Microsoft on Friday shared advice to assistance clients find out indicators of compromise (IoCs) linked with a a short while ago patched Outlook vulnerability.
Tracked as CVE-2023-23397 (CVSS score: 9.8), the critical flaw relates to a situation of privilege escalation that could be exploited to steal NT Lan Manager (NTLM) hashes and stage a relay attack without requiring any person interaction.
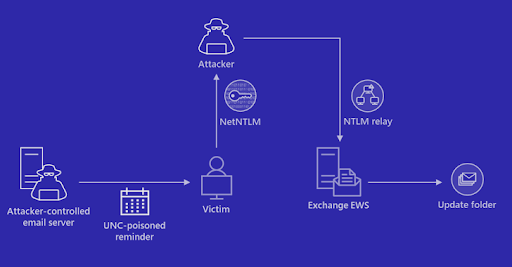
“External attackers could send out specially crafted email messages that will lead to a link from the victim to an untrusted location of attackers’ command,” the business mentioned in an advisory released this month.
“This will leak the Net-NTLMv2 hash of the sufferer to the untrusted network which an attacker can then relay to an additional service and authenticate as the victim.
The vulnerability was solved by Microsoft as aspect of its Patch Tuesday updates for March 2023, but not ahead of Russia-based mostly danger actors weaponized the flaw in attacks concentrating on federal government, transportation, energy, and armed service sectors in Europe.
Microsoft’s incident response staff said it observed proof of probable exploitation of the shortcoming as early as April 2022.
In a person attack chain explained by the tech giant, a successful Net-NTLMv2 Relay attack enabled the threat actor to obtain unauthorized obtain to an Exchange Server and modify mailbox folder permissions for persistent accessibility.
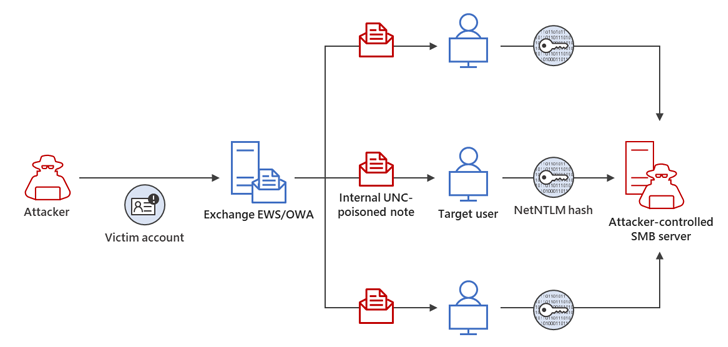
The compromised email account was then applied to lengthen the adversary’s entry within the compromised ecosystem by sending additional malicious messages to target other members of the identical business.
“Although leveraging NTLMv2 hashes to achieve unauthorized entry to resources is not a new system, the exploitation of CVE-2023-23397 is novel and stealthy,” Microsoft explained.
“Businesses really should review SMBClient function logging, Process Creation gatherings, and other out there network telemetry to detect prospective exploitation by using CVE-2023-23397.”
WEBINARDiscover the Hidden Dangers of Third-Bash SaaS Applications
Are you informed of the pitfalls connected with third-celebration app entry to your company’s SaaS apps? Sign up for our webinar to study about the varieties of permissions being granted and how to limit risk.
RESERVE YOUR SEAT
The disclosure will come as the U.S. Cybersecurity and Infrastructure Security Agency (CISA) unveiled a new open up resource incident response device that helps detect indications of malicious action in Microsoft cloud environments.
Dubbed Untitled Goose Resource, the Python-based utility features “novel authentication and information gathering strategies” to examine Microsoft Azure, Azure Lively Listing, and Microsoft 365 environments, the agency said.
Earlier this calendar year, Microsoft also urged consumers to keep their on-premises Exchange servers current as well as choose techniques to bolster their networks to mitigate opportunity threats.
Found this article attention-grabbing? Adhere to us on Twitter and LinkedIn to read through more distinctive information we publish.
Some parts of this article are sourced from:
thehackernews.com

 OpenAI Reveals Redis Bug Behind ChatGPT User Data Exposure Incident
OpenAI Reveals Redis Bug Behind ChatGPT User Data Exposure Incident