The APT, which targets Middle-Japanese electrical power corporations & telecoms, has been relatively tranquil due to the fact its exposure but not entirely silent. It’s kept up attacks as a result of 2021 and is working on retooling its arsenal but yet again.
The Lyceum risk group has resurfaced, this time with a bizarre variant of a distant-accessibility trojan (RAT) that does not have a way to chat to a command-and-control (C2) server and could possibly instead be a new way to proxy targeted visitors amongst interior network clusters.
Kaspersky’s Mark Lechtik – senior security researcher at the company’s International Analysis & Assessment Team (Wonderful) – reported in a Monday put up that the team has identified a new cluster of Lyceum action that is focused on two entities in Tunisia.
In a paper (PDF) introduced earlier this thirty day period at the Virus Bulletin conference, Lechtik and fellow Kaspersky researchers Aseel Kayal and Paul Rascagneres wrote that the risk actor has attacked large-profile Tunisian organizations, these as telecoms or aviation firms.
That suits into the group’s concentrate on listing. Lyceum has been active due to the fact as early as April 2018, when it attacked telecoms, and critical infrastructure in Center Japanese oil-and-gasoline companies. Lyceum treads frivolously but carries a significant adhere: “All the though it has kept a minimal profile, drawing minimal focus from security researchers,” the trio of researchers wrote.
The Lyceum team (aka Hexane) was initially exposed in 2019 by Secureworks, which spotted the group targeting Middle Eastern power firms and telecoms with malware-laced spearphishing emails.
Back again then, Lyceum was making use of a variety of PowerShell scripts and a novel .NET-centered remote-access trojan (RAT) called DanBot, which deployed put up-intrusion resources to distribute across contaminated companies’ networks, steal qualifications and other account info, and log keystrokes. DanBot communicated with a C2 server by using custom made-built protocols in excess of DNS or HTTP.
Kaspersky’s new Lyceum findings were sparked by a PowerShell script (MD5: 94eac052ea0a196a4600e4ef6bec9de2) that was submitted to VirusTotal in past November, and which assisted scientists to follow the menace group’s extra new tracks.
“The script is obfuscated and Foundation64-encoded, suggesting that it was perhaps hoping to evade detection in a victim’s setting,” according to the paper. “But just after de-obfuscating it, the resulting code reveals a lot of feedback that had been left by the attackers, detailing what the script does and even detailing the modifications from prior versions. Some of the features had been also marked as out of date, suggesting that this script is probably a perform in development.”
Though it is held fairly tranquil, Lyceum has not been silent. In reality, Kaspersky has located adequate threads to tie it back again to the APT34/OilRig danger actor, as comprehensive beneath.
Off of .NET, Onto C++
The group’s tracks display that Lyceum’s arsenal has evolved. The group has shifted from its before .NET malware and onto new versions prepared in C++. Kaspersky has described two clusters of variants, named “James” and “Kevin” only mainly because those people have been the names on the devices used to compile the malware.
People DanBot variants cropped up a couple months just after Secureworks revealed its conclusions about Lyceum, suggesting that the publicity put some hurt on the group, as Kayal mentioned during the Virus Bulletin conference:
“There is a time hole of a few of months among the previously documented DanBot and the two newer variants,” she stated. “We imagine that this is in all probability because of to SecureWorks’ publication, and that the attackers may possibly have determined to introduce some alterations to their toolset immediately after some of them had been uncovered in this report.”
Both of those of the new DanBot variants, like the first DanBot, support identical custom C2 protocols tunneled more than DNS or HTTP, Lechtik explained in his Monday short. “That reported, we also determined an uncommon variant that did not have any mechanism for network interaction,” he reported. “We think that it was utilised as a means to proxy traffic among two inner network clusters.”
Kevin, You Weirdo
Kaspersky thinks that the Kevin variant may perhaps “represent a new branch of advancement in the group’s arsenal,” according to the paper.
The variant to start with appeared in June 2020, with most samples carrying a string signifying that it was an inner version named v1..2. Then, 10 months ago, in December, a new wave of samples from the Kevin variant emerged, carrying the variation quantity v2.1..2.
The variant introduced alterations in conversation protocols and is largely compiled for 64-little bit programs. Its reason is “to facilitate a communication channel that passes arbitrary instructions to be executed by the implant,” in accordance to Kaspersky’s writeup.
“To do this, the malware requests documents that will be produced in the file procedure and published with instructions been given from the server employing a specified structure,” the paper continued. “The contents of the file will be read through and interpreted by the implant according to that format, wherever predefined keywords will be changed with specific malware-linked paths or used to update interior run-time configurations. In turn, the commands will be executed, issuing the reaction back to the server.”
But prior to conversation takes place, the Kevin variant may well bootstrap and get ready the target ecosystem for its execution by way of a established of actions prevalent to a great deal of its samples, as scientists explained.
A partial listing of all those actions:
- Hides the recent window from the person utilizing the ‘ShowWindow’ API function.
