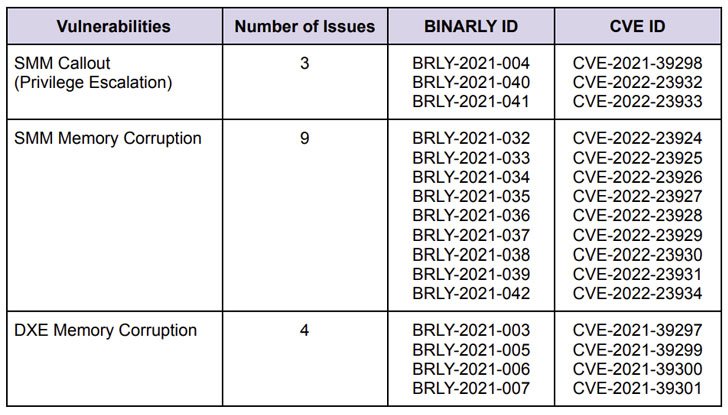
Cybersecurity scientists on Tuesday disclosed 16 new significant-severity vulnerabilities in numerous implementations of Unified Extensible Firmware Interface (UEFI) firmware impacting various HP organization units.
The shortcomings, which have CVSS scores ranging from 7.5 to 8.8, have been uncovered in HP’s UEFI firmware. The variety of units influenced features HP’s laptops, desktops, place-of-sale (PoS) units, and edge computing nodes.
“By exploiting the vulnerabilities disclosed, attackers can leverage them to complete privileged code execution in firmware, down below the operating process, and probably supply persistent malicious code that survives operating procedure re-installations and makes it possible for the bypass of endpoint security solutions (EDR/AV), Protected Boot and Virtualization-Centered Security isolation,” firmware security firm Binarly reported in a report shared with The Hacker News.
The most serious of the flaws concern a number of memory corruption vulnerabilities in the Process Administration Method (SMM) of the firmware, thus enabling the execution of arbitrary code with the optimum privileges.
Next a coordinated disclosure process with HP and CERT Coordination Middle (CERT/CC), the issues were being dealt with as element of a series of security updates delivered in February and March 2022.
“Unfortunately, most of the issues […] are repeatable failures, some of which are owing to the complexity of the codebase or legacy parts that get a lot less security focus, but are nonetheless commonly employed in the industry,” the researchers pointed out.
The disclosure arrives a small over a thirty day period after Binarly publicized the discovery of 23 substantial-impression vulnerabilities in Insyde Software’s InsydeH2O UEFI firmware that could be weaponized to deploy persistent malware that’s able of evading security units.

The newest findings are also sizeable in mild of the point that firmware has emerged as an ever-increasing attack area for risk actors to launch remarkably-qualified devastating attacks. At least 5 distinct firmware malware strains have been detected in the wild to day considering the fact that 2018.
“Securing the firmware layer is generally overlooked, but it is a solitary stage of failure in equipment and is one of the stealthiest solutions in which an attacker can compromise equipment at scale,” the U.S. Commerce and Homeland Security departments highlighted in a report posted past thirty day period.
Found this report interesting? Abide by THN on Facebook, Twitter and LinkedIn to go through a lot more exclusive content we post.
Some parts of this article are sourced from:
thehackernews.com

 Study for four CompTIA certifications with a $30 lab bundle
Study for four CompTIA certifications with a $30 lab bundle