A threat actor of probable Pakistani origin has been attributed to nevertheless another campaign made to backdoor targets of fascination with a Windows-centered distant entry trojan named CrimsonRAT considering the fact that at minimum June 2021.
“Clear Tribe has been a extremely energetic APT team in the Indian subcontinent,” Cisco Talos scientists explained in an analysis shared with The Hacker Information. “Their primary targets have been authorities and armed forces staff in Afghanistan and India. This campaign furthers this concentrating on and their central goal of developing prolonged expression entry for espionage.”

Last month, the innovative persistent threat expanded its malware toolset to compromise Android gadgets with a backdoor named CapraRAT that exhibits a higher “degree of crossover” with CrimsonRAT.
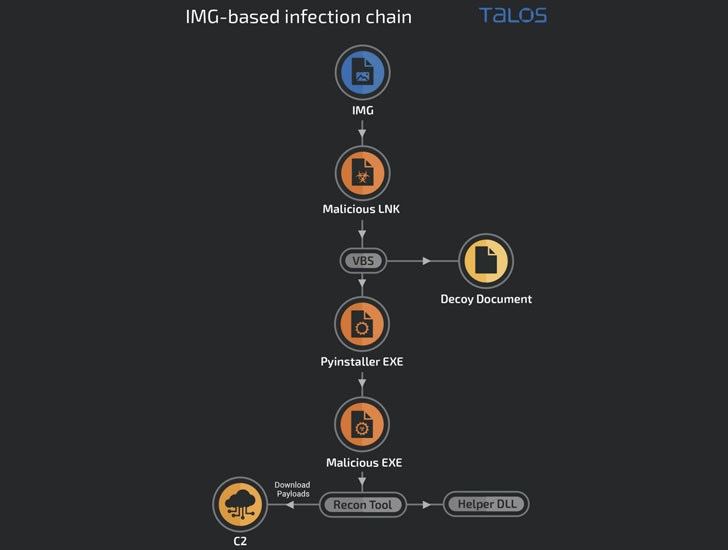
The most up-to-date established of assaults detailed by Cisco Talos entails generating use of faux domains that mimic respectable govt and linked corporations to provide the malicious payloads, like a Python-primarily based stager used to set up .NET-centered reconnaissance resources and RATs as properly as a barebones .NET-centered implant to operate arbitrary code on the contaminated method.
In addition to frequently evolving their deployment tactics and destructive functionalities, Clear Tribe is regarded to count on a wide range of shipping and delivery techniques, these as executables impersonating installers of reputable apps, archive files, and weaponized documents to concentrate on Indian entities and people today.

Just one of the downloader executables masquerades as Kavach (meaning “armor” in Hindi), an Indian authorities-mandated two-component authentication answer needed for accessing email products and services, in order to supply the malicious artifacts.
Also set to use are COVID-19-themed decoy visuals and digital difficult disk data files (aka VHDX documents) that are utilised as a launchpad for retrieving added payloads from a remote command-and-control server, this kind of as the CrimsonRAT, which is utilized to assemble delicate information and set up very long-expression access into sufferer networks.
“The use of several sorts of shipping and delivery cars and new bespoke malware that can be simply modified for agile operations suggests that the group is aggressive and persistent, nimble, and consistently evolving their ways to infect targets,” the researchers stated.
Located this posting intriguing? Follow THN on Fb, Twitter and LinkedIn to read more unique articles we put up.
Some parts of this article are sourced from:
thehackernews.com


