent Tribe,” Uptycs security researcher Tejaswini Sandapolla reported in a complex report released this 7 days.
“It is a typical-goal backdoor that gives attackers with a vast variety of abilities to hijack an contaminated host. Its functionalities include things like logging keystrokes, using display screen captures, uploading and downloading information, and remotely administering the procedure in various strategies.”
Clear Tribe is also tracked as APT36, Procedure C-Key, PROJECTM, and Mythic Leopard, and has a track file of targeting Indian governing administration companies, armed forces staff, protection contractors, and academic entities.
It has also frequently leveraged trojanized versions of Kavach, the Indian governing administration-mandated 2FA program, to deploy a assortment of malware, such as CrimsonRAT and LimePad to harvest useful info.
A different phishing marketing campaign detected late final year took edge of weaponized attachments to download malware intended to exfiltrate databases files established by the Kavach application.
The newest set of assaults entail the use of a backdoored version of Kavach to concentrate on Linux people functioning for Indian government businesses, indicating tries created by the menace actor to increase its attack spectrum outside of Windows and Android ecosystems.
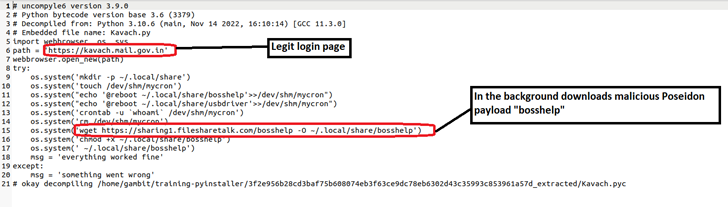
“When a user interacts with the destructive version of Kavach, the real login webpage is exhibited to distract them,” Sandapolla stated. “Meanwhile, the payload is downloaded in the track record, compromising the user’s program.”
Future WEBINARMaster the Artwork of Dark Web Intelligence Accumulating
Find out the artwork of extracting menace intelligence from the dark web – Join this pro-led webinar!
Conserve My Seat!
The setting up stage of the infections is an ELF malware sample, a compiled Python executable that is engineered to retrieve the 2nd-phase Poseidon payload from a distant server.
The cybersecurity agency mentioned that the phony Kavach applications are largely dispersed by rogue internet sites that are disguised as respectable Indian federal government web-sites. This features www.ksboard[.]in and www.rodra[.]in.
With social engineering being the key attack vector employed by Transparent Tribe, end users operating within the Indian government are advised to double-look at URLs acquired in emails ahead of opening them.
“Repercussions of this APT36 attack could be significant, main to loss of delicate facts, compromised methods, money losses, and reputational damage,” Sandapolla explained.
Located this write-up appealing? Stick to us on Twitter and LinkedIn to browse much more exclusive written content we post.
Some parts of this article are sourced from:
thehackernews.com


 Uncovering (and Understanding) the Hidden Risks of SaaS Apps
Uncovering (and Understanding) the Hidden Risks of SaaS Apps