Scientists have disclosed aspects of a recently uncovered macOS variant of a malware implant made by a Chinese espionage danger actor acknowledged to strike attack corporations across Asia.
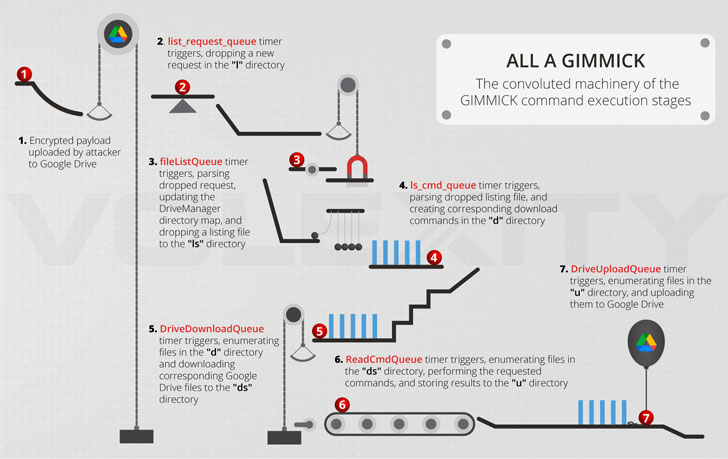
Attributing the assaults to a team tracked as Storm Cloud, cybersecurity firm Volexity characterised the new malware, dubbed Gimmick, a “aspect-abundant, multi-platform malware family members that utilizes public cloud hosting expert services (these as Google Travel) for command-and-handle (C2) channels.”
The cybersecurity organization said it recovered the sample by means of memory assessment of a compromised MacBook Pro operating macOS 11.6 (Major Sur) as part of an intrusion marketing campaign that took put in late 2021.

“Storm Cloud is an superior and flexible threat actor, adapting its resource established to match distinct working units applied by its targets,” Volexity scientists Damien Hard cash, Steven Adair, and Thomas Lancaster explained in a report.
“They make use of created-in running system utilities, open up-source equipment, and tailor made malware implants to reach their aims. Leveraging cloud platforms for C2, these kinds of as using Google Generate, boosts the probability of functioning undetected by network monitoring options.”
Contrary to its Windows counterpart, which is coded in each .NET and Delphi, the macOS variation is composed in Objective C. The preference of the programming languages aside, the two versions of the malware are recognized to share the identical C2 infrastructure and behavioral styles.
At the time deployed, Gimmick is introduced both as a daemon or in the type of a personalized software which is engineered to impersonate a system often launched by the targeted consumer. The malware is configured to talk with its Google Drive-primarily based C2 server only on doing the job times in order to even further mix in with the network targeted traffic in the focus on natural environment.
What’s additional, the backdoor, apart from retrieving arbitrary data files and executing instructions from the C2 server, arrives with its individual uninstall operation that makes it possible for it to erase by itself from the compromised machine.
To secure people in opposition to malware, Apple has issued new signatures to its built-in anti-malware protection suite identified as XProtect as of March 17, 2022 to block and take away the bacterial infections by means of its Malware Elimination Software (MRT).
“The get the job done associated in porting this malware and adapting its programs to a new functioning technique (macOS) is no light-weight undertaking and suggests the threat actor guiding it is very well resourced, adept, and functional,” the researchers stated.
Found this posting exciting? Follow THN on Fb, Twitter and LinkedIn to read through far more unique content we post.
Some parts of this article are sourced from:
thehackernews.com


 Over 200,000 MicroTik Routers Worldwide Are Under the Control of Botnet Malware
Over 200,000 MicroTik Routers Worldwide Are Under the Control of Botnet Malware