A new facts-thieving malware known as Mystic Stealer has been discovered to steal details from about 40 various web browsers and above 70 web browser extensions.
First advertised on April 25, 2023, for $150 for each thirty day period, the malware also targets cryptocurrency wallets, Steam, and Telegram, and employs intensive mechanisms to resist analysis.
“The code is intensely obfuscated making use of polymorphic string obfuscation, hash-primarily based import resolution, and runtime calculation of constants,” InQuest and Zscaler scientists claimed in an evaluation published previous week.
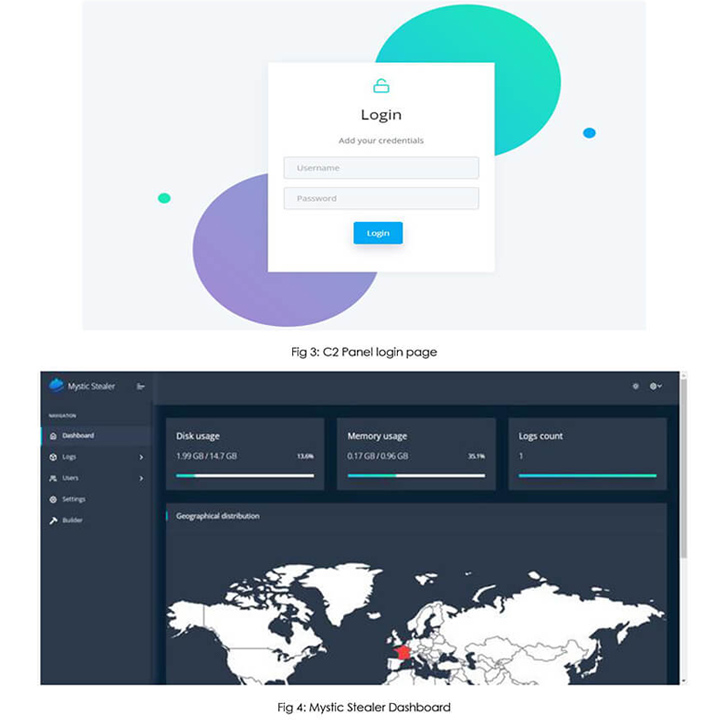
Mystic Stealer, like several other crimeware methods that are available for sale, focuses on pilfering data and is carried out in the C programming language. The command panel has been designed using Python.
Updates to the malware in Might 2023 integrate a loader element that lets it to retrieve and execute subsequent-stage payloads fetched from a command-and-regulate (C2) server, creating it a much more formidable menace.
C2 communications are accomplished working with a custom binary protocol in excess of TCP. As a lot of as 50 operational C2 servers have been discovered to day. The command panel, for its element, serves as the interface for potential buyers of the stealer to accessibility info logs and other configurations.
Cybersecurity firm Cyfirma, which posted a concurrent assessment of Mystic, mentioned, “the author of the product or service overtly invitations tips for supplemental enhancements in the stealer” by means of a focused Telegram channel, indicating lively attempts to court the cybercriminal group.
“It would seem crystal clear that the developer of Mystic Stealer is wanting to generate a stealer on par with the current tendencies of the malware house although making an attempt to target on anti-investigation and defense evasion,” the scientists mentioned.

The results appear as infostealers have emerged as a warm commodity in the underground overall economy, frequently serving as the precursor by facilitating the selection of qualifications to allow original access into concentrate on environments.
Place in a different way, stealers are applied as a basis by other cybercriminals to launch monetarily determined strategies that use ransomware and facts extortion factors.
The spike in level of popularity notwithstanding, off-the-shelf stealer malware are not currently being promoted at affordable selling prices to enchantment to a broader audience, they are also evolving to develop into extra deadly, packing in sophisticated techniques to fly less than the radar.
The at any time-evolving and volatile nature of the stealer universe is finest exemplified by the steady introduction of new strains this kind of as Album Stealer, Bandit Stealer, Devopt, Fractureiser, and Rhadamanthys in new months.
In a even further indication of threat actor’s attempts to evade detection, information stealers and distant obtain trojans have been noticed packaged in crypters like AceCryptor, ScrubCrypt (aka BatCloak), and Snip3.
The improvement also will come as HP Wolf Security in depth a March 2023 ChromeLoader marketing campaign codenamed Shampoo which is engineered to set up a malicious extension in Google Chrome and steal delicate data, redirect lookups, and inject ads into a victim’s browser session.
Forthcoming WEBINAR🔐 Mastering API Security: Comprehension Your Real Attack Area
Find the untapped vulnerabilities in your API ecosystem and consider proactive techniques in direction of ironclad security. Sign up for our insightful webinar!
Be a part of the Session.wn-button,.wn-label,.wn-label:afterscreen:inline-block.look at_two_webinarmargin:20px 10px 30px 0background:#f9fbffcolor:#160755padding: 5%border:2px strong #d9deffborder-radius:10pxtext-align:leftbox-shadow:10px 10px #e2ebff-webkit-border-top-still left-radius:25px-moz-border-radius-topleft:25px-webkit-border-base-ideal-radius:25px-moz-border-radius-bottomright:25px.wn-labelfont-sizing:13pxmargin:20px 0font-excess weight:600letter-spacing:.6pxcolor:#596cec.wn-label:followingwidth:50pxheight:6pxcontent:”border-top rated:2px sound #d9deffmargin: 8px.wn-titlefont-dimension:21pxpadding:10px 0font-pounds:900textual content-align:leftline-height:33px.wn-descriptiontextual content-align:leftfont-measurement:15.6pxline-top:26pxmargin:5px !importantcolor:#4e6a8d.wn-buttonpadding:6px 12pxborder-radius:5pxbackground-coloration:#4469f5font-dimensions:15pxcolor:#fff!importantborder:0line-top:inherittext-decoration:none!importantcursor:pointermargin:15px 20pxfloat:leftfont-bodyweight:500letter-spacing:.2px
“Customers encountered the malware generally from downloading unlawful content, these types of as films (Cocaine Bear.vbs), movie games, or other,” security researcher Jack Royer stated. “These internet sites trick victims into working a malicious VBScript on their PCs that triggers the infection chain.”
The VBScript then proceeds to start PowerShell code capable of terminating all current Chrome windows and opening a new session with the unpacked rogue extension making use of the “–load-extension” command line argument.
It also follows the discovery of a new modular malware trojan christened Pikabot that has the capacity to execute arbitrary commands and inject payloads that are furnished by a C2 server, these kinds of as Cobalt Strike.
The implant, energetic because early 2023, has been found to share resemblances with QBot with regard to distribution approaches, strategies, and malware behaviors, although there is no conclusive proof connecting the two people.
“Pikabot is a new malware loved ones that implements an comprehensive established of anti-examination methods and gives popular backdoor capabilities to load shellcode and execute arbitrary second-stage binaries,” Zscaler stated.
Observed this short article fascinating? Abide by us on Twitter and LinkedIn to go through extra distinctive information we submit.
Some parts of this article are sourced from:
thehackernews.com


 Researchers Discover New Sophisticated Toolkit Targeting Apple macOS Systems
Researchers Discover New Sophisticated Toolkit Targeting Apple macOS Systems