Industrial and govt corporations, such as enterprises in the military-industrial intricate and exploration laboratories, are the targets of a new malware botnet dubbed PseudoManyscrypt that has infected about 35,000 Windows desktops this calendar year on your own.
The title will come from its similarities to the Manuscrypt malware, which is portion of the Lazarus APT group’s attack toolset, Kaspersky scientists reported, characterizing the procedure as a “mass-scale spyware attack marketing campaign.” The Russian cybersecurity company stated it 1st detected the sequence of intrusions in June 2021.
At the very least 7.2% of all computer systems attacked by the malware are section of industrial handle devices (ICS) utilised by corporations in engineering, setting up automation, electrical power, production, development, utilities, and water administration sectors that are found predominantly in India, Vietnam, and Russia. Somewhere around a third (29.4%) of non-ICS personal computers are positioned in Russia (10.1%), India (10%), and Brazil (9.3%).

“The PseudoManuscrypt loader would make its way onto consumer devices by using a MaaS system that distributes malware in pirated software package installer archives,” the Kaspersky ICS CERT staff claimed. “A single precise scenario of the PseudoManuscrypt downloader’s distribution is its set up via the Glupteba botnet.”
Coincidentally, Glupteba’s operations have also taken a important strike when Google earlier this thirty day period disclosed that it acted to dismantle the botnet’s infrastructure and pursued litigation against two Russian nationals, who are alleged to have managed the malware alongside with 15 other unnamed men and women.
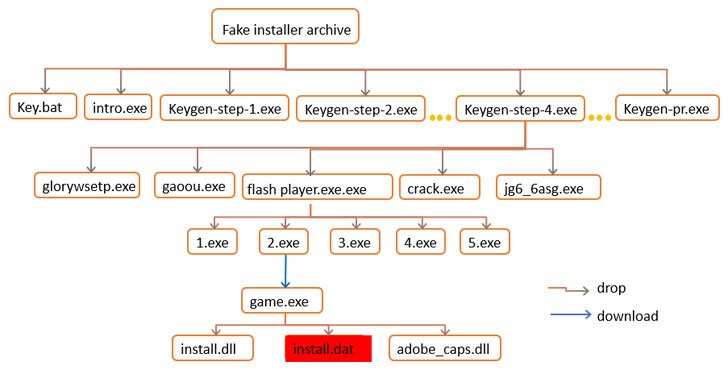
Between the cracked installers that are employed to gas the botnet represent Windows 10, Microsoft Business, Adobe Acrobat, Garmin, Call of Responsibility, SolarWinds Engineer’s Toolset, and even Kaspersky’s have antivirus alternative. The pirated application installations are driven by a technique named search poisoning in which the attackers build destructive websites and use research motor optimization (Search engine optimization) practices to make them demonstrate up prominently in lookup outcomes.
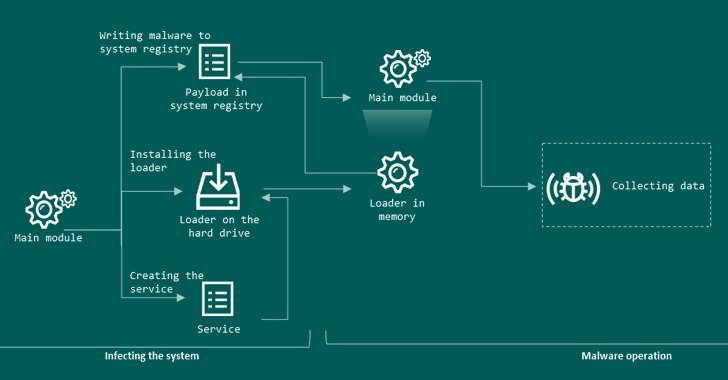
As soon as set up, PseudoManuscrypt arrives with an array of intrusive capabilities that enables the attackers to entire control of the contaminated system. This is composed of disabling antivirus options, stealing VPN connection info, logging keystrokes, recording audio, capturing screenshots and movies of the monitor, and intercepting info stored in the clipboard.
Kaspersky observed it has determined 100 various versions of the PseudoManuscrypt loader, with the earliest exam variants courting again to March 27, 2021. Components of the trojan have been borrowed from commodity malware like Fabookie and a KCP protocol library employed by the China-based APT41 team.
The malware samples analyzed by the ICS CERT also featured remarks penned in Chinese and have been observed specifying Chinese as the chosen language, but these clues on your own have been inconclusive to make an evaluation about the malware’s operators or their origins. Also unclear are the greatest targets of the marketing campaign, elevating inquiries as to irrespective of whether the assaults are monetarily inspired or condition-backed.
“The big variety of engineering computers attacked, which include programs utilised for 3D and actual physical modeling, the development and use of digital twins raises the issue of industrial espionage as just one of the doable targets of the marketing campaign,” the scientists claimed.
Observed this posting interesting? Adhere to THN on Fb, Twitter and LinkedIn to go through much more unique written content we write-up.
Some parts of this article are sourced from:
thehackernews.com