Various security vulnerabilities have been disclosed in Baxter’s internet-linked infusion pumps utilized by health care specialists in clinical environments to dispense medication to sufferers.
“Thriving exploitation of these vulnerabilities could consequence in access to sensitive facts and alteration of process configuration,” the U.S. Cybersecurity and Infrastructure Security Agency (CISA) claimed in a coordinated advisory.
Infusion pumps are internet-enabled units utilized by hospitals to supply treatment and diet directly into a patient’s circulatory program.
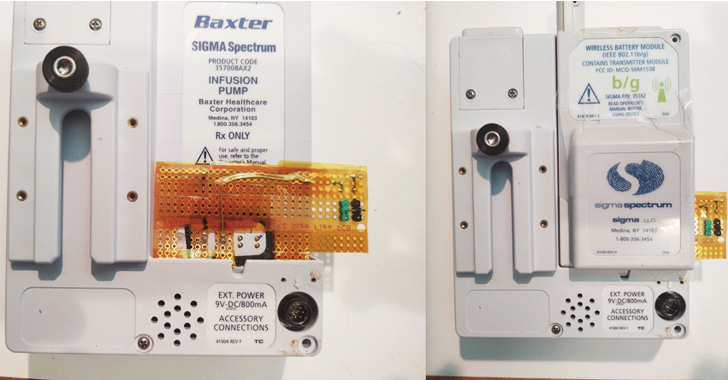
The 4 vulnerabilities in dilemma, identified by cybersecurity company Rapid7 and reported to Baxter in April 2022, have an affect on the next Sigma Spectrum Infusion programs –
- Sigma Spectrum v6.x product 35700BAX
- Sigma Spectrum v8.x model 35700BAX2
- Baxter Spectrum IQ (v9.x) product 35700BAX3
- Sigma Spectrum LVP v6.x Wi-fi Battery Modules v16, v16D38, v17, v17D19, v20D29 to v20D32, and v22D24 to v22D28
- Sigma Spectrum LVP v8.x Wi-fi Battery Modules v17, v17D19, v20D29 to v20D32, and v22D24 to v22D28
- Baxter Spectrum IQ LVP (v9.x) with Wi-fi Battery Modules v22D19 to v22D28

The checklist of flaws uncovered is underneath –
- CVE-2022-26390 (CVSS rating: 4.2) – Storage of network qualifications and affected person overall health data (PHI) in unencrypted structure
- CVE-2022-26392 (CVSS score: 2.1) – A format string vulnerability when running a Telnet session
- CVE-2022-26393 (CVSS score: 5.) – A structure string vulnerability when processing Wi-Fi SSID info, and
- CVE-2022-26394 (CVSS rating: 5.5) – Lacking mutual authentication with the gateway server host
Successful exploitation of the earlier mentioned vulnerabilities could trigger a distant denial-of-provider (DoS), or enable an attacker with actual physical entry to the device to extract sensitive facts or alternatively carry out adversary-in-the-middle attacks.
The vulnerabilities could further more final result in a “loss of critical Wi-Fi password facts, which could guide to larger network obtain ought to the network not be appropriately segmented,” Deral Heiland, principal security researcher for IoT at Swift7, instructed The Hacker News.
Baxter, in an advisory, emphasized that the issues only affect consumers who use the wireless capabilities of the Spectrum Infusion Technique, but also cautioned it could guide to a delay or interruption of therapy should the flaws be weaponized.
“If exploited, the vulnerabilities could result in disruption of [Wireless Battery Module] operation, disconnection of the WBM from the wi-fi network, alteration of the WBM’s configuration, or publicity of info saved on the WBM,” the enterprise claimed.

The hottest findings are yet a further indication of how typical software vulnerabilities keep on to plague the clinical business, a concerning growth given their opportunity implications affecting client treatment.
That reported, this is not the 1st time security flaws in infusion pumps have appear underneath the scanner. Previously this March, Palo Alto Networks Device 42 disclosed that an overwhelming the vast majority of infusion pumps have been exposed to practically 40 regarded vulnerabilities, highlighting the need to have to protected healthcare devices from security threats.
Baxter is recommending shoppers to be certain that all facts and settings are erased from decommissioned pumps, spot infusion techniques powering a firewall, implement network segmentation, and use solid wi-fi network security protocols to reduce unauthorized access.
It truly is vital to “carry out processes and methods to manage the de-acquisition of professional medical technology, [and] to guarantee that PII and/or configuration facts these types of as Wi-Fi, WPA, PSK, etc., are purged from the devices prior to resale or transfer to one more bash,” Heiland stated.
“Maintain sturdy physical security in just and all over health care spots that contains MedTech units, as very well as spots with accessibility to a biomed network. Apply network segmentation for all biomed networks to protect against other general or company networks from speaking with MedTech gadgets.”
Discovered this short article exciting? Follow THN on Facebook, Twitter and LinkedIn to go through a lot more special material we submit.
Some parts of this article are sourced from:
thehackernews.com

 Rapid7 Discusses SIGMA Spectrum Infusion Pump and WiFi Battery Vulnerabilities
Rapid7 Discusses SIGMA Spectrum Infusion Pump and WiFi Battery Vulnerabilities