“Owowa” stealthily lurks on IIS servers, ready to harvest effective logins when an Outlook Web Obtain (OWA) authentication request is designed.
Researchers have uncovered a beforehand mysterious malicious IIS module, dubbed Owowa, that steals qualifications when customers log into Microsoft Outlook Web Accessibility (OWA).
Internet Information and facts Expert services (IIS), Microsoft’s web server/web-hosting software package suite, can be prolonged through several incorporate-ons that are recognized as modules.
Like plugins for WordPress or Chrome extensions, IIS modules offer an desirable way to facet-load malicious capabilities into web-dealing with programs. In this situation, Owowa infects Exchange servers, exposing Exchange’s OWA purpose. Further than credential theft, it allows distant attackers to run commands on the underlying server and to set up a foothold for obtain to the broader network, scientists warned.
“[It] makes it possible for the attackers to steal login qualifications for Outlook Web Obtain and get distant access management to the underlying server,” according to researchers at Kaspersky, in a Tuesday writeup. “Its destructive abilities can easily be released by sending seemingly innocuous requests – in this situation, OWA authentication requests.”
The module is also stealthy and tricky to detect, and it presents persistence even in the facial area of computer software updates from Trade, according to Pierre Delcher, senior security researcher with Kaspersky’s World Investigation and Assessment Crew (Great).
“The individual threat with Owowa is that an attacker can use the module to passively steal qualifications from people who are legitimately accessing web providers,” he stated. “This is a far stealthier way to achieve distant entry than sending phishing emails. In addition, though IIS configuration instruments can be leveraged to detect this sort of threats, they are not element of conventional file and network checking pursuits, so Owowa may possibly be conveniently disregarded by security tools.”
The malicious module can be loaded by a cyberattacker that has first access to the server environment (possibly by exploiting the ProxyLogon or ProxyShell vulnerabilities), scientists discussed. It is loaded utilizing the PowerShell script proven below:
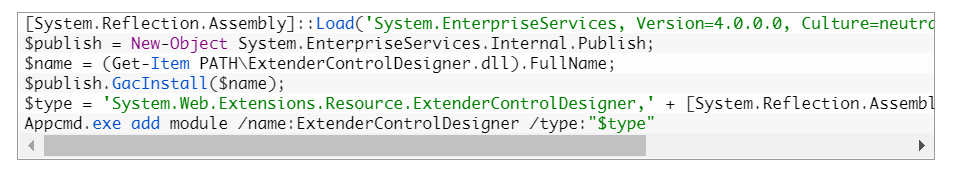
Resource: Kaspersky.
“The module is to start with registered in the world wide assembly cache, and can then be loaded by the IIS server that is jogging the OWA software,” in accordance to Kaspersky.
As soon as installed, the module screens HTTP requests and responses for OWA targeted visitors by hooking the “PreSendRequestContent” occasion, according to Kaspersky. When an OWA authentication request is created, it springs into action, very first checking that the login try was thriving by examining that the OWA software is sending an authentication token again to the person. If that’s the situation, the username, password, user’s IP tackle and recent timestamp are saved in a file and encoded with RSA encryption.
Cybercriminals can interact with Owowa and exfiltrate the harvested logins by coming into specifically crafted instructions – thorough down below – into the username and password fields in the OWA log-in webpage of the compromised server, according to Kaspersky’s assessment.
- If the OWA username is jFuLIXpzRdateYHoVwMlfc, Owowa will return the encrypted qualifications log, encoded in foundation64
- If the OWA username is Fb8v91c6tHiKsWzrulCeqO, the destructive module deletes the written content of the encrypted qualifications log, and returns the Okay string (encrypted utilizing RSA)
- If the OWA username is dEUM3jZXaDiob8BrqSy2PQO1, Owowa executes the command that is typed in the OWA password discipline using PowerShell on the compromised server. The final result of the command is encrypted (as previously explained) and returned to the operator.
Monitoring Owowa’s Improvement
Scientists uncovered that Owowa was compiled someday in between late 2020 and April 2021, ironically around the same time that the aforementioned ProxyLogon set of four critical vulnerabilities in Microsoft Trade servers have been uncovered, supplying attackers the means to get entry to registered email accounts and execute arbitrary code. The module has been made use of considering that then to target government and public-sector victims in Indonesia, Malaysia, Mongolia and the Philippines, like a condition transportation organization. Researchers suspect there are also victims in Europe.
Kaspersky researchers could not hyperlink Owowa to any certain threat actor, over and above noting the use of the username “S3crt” in the coding. The name is connected to the development of other malicious binary loaders, scientists mentioned. Having said that, the take care of could really perfectly be utilised by multiple people today. It’s also the username on an account on RAID Community forums, which specializes in Core Influence: a well-known penetration-tests software suite.
Whatsoever could be the situation with S3crt, the operator is not likely to be an sophisticated persistent risk (APT) regardless of the victimology and clear aim of espionage, in accordance to the examination. That is for the reason that the development displays some rookie blunders.
For instance, the creators overlooked explicit warnings from Microsoft relating to many risky enhancement tactics for HTTP modules, which could consequence in server crashes (as a result alerting admins to Owowa’s presence). And, they remaining behind sensitive information and facts on the improvement environment, plainly noticeable in publicly available samples. These can be made use of to locate backlinks to further more samples or on line profiles.
“The very good news is the attackers don’t seem very advanced,” mentioned Paul Rascagneres, senior security researcher with Kaspersky’s Good. “Companies need to closely keep an eye on Exchange servers because they are very delicate and consist of all corporate emails. We also suggest contemplating all running modules as critical and checking them consistently.”
How to Secure Versus Destructive IIS Modules
To protect against the risk, Kaspersky recommended that corporations:
- Routinely check out loaded IIS modules on uncovered IIS servers (notably Exchange servers), leveraging current tools from the IIS server suite. Malicious IIS modules, and Owowa in certain, can be discovered by making use of the command “appcmd.exe” or the IIS configuration device, which lists all the loaded modules on a presented IIS server.
- Examine for these kinds of modules as component of normal risk-hunting actions, and each time a major vulnerability is introduced on Microsoft server products.
- Concentration the protection tactic on detecting lateral movement and knowledge exfiltration to the internet, paying out specific consideration to outgoing site visitors to detect cybercriminal connections.
- Back up details regularly and make sure it can be swiftly accessed in an emergency.
Check out out our free upcoming are living and on-demand on the internet town halls – exclusive, dynamic discussions with cybersecurity experts and the Threatpost community.
Some parts of this article are sourced from:
threatpost.com


 SAP Kicks Log4Shell Vulnerability Out of 20 Apps
SAP Kicks Log4Shell Vulnerability Out of 20 Apps