A new North Korean nation-condition cyber operator has been attributed to a sequence of strategies orchestrated to collect strategic intelligence that aligns with Pyongyang’s geopolitical pursuits considering that 2018.
Google-owned Mandiant, which is monitoring the exercise cluster under the moniker APT43, reported the group’s motives are equally espionage- and economically-motivated, leveraging procedures like credential harvesting and social engineering.
The financial angle to its attack campaigns is an try on the portion of the menace actor to create money to meet up with its “primary mission of gathering strategic intelligence.”
Victimology patterns suggest that focusing on is concentrated on South Korea, the U.S., Japan, and Europe, spanning authorities, instruction, investigation, policy institutes, business enterprise providers, and production sectors.
The danger actor was also noticed straying off course by putting wellness-associated verticals and pharma organizations from Oct 2020 by means of Oct 2021, underscoring its skill to quickly transform priorities.
“APT43 is a prolific cyber operator that supports the interests of the North Korean regime,” Mandiant scientists reported in a in depth specialized report posted Tuesday.
“The team brings together reasonably-refined specialized capabilities with aggressive social engineering ways, particularly towards South Korean and U.S.-primarily based governing administration companies, academics, and consider tanks centered on Korean peninsula geopolitical issues.”
APT43’s routines are claimed to align with the Reconnaissance Normal Bureau (RGB), North Korea’s international intelligence company, indicating tactical overlaps with one more hacking team dubbed Kimsuky (aka Black Banshee, Thallium, or Velvet Chollima).
What is actually additional, it has been observed employing equipment formerly related with other subordinate adversarial syndicates inside RGB, these types of as the Lazarus Team (aka TEMP.Hermit).
Attack chains mounted by APT43 contain spear-phishing emails made up of tailored lures to entice victims. These messages are despatched using spoofed and fraudulent personas that masquerade as important folks within just the target’s place of know-how to achieve their have faith in.
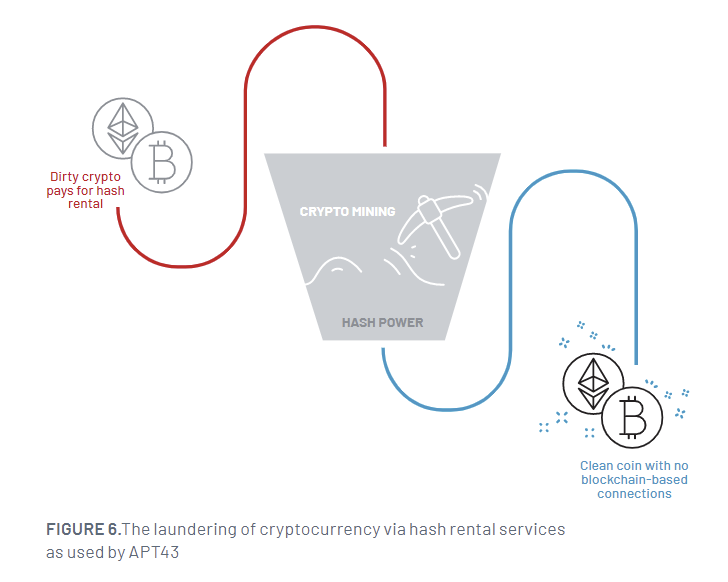
It is really also identified to just take edge of get hold of lists stolen from compromised people to detect much more targets and steal cryptocurrency to fund its attack infrastructure. The stolen electronic belongings are then laundered working with hash rental and cloud mining services to obscure the forensic trail and convert them into clean up cryptocurrency.
The final purpose of the attacks is to aid credential assortment strategies through domains that mimic a extensive assortment of legit providers and use the collected details to generate online personas.
“The prevalence of economically-motivated action between North Korean teams, even between these which have traditionally centered on cyber espionage, indicates a widespread mandate to self-fund and an expectation to sustain them selves with no extra resourcing,” Mandiant stated.
APT43’s functions are actualized by a significant arsenal of tailor made and publicly available malware this kind of as LATEOP (aka BabyShark), FastFire, gh0st RAT, Quasar RAT, Amadey, and an Android variation of a Windows-based mostly downloader named PENCILDOWN.
WEBINARDiscover the Concealed Risks of Third-Occasion SaaS Applications
Are you informed of the dangers connected with 3rd-bash app entry to your firm’s SaaS apps? Join our webinar to study about the types of permissions currently being granted and how to reduce risk.
RESERVE YOUR SEAT
The findings arrive considerably less than a 7 days immediately after German and South Korean government companies warned about cyber assaults mounted by Kimsuky utilizing rogue browser extensions to steal users’ Gmail inboxes.
“APT43 is extremely responsive to the demands of Pyongyang’s management,” the threat intelligence agency reported, noting the group “maintains a large tempo of action.”
“Though spear-phishing and credential collection in opposition to federal government, military, and diplomatic organizations have been main taskings for the group, APT43 eventually modifies its focusing on and practices, procedures and procedures to go well with its sponsors, which include carrying out economically-inspired cybercrime as essential to aid the regime.”
Uncovered this write-up attention-grabbing? Observe us on Twitter and LinkedIn to read through more distinctive content we submit.
Some parts of this article are sourced from:
thehackernews.com

 Phone-based measurements provide fast, accurate information about the health of forests
Phone-based measurements provide fast, accurate information about the health of forests