A monetarily-determined North Korean threat actor is suspected to be guiding a new Apple macOS malware pressure named RustBucket.
“[RustBucket] communicates with command and handle (C2) servers to obtain and execute numerous payloads,” Jamf Danger Labs researchers Ferdous Saljooki and Jaron Bradley reported in a technological report released very last 7 days.
The Apple product management company attributed it to a risk actor recognized as BlueNoroff, a subgroup in the notorious Lazarus cluster that’s also tracked under the monikers APT28, Nickel Gladstone, Sapphire Sleet, Stardust Chollima, and TA444.
The connections stem from tactical and infrastructure overlaps with a prior campaign exposed by Russian cybersecurity firm Kaspersky in late December 2022 most likely aimed at Japanese economic entities applying fake domains impersonating undertaking cash corporations.
BlueNoroff, in contrast to other constituent entities of the Lazarus Team, is recognized for its sophisticated cyber-enabled heists focusing on the SWIFT technique as nicely as cryptocurrency exchanges as section of an intrusion established tracked as CryptoCore.
Before this calendar year, the U.S. Federal Bureau of Investigation (FBI) implicated the menace actor for the theft of $100 million in cryptocurrency property from Harmony Horizon Bridge in June 2022.
BlueNoroff’s attack repertoire is also stated to have witnessed a important shift over the previous few months, what with the group producing use of task-themed lures to trick email recipients into coming into their credentials on faux landing web pages.
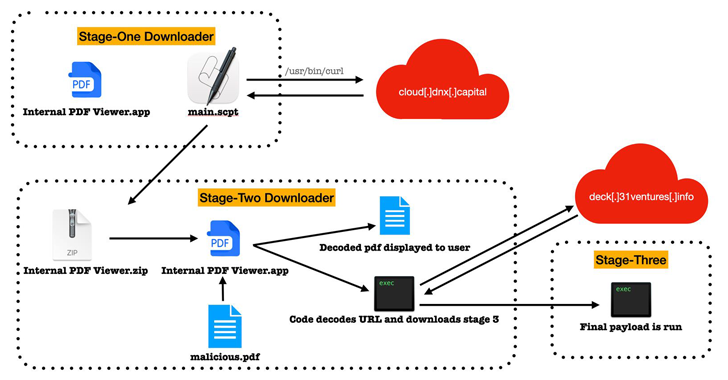
The macOS malware identified by Jamf masquerades as an “Internal PDF Viewer” software to activate the infection, though it bears noting that the success of the attack banking companies on the victim manually overriding Gatekeeper protections.
In actuality, it is really an AppleScript file that’s engineered to retrieve a second-stage payload from a distant server, which also carries the same name as its predecessor. Equally the malicious apps are signed with an advertisement-hoc signature.
The second-phase payload, penned in Objective-C, is a primary software that delivers the means to perspective PDF data files and only initiates the future stage of the attack chain when a booby-trapped PDF file is opened as a result of the app.
1 these 9-page PDF document determined by Jamf purports to give an “investment technique,” that when released, reaches out to the command-and-regulate (C2) server to down load and execute a 3rd-phase trojan, a Mach-O executable penned in Rust that comes with capabilities to run technique reconnaissance instructions.
“This PDF viewer technique used by the attacker is a clever a single,” the scientists described. “At this level, in buy to accomplish evaluation, not only do we have to have the stage-two malware but we also involve the accurate PDF file that operates as a important in order to execute the destructive code within the software.”
It’s not presently not very clear how preliminary accessibility is obtained and if the attacks have been profitable, but the development is a indication that threat actors are adapting their toolsets to accommodate cross-platform malware by using programming languages like Go and Rust.
The findings also appear off a busy time period of attacks orchestrated by the Lazarus Team aimed at businesses throughout international locations and market verticals for amassing strategic intelligence and doing cryptocurrency theft.
Lazarus Group (aka Hidden Cobra and Diamond Sleet) is considerably less a unique outfit and additional of an umbrella phrase for a mixture of point out-sponsored and felony hacking groups that sit within just the Reconnaissance Standard Bureau (RGB), North Korea’s major international intelligence apparatus.
Latest action carried out by the danger actor has offered refreshing evidence of the risk actor’s escalating fascination in exploiting believe in associations in the software program offer chain as entry points to company networks.
Very last week, the adversarial collective was linked to a cascading provide chain attack that weaponized trojanized installers variations of a legitimate app recognised as X_TRADER to breach company communications computer software maker 3CX and poison its Windows and macOS applications.
Around the exact time, ESET thorough Lazarus Group’s use of a Linux malware dubbed SimplexTea from the backdrop of a recurring social engineering campaign referred to as Procedure Desire Task.
Upcoming WEBINARZero Believe in + Deception: Understand How to Outsmart Attackers!
Uncover how Deception can detect sophisticated threats, quit lateral movement, and boost your Zero Have faith in system. Be part of our insightful webinar!
Preserve My Seat!
“It is also appealing to notice that Lazarus can develop and use native malware for all important desktop working devices: Windows, macOS, and Linux,” ESET malware researcher Marc-Etienne M.Léveillé pointed out past 7 days.
Lazarus is much from the only RGB-affiliated point out-sponsored hacking group recognised to perform functions on behalf of the sanctions-strike place. One more equally prolific risk actor is Kimsuky (aka APT43 or Emerald Sleet), a subgroup of which is monitored by Google’s Threat Assessment Team (TAG) as ARCHIPELAGO.
“The actor mostly targets corporations in the U.S. and South Korea, like men and women performing inside the federal government, army, production, educational, and think tank companies that possess matter subject skills in protection and security, especially nuclear security and nonproliferation coverage,” Google-owned Mandiant mentioned previous calendar year.
Other lesser recognised targets of Kimsuky contain Indian and Japanese federal government and instructional establishments, a set of assaults tracked by Taiwnese cybersecurity organization TeamT5 less than the identify KimDragon.
The team has a record of deploying a raft of cyber weapons to exfiltrate delicate info by way of a huge range of ways such as spear-phishing, fraudulent browser extensions, and distant obtain trojans.
Most current findings released by VirusTotal emphasize Kimsuky’s major reliance on malicious Microsoft Word paperwork to supply its payloads. A majority of the information have been submitted to the malware-scanning platform from South Korea, the U.S., Italy, and Israel, and the U.K.
“The group uses a assortment of procedures and tools to perform espionage, sabotage, and theft operations, which includes spear-phishing and credential harvesting,” the Google Chronicle subsidiary mentioned.
Found this write-up interesting? Adhere to us on Twitter and LinkedIn to study additional exceptional information we submit.
Some parts of this article are sourced from:
thehackernews.com

 Falling Dwell Time May Be Due to Faster Threat Activity
Falling Dwell Time May Be Due to Faster Threat Activity