A malicious marketing campaign mounted by the North Korea-joined Lazarus Team is targeting strength suppliers about the planet, like all those based in the United States, Canada, and Japan.
“The campaign is intended to infiltrate organizations close to the globe for developing extensive-term obtain and subsequently exfiltrating facts of desire to the adversary’s nation-point out,” Cisco Talos said in a report shared with The Hacker News.
Some factors of the espionage attacks have presently entered public domain, courtesy of prior experiences from Broadcom-owned Symantec and AhnLab before this April and May perhaps.

Symantec attributed the procedure to a group referred to as Stonefly, a Lazarus subgroup which is improved acknowledged as Andariel, Guardian of Peace, OperationTroy, and Silent Chollima.
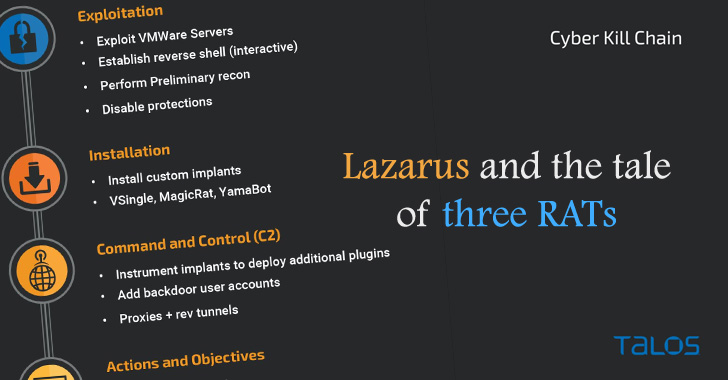
Even though these assaults previously led to the instrumentation of Preft (aka Dtrack) and NukeSped (aka Manuscrypt) implants, the most current attack wave is notable for utilizing two other parts of malware: VSingle, an HTTP bot which executes arbitrary code from a remote network, and a Golang backdoor named YamaBot.
Also put to use in the campaign is a new remote entry trojan termed MagicRAT that arrives with abilities to evade detection and launch extra payloads on the contaminated methods.
“Though the exact tactics have been used in both assaults, the resulting malware implants deployed have been unique from a person an additional, indicating the wide variety of implants readily available at the disposal of Lazarus,” researchers Jung soo An, Asheer Malhotra, and Vitor Ventura claimed.

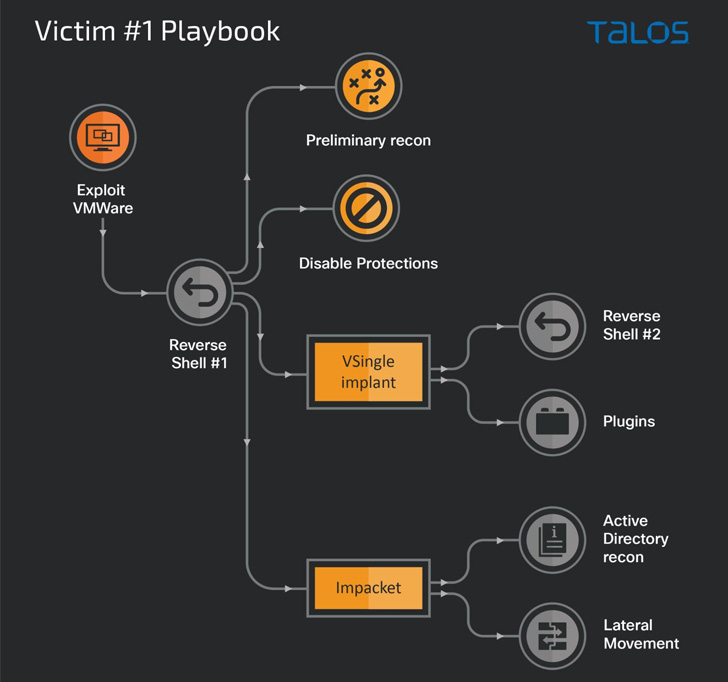
Preliminary access into organization networks is facilitated by suggests of exploitation of vulnerabilities in VMware goods (e.g., Log4Shell), with the final objective of setting up persistent entry to conduct pursuits in assist of North Korean govt goals.
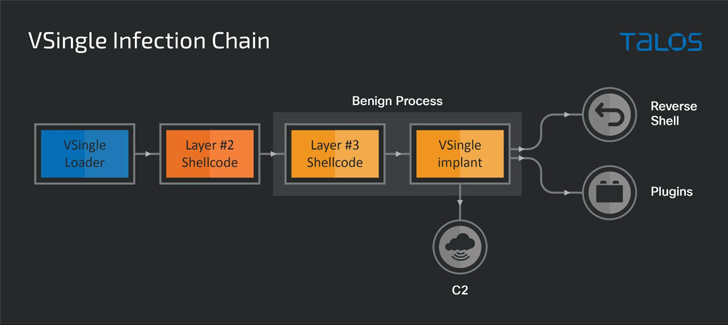
The use of VSingle in a person attack chain is stated to have enabled the danger actor to have out a selection of routines these kinds of as reconnaissance, exfiltration, and guide backdooring, providing the operators a stable being familiar with of the sufferer surroundings.
Other techniques embraced by the group aside from the use of bespoke malware contain credential harvesting by using tools like Mimikatz and Procdump, disabling antivirus parts, and reconnaissance of the Energetic Directory expert services, and even getting measures to cleanup their traces just after activating the backdoors on the endpoint.
Discovered this post intriguing? Observe THN on Fb, Twitter and LinkedIn to study a lot more exclusive content we publish.
Some parts of this article are sourced from:
thehackernews.com

 Apple's $799 Watch Ultra is bigger, more durable and lasts longer
Apple's $799 Watch Ultra is bigger, more durable and lasts longer