For the duration of the previous 7 days of March, 3 significant tech firms – Microsoft, Okta, and HubSpot – described considerable facts breaches. DEV-0537, also recognised as LAPSUS$, done the to start with two. This hugely advanced group utilizes point out-of-the-art attack vectors to fantastic achievements. Meanwhile, the team guiding the HubSpot breach was not disclosed. This site will evaluate the a few breaches dependent on publicly disclosed info and advise most effective tactics to lessen the risk of this kind of attacks succeeding towards your business.
HubSpot – Employee Entry
On March 21, 2022, HubSpot described the breach which happened on March 18. Destructive actors compromised a HubSpot employee account that the worker employed for purchaser support. This authorized destructive actors the ability to accessibility and export call information working with the employee’s accessibility to numerous HubSpot accounts.
With very little data pertaining to this breach, defending against an attack is tough, but a key configuration inside HubSpot can enable. This is the “HubSpot Employee Entry” management (shown in the determine below) in HubSpot’s account placing. Clients must disable this placing at all instances, unless of course they involve particular guidance, and then promptly convert it off after finishing the company contact.
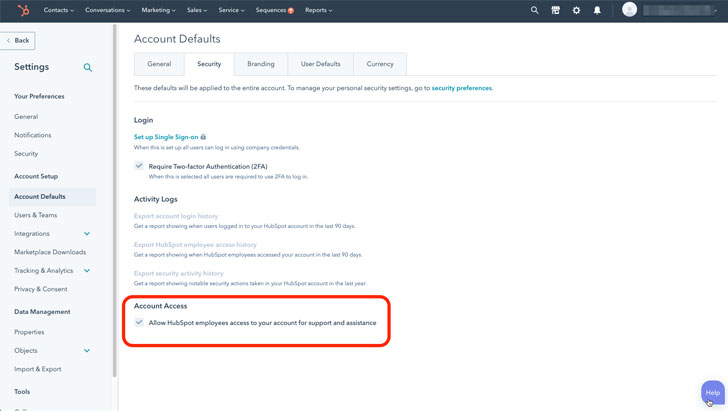
A equivalent environment seems in other SaaS purposes and must be disabled there as well. Personnel accessibility is commonly recorded in Audit Logs, which must be reviewed frequently.
Study how an SSPM can enable shield your firm from SaaS misconfigurations
Okta – Deficiency of Machine Security for Privileged User
Okta subcontracts some of its client aid to the Sitel Group. On January 21, an Okta security crew member obtained an warn that a new MFA aspect was extra to a Sitel Team personnel account from a new spot.
An investigation uncovered that a Sitel guidance engineer’s personal computer was compromised employing a remote desktop protocol. This regarded vulnerability is ordinarily disabled other than when specially needed — which helped Okta investigators slender the timeframe for the attack to a five-day window between Jan. 16-21, 2022.
Thanks to the minimal access support engineers have to their program, the effect on Okta customers was minimum. Assist engineers will not have accessibility to develop or delete consumers or download consumer databases. Their accessibility to consumer details is pretty restricted as well.
On March 22, DEV-0537, which is far more usually regarded as LAPSUS$, shared screenshots on the web. In reaction, Okta produced a assertion indicating, “there are no corrective actions our clients have to have to get.” The subsequent day the enterprise shared details of its investigation, which integrated a comprehensive reaction timeline.
While this breach was constrained in the hurt it induced, it features 3 vital security lessons.
See Cloudflare’s investigation of the January 2022 Okta compromise for a superior instance of a response to this kind of a breach.
Come across out how Adaptive Protect presents endpoint posture management and SaaS configuration regulate
Microsoft – MFA for all privileged people
On March 22, Microsoft Security shared information and facts relating to an attack it experienced at the arms of DEV-0537. Microsoft experienced a solitary account compromised, which resulted in resource code being stolen and printed.
Microsoft confident its buyers that the LAPSUS$ attack didn’t compromise any of their info, and additional said that there was no risk to any of their products and solutions owing to the stolen code.
Microsoft did not especially share how the breach was carried out, despite the fact that it did notify readers that LAPSUS$ actively recruits workers at telecoms, significant software program developers, phone centers, and other industries to share qualifications.
The company also offered these strategies for securing platforms against these assaults.
For a complete list of Microsoft’s recommendations, see this note.
Final ideas
Securing SaaS platforms is a important obstacle, and as witnessed this week, even world wide enterprises need to have to stay on top of their security. Destructive actors carry on to evolve and strengthen their attack solutions, which forces businesses to be on the lookout and prioritize their SaaS security consistently.
Sturdy passwords and SSO alternatives are no longer enough by on their own. Businesses will need sophisticated security steps, this sort of as solid MFA, IP enable lists, and blocking needless aid engineer accessibility. An automated remedy like SaaS Security Posture Administration (SSPM) can support security groups remain on top rated of these issues.
The great importance of product security in SaaS is a further takeaway from these assaults. Even a absolutely secured SaaS system can be compromised when a privileged user accesses a SaaS application from a compromised unit. Leverage a security option that combines device security posture with SaaS security posture for comprehensive, conclusion-to-conclude security.
The problem of securing SaaS solutions is intricate and beyond burdensome to entire manually. SSPM alternatives, like Adaptive Shield, can provide automatic SaaS security posture management, with configuration command, endpoint posture management, and 3rd social gathering application handle.
Be aware — This article is composed and contributed by Hananel Livneh, Senior Product Analyst at Adaptive Defend.
Observed this short article fascinating? Comply with THN on Fb, Twitter and LinkedIn to study far more exceptional information we put up.
Some parts of this article are sourced from:
thehackernews.com