OpenAI on Friday disclosed that a bug in the Redis open up supply library was accountable for the publicity of other users’ personal details and chat titles in the upstart’s ChatGPT service earlier this week.
The glitch, which came to mild on March 20, 2023, enabled specific customers to check out quick descriptions of other users’ conversations from the chat historical past sidebar, prompting the company to briefly shut down the chatbot.
“It really is also possible that the to start with message of a freshly-created conversation was obvious in someone else’s chat historical past if equally people had been lively about the exact same time,” the organization explained.
The bug, it even further added, originated in the redis-py library, leading to a circumstance where by canceled requests could cause connections to be corrupted and return unanticipated facts from the database cache, in this circumstance, facts belonging to an unrelated consumer.
To make issues worse, the San Francisco-centered AI exploration firm said it released a server-aspect transform by oversight that led to a surge in ask for cancellations, thus upping the mistake price.
When the challenge has considering that been dealt with, OpenAI observed that the issue may possibly have experienced a lot more implications somewhere else, likely revealing payment-related information of 1.2% of the ChatGPT Plus subscribers on March 20 amongst 1-10 a.m. PT.
This provided one more active user’s to start with and final identify, email handle, payment handle, the last four digits (only) of a credit rating card number, and credit score card expiration date. It emphasised that entire credit rating card figures have been not uncovered.
The company mentioned it has achieved out to affected buyers to notify them of the inadvertent leak. It also explained it “extra redundant checks to assure the details returned by our Redis cache matches the requesting consumer.”
OpenAI Fixes Critical Account Takeover Flaw
In yet another caching-similar issue, the business also dealt with a critical account takeover vulnerability that could be exploited to seize handle of a different user’s account, perspective their chat heritage, and access billing information and facts without having their know-how.
WEBINARDiscover the Concealed Risks of Third-Celebration SaaS Apps
Are you knowledgeable of the risks associated with 3rd-party app access to your firm’s SaaS apps? Join our webinar to discover about the styles of permissions currently being granted and how to limit risk.
RESERVE YOUR SEAT
The flaw, which was discovered by security researcher Gal Nagli, bypasses protections put in spot by OpenAI on chat.openai[.]com to examine a victim’s sensitive info.
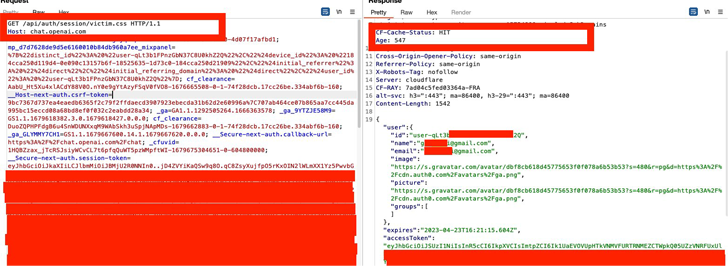
This is attained by first producing a specifically crafted link that appends a .CSS useful resource to the “chat.openai[.]com/api/auth/session/” endpoint and tricking a victim to click on the backlink, creating the reaction that contains a JSON object with the accessToken string to be cached in Cloudflare’s CDN.
The cached response to the CSS source (which has the CF-Cache-Status header benefit set to Hit) is then abused by the attacker to harvest the target’s JSON Web Token (JWT) credentials and acquire above the account.
Nagli said the bug was preset by OpenAI within just two hrs of accountable disclosure, indicative of the severity of the issue.
Uncovered this article intriguing? Abide by us on Twitter and LinkedIn to read much more special content material we write-up.
Some parts of this article are sourced from:
thehackernews.com


 Integrating humans with AI in structural design
Integrating humans with AI in structural design