A new variant of an IoT botnet identified as BotenaGo has emerged in the wild, specially singling out Lilin security digital camera DVR equipment to infect them with Mirai malware.
Dubbed “Lilin Scanner” by Nozomi Networks, the latest edition is intended to exploit a two-yr-previous critical command injection vulnerability in the DVR firmware that was patched by the Taiwanese business in February 2020.

BotenaGo, initially documented in November 2021 by AT&T Alien Labs, is composed in Golang and functions above 30 exploits for acknowledged vulnerabilities in web servers, routers and other types of IoT products.
The botnet’s source code has given that been uploaded to GitHub, generating it ripe for abuse by other felony actors. “With only 2,891 traces of code, BotenaGo has the likely to be the setting up place for a lot of new variants and new malware families applying its source code,” the scientists claimed this 12 months.
The new BotenaGo malware is the most recent to exploit vulnerabilities in Lilin DVR devices soon after Chalubo, Fbot, and Moobot. Before this thirty day period, Qihoo 360’s Network Security Research Lab (360 Netlab) in depth a rapidly spreading DDoS botnet referred to as Fodcha that has spread via various N-Day flaws and weak Telnet/SSH passwords.
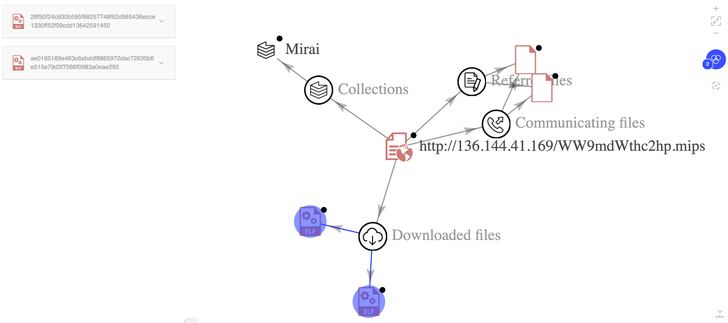
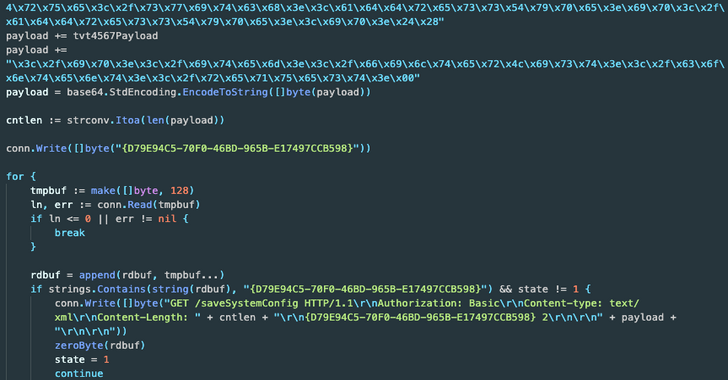
A single very important aspect sets Lillin Scanner aside from BotenaGo is its reliance on an external application to build an IP handle list of vulnerable Lilin equipment, subsequently exploiting the aforementioned flaw to execute arbitrary code remotely on the focus on and deploy Mirai payloads.

It really is worth noting that the malware can not propagate by itself in a worm-like trend, and can only be applied to strike the IP addresses provided as enter with the Mirai binaries.
“One more behavior linked with the Mirai botnet is the exclusion of IP ranges belonging to the internal networks of the U.S. Section of Protection (DoD), U.S. Postal Support (USPS), Standard Electric (GE), Hewlett-Packard (HP), and other people,” the scientists reported.
Like Mirai, the emergence of Lilin Scanner details to the reuse of quickly accessible source code to spawn new malware offshoots.
“Its authors eradicated virtually all of the 30+ exploits present in BotenaGo’s first supply code,” the scientists reported, including, “it would seem that this device has been quickly constructed utilizing the code base of the BotenaGo malware.”
Discovered this report exciting? Adhere to THN on Facebook, Twitter and LinkedIn to browse more unique information we submit.
Some parts of this article are sourced from:
thehackernews.com

 FBI Warns of BlackCat Ransomware That Breached Over 60 Organisations Worldwide
FBI Warns of BlackCat Ransomware That Breached Over 60 Organisations Worldwide