Created by John Tuckner and the group at workflow and automation platform Tines, the SOC Automation Functionality Matrix (SOC ACM) is a set of strategies developed to assist security operations teams realize their automation capabilities and react additional efficiently to incidents.
A customizable, seller-agnostic instrument showcasing lists of automation prospects, it can be been shared and advisable by associates of the security local community considering that its start in January 2023, notably by Airbnb engineer Allyn Stott in his BSides and Black Hat talk, How I Learned to End Worrying and Develop a Modern Detection & Response Software.
The SOC ACM has been in contrast to the MITRE ATT&CK and RE&CT frameworks, with one particular person expressing, “it could be a conventional for classification of SOAR automations, a little bit like the RE&CT framework, but with far more automation aim.” It’s been utilised by businesses in Fintech, Cloud Security, and beyond, as a basis for examining and optimizing their security automation plans.
In this article, we are going to take a closer glimpse at how the SOC ACM will work, and share how you can use it in your corporation.
What is the SOC Automation Functionality Matrix?
The SOC Automation Capability Matrix is an interactive set of tactics that empower security operations teams to respond proactively to popular cybersecurity incidents.
It is not a list of distinct use scenarios relevant to any a single product or service or services, but a way to imagine about the capabilities an business might abide by.
It offers a stable basis for inexperienced persons to understand what is actually achievable with security automation. For far more innovative applications, it serves as a resource of inspiration for potential implementations, a resource to gauge achievement, and a usually means to report results.
Though the tool is vendor-agnostic, it pairs perfectly with a platform like Tines, which was created by security practitioners to support fellow security practitioners automate their mission-critical procedures.

How does the SOC Automation Capability Matrix do the job?
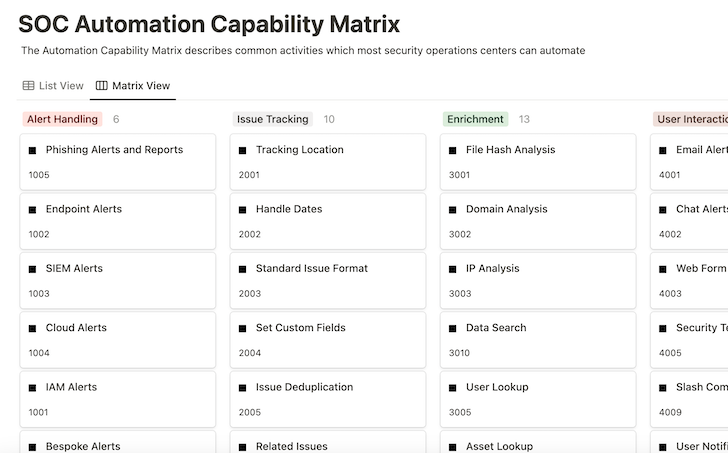
The SOC ACM is split into types that include automation capabilities.
Each and every capability comprises:
- Description – a quick overview of what the functionality is accomplishing
- Approaches – technology-agnostic ideas for how to implement the ability
- Examples – pertinent workflow templates from the Tines library
- References – other research contributing to the functionality
The framework reads from left to correct and prime to bottom in groups. Whilst it is minimally opinionated about which capabilities bring the most worth or are less difficult to put into practice, the framework is adaptable to what companies discover most important.
Each individual capacity can stand on your own in the matrix, but joining several capabilities jointly can make quite a few much more elaborate and impactful outcomes.
How to use the SOC Automation Capacity Matrix
Future, we are going to illustrate how to use the SOC ACM, taking phishing reaction as our instance. A lot of organizations make use of a number of strategies to uncover and examine suspicious messages to answer correctly to malicious emails.
To commence, in this article are some processes a regime phishing investigation may possibly involve:
In just the matrix capability, Phishing Alerts show up in the Warn Managing segment it mentions that many businesses implement resources like email security gateways to stop suspicious e-mail from staying delivered to inboxes even though also generating alerts of attack campaigns that could be automatic.

The capacity also outlines a tactic to develop a purposeful inbox for buyers to effortlessly ahead phishing email messages that could have passed via the filters. Utilizing each of these capabilities delivers an prospect to get started an automation workflow.
When a suspicious information has been determined, possibly by the user reporting or created notify, more automation abilities grow to be readily available. One recommendation is to generate a locale for monitoring the lifecycle of each individual inform as before long as feasible.
Using the Tracking Site capacity in the Issue Tracking segment, we can detect wherever these alerts must be recorded, up to date, and described. See how the workflow has now moved among sections of the Automation Ability Matrix to extend the approach.