- Makes a mutex with a lower-circumstance GUID value that is really hard coded in the binary.
- Checks the arguments with which it was executed. It’s obligatory that the 1st argument is equivalent to a variation quantity (e.g., v1..2 or v2.1..2). “We assess that this could have been included in buy to prevent total execution of the malware features in sandboxed environments,” the researchers discussed.
Tracing the Threads to Other APTs
Kaspersky scientists reported that they recognized specified similarities involving Lyceum and the notorious condition-sponsored campaign from the DNSpionage team, which scooped up qualifications by targeting national security organizations throughout the Middle East and North Africa (MENA) – and in other places – with domain identify program (DNS) hijacking assaults.
DNSpionage is in change related with APT34/OilRig, Lechtik mentioned in his Monday writeup: An innovative persistent risk (APT) that introduced a collection of cyberattacks on a Center Jap telecom in July 2020.
“Besides equivalent geographical focus on possibilities, and the use of DNS or bogus websites to tunnel C2 data as a TTP [tactics, techniques and procedures), we were able to trace significant similarities between lure documents delivered by Lyceum in the past and those used by DNSpionage,” he wrote. “These were made evident through a common code structure and choices of variable names.”
The researchers noted that Lyceum’s modus operandi “bears a striking resemblance to that of APT34/OilRig.”
According to the paper, “Both groups have similar geopolitical targeting, and prefer to use DNS tunneling in the different payloads they have developed over the years. Although we did not find conclusive evidence to support this, we did notice some similarities between the delivery documents used by Lyceum back in 2018-2019 and those by DNSpionage, which is also believed to have ties to OilRig.”
As well, the macros embedded in documents from the two groups share the same variable names and a similar code structure, as shown below.
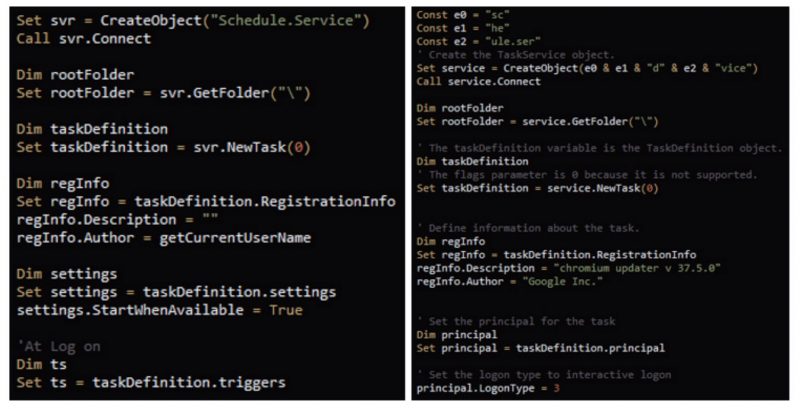
Similar macros in Lyceum and DNSpionage delivery documents. Source: Kaspersky.
Attacks Started with Excel Docs
When Lyceum/Hexane was first exposed, its attacks were started with Excel documents boobytrapped with malicious macros. One of the observed attacks used messages promising to display a list of events related to industrial control systems or to Middle Eastern gas-and-oil content. Another malicious spreadsheet pretended to be related to security, purporting to contain a list of the worst passwords since 2017.
In its recent investigation, Kaspersky identified some of Lyceum’s other MOs, including some of the commands the attackers used within the compromised environments, as well as how user credentials stored in browsers were stolen by using a PowerShell script, and details about a custom keylogger deployed on some of the targeted machines.
Kaspersky’s paper takes a deep dive into the technical aspects of its investigation into Lyceum, but the TL;DR version is that the APT didn’t blink out of existence following its discovery in 2019, and we’ll likely hear more about it still.
“With considerable revelations on the activity of DNSpionage in 2018, as well as further data points that shed light on an apparent relationship with APT34, we can assess that the latter may have changed some of its modus operandi and organizational structure, manifesting into new operational entities, tools and campaigns,” according to Kaspersky’s paper.
Lyceum=Outgrowth of DNSpionage?
One of the new operational arms of DNSpionage is, in fact, Lyceum, Kaspersky asserted. “After further exposure by Secureworks in 2019, [Lyceum] experienced to retool but yet another time,” foremost to the campaign Kaspersky described in its paper.
Lyceum has not ceased procedure somewhat, the group has “attempted to get a foothold on the focused networks time and time once again,” the scientists stated.
The APT has not only held up its tried assaults by way of 2021. And, its samples also display code versions that issue to the group owning started to retool when yet again.
“With the publicity of this publication, we assess that Lyceum will keep on to be energetic, working with renewed malware and TTPs and modifying its abilities to conduct espionage and counterintelligence operations in the Center East,” the scientists predicted.
Test out our free impending live and on-demand from customers online city halls – one of a kind, dynamic conversations with cybersecurity authorities and the Threatpost community.
Some parts of this article are sourced from:
threatpost.com


 Apple Music's new $5 plan only works with Siri
Apple Music's new $5 plan only works with Siri