A group of academics from Northeastern University and KU Leuven has disclosed a basic style and design flaw in the IEEE 802.11 Wi-Fi protocol conventional, impacting a extensive variety of products managing Linux, FreeBSD, Android, and iOS.
Profitable exploitation of the shortcoming could be abused to hijack TCP connections or intercept shopper and web traffic, researchers Domien Schepers, Aanjhan Ranganathan, and Mathy Vanhoef explained in a paper released this 7 days.
The method exploits ability-preserve mechanisms in endpoint units to trick entry points into leaking info frames in plaintext, or encrypt them employing an all-zero critical.
“The unprotected nature of the electric power-help you save little bit in a frame’s header […] also enables an adversary to pressure queue frames meant for a particular client resulting in its disconnection and trivially executing a denial-of-provider attack,” the scientists observed.
In other words and phrases, the target is to leak frames from the entry stage destined to a sufferer consumer station by taking benefit of the reality that most Wi-Fi stacks do not sufficiently dequeue or purge their transmit queues when the security context improvements.
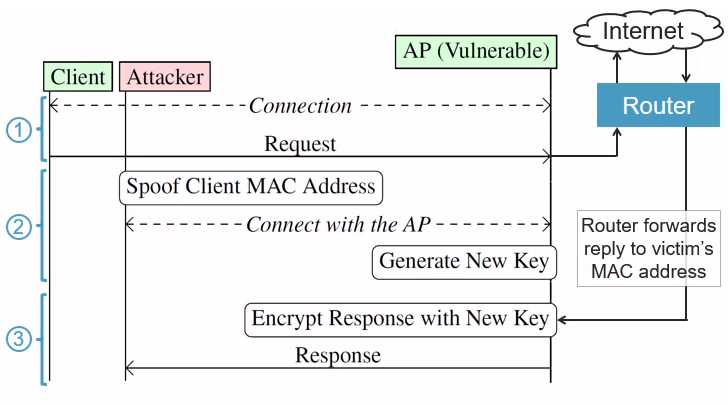
Other than manipulating the security context to leak frames from the queue, an attacker can override the client’s security context made use of by an accessibility stage to get packets supposed for the victim. This attack pre-supposes that the specific get together is connected to a hotspot-like network.
“The main strategy behind the attack is that the method in which clientele are authenticated is unrelated to how packets are routed to the right Wi-Fi customer,” Vanhoef described.
“A malicious insider can abuse this to intercept information to a Wi-Fi shopper by disconnecting a target and then connecting beneath the MAC address of the victim (making use of the qualifications of the adversary). Any packets that were nevertheless underway to the victim, this kind of web-site details that the target was still loading, will now be gained by the adversary rather.”
Cisco, in an informational advisory, explained the vulnerabilities as an “opportunistic attack and the information and facts attained by the attacker would be of minimal worth in a securely configured network.”
Nonetheless, the company acknowledged that the attacks introduced in the research might be effective towards Cisco Wireless Obtain Issue products and Cisco Meraki items with wi-fi capabilities.
To lessen the chance of these kinds of attacks, it really is advised to apply transportation layer security (TLS) to encrypt knowledge in transit and apply plan enforcement mechanisms to limit network obtain.
THN WEBINARBecome an Incident Response Pro!
Unlock the techniques to bulletproof incident response – Learn the 6-Phase system with Asaf Perlman, Cynet’s IR Leader!
Never Miss out on Out – Conserve Your Seat!
The conclusions get there months soon after scientists Ali Abedi and Deepak Vasisht demonstrated a spot-revealing privacy attack referred to as Wi-Peep that also exploits the 802.11 protocol’s energy-preserving system to localize target devices.
The investigate also follows other latest reports that have leveraged the Google Geolocation API to start area spoofing attacks in urban parts, not to point out use Wi-Fi signals to detect and map human motion in a place.
Observed this posting fascinating? Stick to us on Twitter and LinkedIn to read more distinctive written content we write-up.
Some parts of this article are sourced from:
thehackernews.com


 Thieves Steal $9m from Crypto Liquidity Pool
Thieves Steal $9m from Crypto Liquidity Pool