Cybersecurity researchers have get rid of gentle on a new phishing marketing campaign that has been identified as targeting people today in Pakistan making use of a tailor made backdoor.
Dubbed PHANTOM#SPIKE by Securonix, the not known risk actors powering the activity have leveraged army-related phishing documents to activate the infection sequence.
“Even though there are several methods made use of now to deploy malware, the threat actors made use of ZIP information with a password-shielded payload archive contained in,” researchers Den Iuzvyk, Tim Peck, and Oleg Kolesnikov stated in a reportreport shared with The Hacker News.
The campaign is notable for its absence of sophistication and the use of uncomplicated payloads to realize distant accessibility to target devices.
The email messages come bearing a ZIP archive that purports to be meeting minutes connected to the International Military-Technological Discussion board Military 2024, a legitimate occasion organized by the Ministry of Defense of the Russian Federation. It is really set to be held in Moscow in mid-August 2024.
Present within just the ZIP file is a Microsoft Compiled HTML Help (CHM) file and a concealed executable (“RuntimeIndexer.exe”), the previous of which, when opened, displays the meeting minutes as well as a couple of illustrations or photos, but stealthily runs the bundled binary as quickly as the consumer clicks wherever on the document.
The executable is designed to perform as a backdoor that establishes connections with a distant server around TCP in buy to retrieve instructions that are subsequently operate on the compromised host.
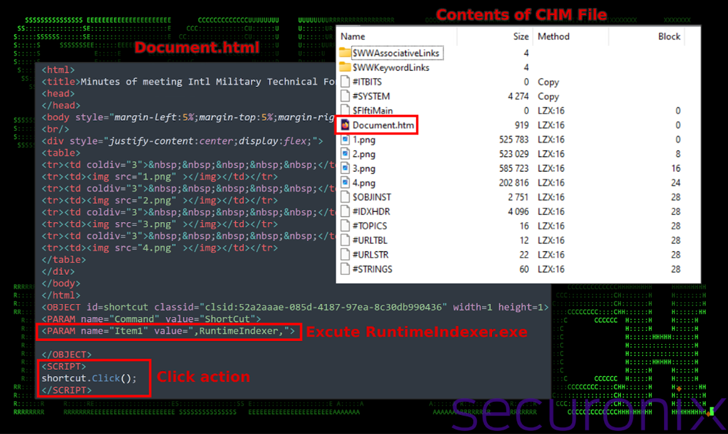
In addition to passing together method data, it executes the instructions via cmd.exe, gathers the output of the operation, and exfiltrates it back to the server. This features managing commands like systeminfo, tasklist, curl to extract the public IP address making use of ip-api[.]com, and schtasks to established up persistence.
“This backdoor primarily capabilities as a command line-centered distant entry trojan (RAT) that provides the attacker with persistent, covert, and protected access to the infected method,” the researchers explained.
“The potential to execute commands remotely and relay the outcomes again to the C2 server permits the attacker to manage the infected procedure, steal delicate information and facts or execute more malware payloads.”
Located this short article intriguing? Adhere to us on Twitter and LinkedIn to examine far more exceptional articles we write-up.
Some parts of this article are sourced from:
thehackernews.com


 Oyster Backdoor Spreading via Trojanized Popular Software Downloads
Oyster Backdoor Spreading via Trojanized Popular Software Downloads