Deep fakes are predicted to become a additional prominent attack vector. This is how to recognize them.
What are Deep Fakes?
A deep phony is the act of maliciously changing authentic images and movies with fabricated kinds to carry out info manipulation. To produce illustrations or photos, online video and audio that are substantial high quality sufficient to be made use of in deep fakes, AI and ML are necessary. These types of use of AI, ML and impression substitution are not like other styles of data manipulation, which use much less severe manipulation tactics, like misrepresentation of information and facts, isolating elements of the information and facts or modifying it in a deceptive fashion. Etay Maor, Senior Director of Security Technique at Cato Networks adds “To add issues, the modern developments and accessibility to AI created textual content, this sort of as GPT3, have currently been employed in blend with deepfakes (as a evidence of principle) to build interactive, human wanting discussion bots”
What Do Deep Fakes Glance Like?
Deep fakes appear in all styles and measurements. Some are less complicated and some are more superior. Some of the most preferred illustrations of deep fakes are:
Experience Swap
Confront swapping is the act of replacing the confront in a online video or graphic from a person individual to another. Encounter swapping requires devoted computer software, but it does not have to be based mostly on innovative technology – now 1 can even find cellular apps that support face swapping. Experience swapping that is offered in mobile apps is commonly limited to uncomplicated use instances, like swapping amongst the user’s shots and actors’ faces in movie scenes.

Far more highly developed encounter swapping does exist, but it needs additional design coaching and code, and – as a result – GPUs, which is costly and source-intensive. An example of a much more state-of-the-art deal with swapping deep phony can be see in this online video, in which Tom Cruise is swapped with the presenter’s experience:

This Tom Cruise confront swap expected two hrs of schooling on a GPU as perfectly as times of experienced movie editing write-up-processing. This could possibly sound like a ton, but it was also regarded a less complicated swap than some others, mainly because the presenter experienced a related haircut to Cruise and can impersonate his voice, which means significantly less training and submit-processing were required.
Puppet Master (Lip Sync)
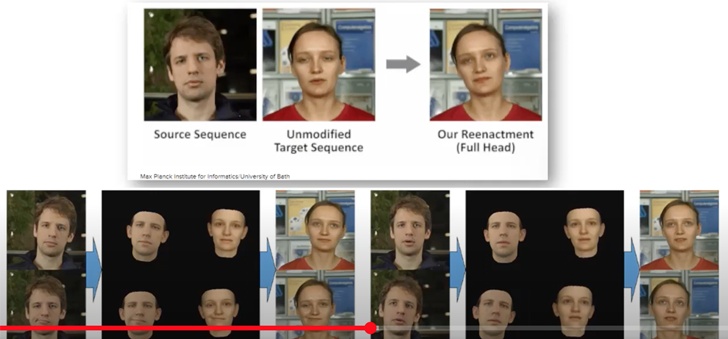
The ‘Puppet Master’ deep bogus is a method in which the picture of a person’s mouth actions are manipulated, creating it feel like the particular person is indicating a little something they haven’t basically mentioned. Compared to facial area swapping, which trains a design on the new, swapped encounter, ‘Puppet Master’ trains a design on the confront of the authentic graphic, and specially on the mouth movements.
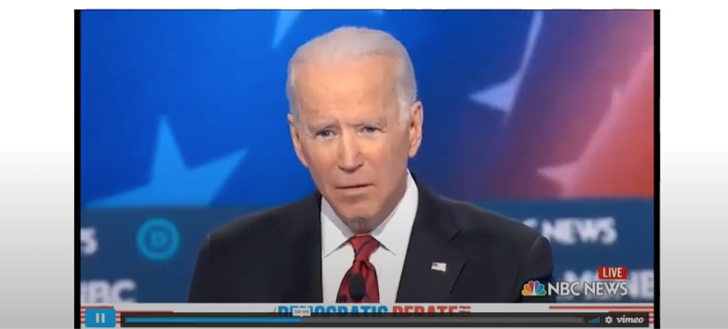
This is what it appears to be like:
[warning – explicit language]

