A under no circumstances-right before-witnessed sophisticated malware is targeting small business-quality routers to covertly spy on victims in Latin America, Europe, and North America at minimum because July 2022.
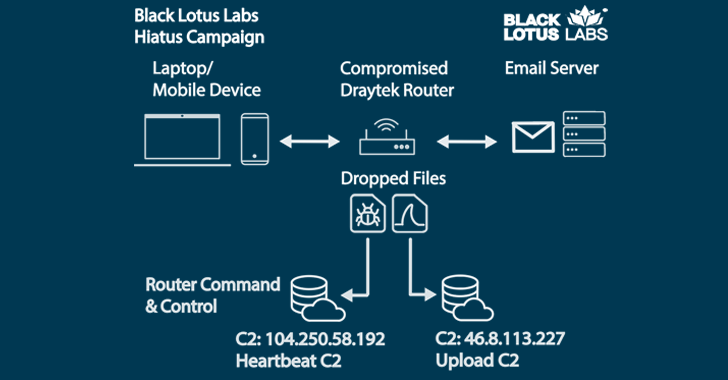
The elusive marketing campaign, dubbed Hiatus by Lumen Black Lotus Labs, has been discovered to deploy two malicious binaries, a remote accessibility trojan dubbed HiatusRAT and a variant of tcpdump that makes it probable to seize packet capture on the focus on gadget.
“At the time a targeted system is contaminated, HiatusRAT permits the menace actor to remotely interact with the program, and it utilizes prebuilt operation […] to change the compromised machine into a covert proxy for the risk actor,” the organization mentioned in a report shared with The Hacker Information.
“The packet-seize binary permits the actor to keep an eye on router traffic on ports affiliated with email and file-transfer communications.”
The risk cluster primarily singles out stop-of-daily life (EoL) DrayTek Vigor router versions 2960 and 3900, with somewhere around 100 internet-uncovered products compromised as of mid-February 2023. Some of the impacted business verticals incorporate prescribed drugs, IT services/consulting companies, and municipal governing administration, between other individuals.
Apparently, this represents only a modest fraction of the 4,100 DrayTek 2960 and 3900 routers that are publicly available about the internet, increasing the probability that “the risk actor is deliberately preserving a nominal footprint to restrict their exposure.”
Presented that the impacted devices are high-bandwidth routers that can at the same time guidance hundreds of VPN connections, it really is currently being suspected that the purpose is to spy on targets and build a stealthy proxy network.

“These equipment generally live outdoors the standard security perimeter, which signifies they ordinarily are not monitored or current,” Mark Dehus, director of risk intelligence for Lumen Black Lotus Labs, mentioned. “This aids the actor build and sustain very long-phrase persistence with no detection.”
The specific first accessibility vector applied in the attacks is unidentified, but a thriving breach is followed by the deployment of a bash script that downloads and executes HiatusRAT and a packet-seize binary.
HiatusRAT is aspect-prosperous and can harvest router facts, functioning procedures, and speak to a remote server to fetch files or run arbitrary commands. It really is also capable of proxying command-and-control (C2) traffic as a result of the router.
Discover the Most current Malware Evasion Practices and Prevention Techniques
Ready to bust the 9 most unsafe myths about file-dependent attacks? Sign up for our impending webinar and grow to be a hero in the fight versus affected individual zero bacterial infections and zero-working day security functions!
RESERVE YOUR SEAT
The use of compromised routers as proxy infrastructure is most likely an try to obfuscate the C2 functions, the scientists reported.
The conclusions appear additional than six months just after Lumen Black Lotus Labs also drop gentle on an unrelated router-concentrated malware campaign that utilized a novel trojan known as ZuoRAT.
“The discovery of Hiatus confirms that actors are continuing to pursue router exploitation,” Dehus claimed. “These strategies exhibit the need to safe the router ecosystem, and routers really should be on a regular basis monitored, rebooted, and updated, while close-of-lifestyle gadgets should really be replaced.”
Observed this write-up attention-grabbing? Comply with us on Twitter and LinkedIn to read far more exceptional content material we publish.
Some parts of this article are sourced from:
thehackernews.com

 From Disinformation to Deep Fakes: How Threat Actors Manipulate Reality
From Disinformation to Deep Fakes: How Threat Actors Manipulate Reality