A “logical flaw” has been disclosed in NPM, the default deal manager for the Node.js JavaScript runtime atmosphere, that permits destructive actors to move off rogue libraries as respectable and trick unsuspecting builders into installing them.
The source chain risk has been dubbed “Package Planting” by scientists from cloud security organization Aqua. Adhering to accountable disclosure on February 10, the underlying issue was remediated by NPM on April 26.

“Up right up until lately, NPM permitted introducing anybody as a maintainer of the bundle without having notifying these consumers or acquiring their consent,” Aqua’s Yakir Kadkoda mentioned in a report published Tuesday.
This proficiently meant that an adversary could create malware-laced deals and assign them to trusted, common maintainers with out their awareness.
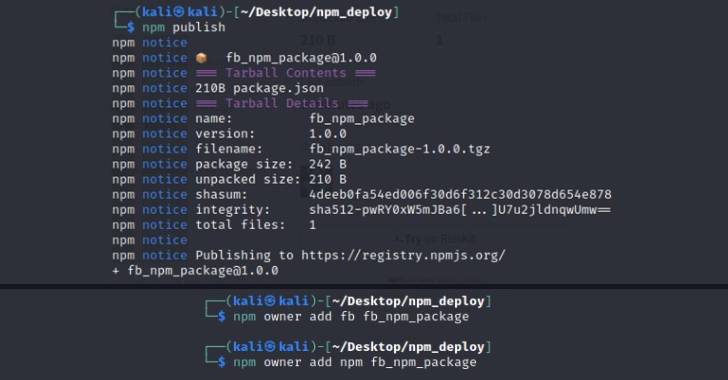
The concept below is to add credible owners involved with other well-known NPM libraries to the attacker-controlled poisoned package deal in hopes that executing so would entice builders into downloading it.
The penalties of these a provide chain attack are significant for a selection of reasons. Not only does it give a bogus feeling of trust among builders, it could also inflict reputational injury to reputable deal maintainers.

The disclosure comes as Aqua uncovered two extra flaws in the NPM system linked to two-variable authentication (2FA) that could be abused to aid account takeover attacks and publish destructive deals.
“The principal trouble is that any npm user can complete this and increase other NPM people as maintainers of their very own offer,” Kadkoda explained. “Ultimately, developers are accountable for what open up resource offers they use when building apps.”
Observed this short article intriguing? Stick to THN on Facebook, Twitter and LinkedIn to study far more distinctive written content we article.
Some parts of this article are sourced from:
thehackernews.com


 The Energy Department will block sales of inefficient light bulbs
The Energy Department will block sales of inefficient light bulbs