The technology behind the ‘Puppet Master’ is dependent on synthesizing the mask, i.e. the unique graphic, and placing it on best of the design of the man or woman who is impersonating and lip syncing them.
Audio
The third outstanding kind of deep faux is audio-dependent. Audio deep fakes are audio information that get a actual person’s voice and make it appears like they are indicating a little something they had by no means said. Audio deep fakes are made by having audio data files, allocating annotations to the seems, schooling an ML design based mostly on the annotations to affiliate seems with textual content and then building a new audio file.
This is what is sounds like:
Deep Fakes vs. Affordable Fixes
Not all modified illustrations or photos or audio are deep fakes. Though deep fakes are media synthesized or modified working with AI, affordable fixes are media synthesized or modified making use of reduced-tech methods, which are simple to spot. They frequently have distortions and have been evidently manipulated. This is what a affordable fix appears like:
The Cyber Risk of Deep Fakes
Deep fakes have turn into much more sensible and obtainable and they are also quicker to make than at any time right before. This makes them a powerful resource for weaponization. As a end result, they pose a risk for businesses and for international locations. They can be used for cyber crime, social engineering, fraud, by risk actor nations to influence international operations, and a lot more.
For instance, deep pretend was employed to mimic a CEO’s voice and influence an govt to wire $243,000 to a scam account. Etay Maor of Cato Networks “Organization email comprise and phishing assaults are getting tougher and tougher to detect based on uncomplicated analysis of the language utilised. There is a have to have for a holistic approach, this sort of as the 1 provided by a single seller SASE option, that can detect the attack at different a number of choke points and not depend on isolated position merchandise that are doomed to are unsuccessful”. In another situation, a deep fake was introduced as proof in a kid custody case.
Deep fakes can also be utilized for spreading disinformation, i.e false distribution of info to influence community view or obscure the fact. For illustration, deep fakes could be applied to impersonate environment leaders and ignite an attack, or to impersonate a CEO and manipulate a company’s stock cost. In other instances, deep fakes permit plausible deniability, in which individuals could deny all sources of media by professing they are deep fakes, which results in a social breach of belief.
Last but not least, deep fake can be utilised for defamation, i.e harmful someone’s fantastic standing. For illustration, by generating revenge porn.
How to Detect Deep Fakes
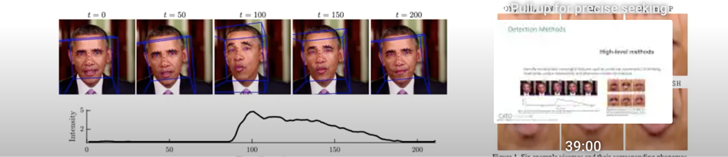
There are two principal styles of solutions for properly detecting deep fakes:
- Small-stage detection methods
- High-stage detection techniques
Low-stage Detection Techniques
Reduced-stage detection solutions depend on ML styles that are experienced to determine artifacts or pixellations that have been launched by way of the deep fake generation system. These artifacts might be imperceptible to the human eye, but the versions, which have been skilled on actual illustrations or photos and deep phony visuals, are able to detect them.

High-amount Detection Strategies
High-amount detection procedures use versions that can identify semantically meaningful characteristics. These involve unnatural movements, like blinking, head-pose or unique mannerisms, and phoneme-viseme mismatches.
Now, these detection techniques are considered precise. On the other hand, as deep faux technology improves and gets extra innovative, they are envisioned to become fewer productive and will need to have to be updated and enhanced. In addition to these tactics, every one particular of us can assist detect deep fakes by verifying the media source of movies and illustrations or photos we receive.
To learn more about various kinds of cybersecurity attacks and how to prevent them, Cato Networks’ Cyber Security Masterclass sequence is offered for your viewing.
Located this post intriguing? Follow us on Twitter and LinkedIn to read extra special information we submit.
Some parts of this article are sourced from:
thehackernews.com

 Core Members of DoppelPaymer Ransomware Gang Targeted in Germany and Ukraine
Core Members of DoppelPaymer Ransomware Gang Targeted in Germany and Ukraine