With the alert and tracking locale resolved on, we can shift to carrying out a comprehensive examination of the phishing warn in dilemma. Phishing e-mails normally consist of likely destructive attachments and suspicious backlinks to seize authentication material and are usually despatched from spoofed sources.
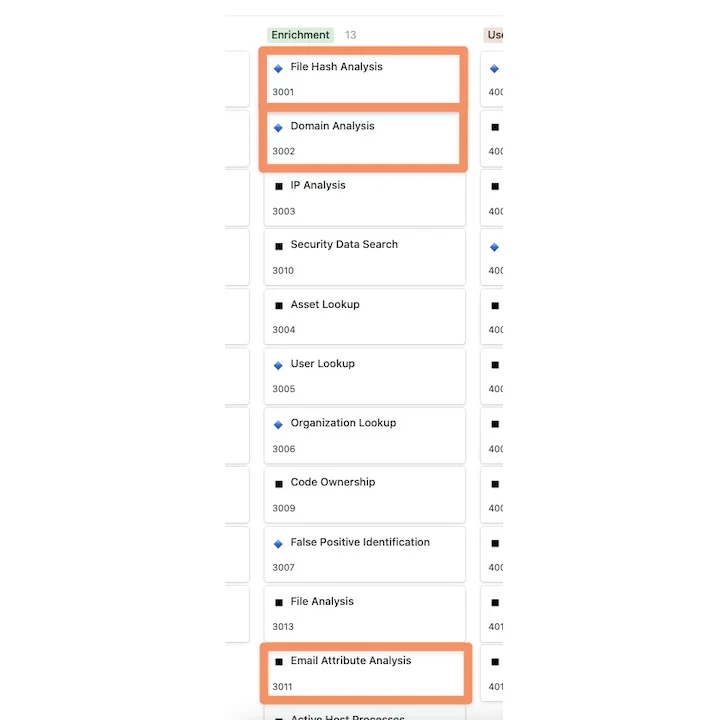
Going into the Enrichment phase, we want to concentrate on utilizing a several critical capabilities at a least: Domain Assessment for any links existing in the email human body, File Hash Assessment/File Evaluation to look at any attachments to the email, and Email Characteristics to glance further into email headers for signs of emails from spoofed addresses.
For Enrichment alternatives, the selection of possibilities for API-pushed equipment and companies that can be used to deliver these capabilities grows exponentially. Some typical options include VirusTotal for files, URLscan for domains, and EmailRep for sender information. Every of these enrichment benefits can be recorded in the linked monitoring site identified earlier to document the outcomes and offer analysts with a watch into the effects.
This exhibits how a lot of abilities from the very same portion can be used to the exact automation workflow, in this situation, to give as a lot facts as attainable to analysts.
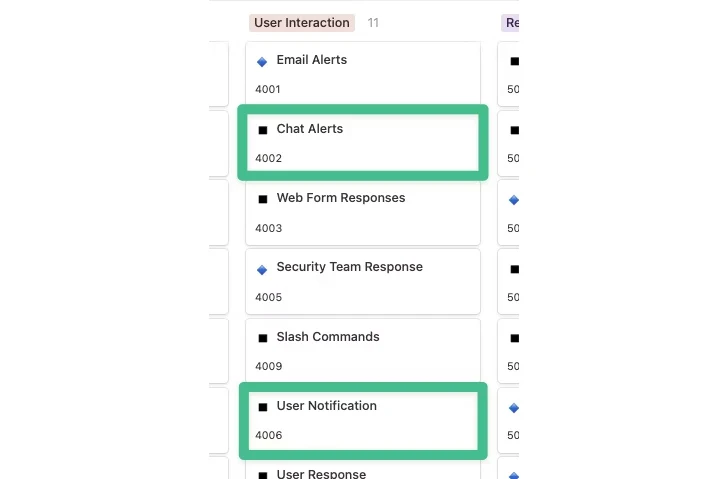
Following enrichment takes place, a verdict might be achieved now, but extra probably, the issue will involve a swift review from an analyst. At this level, the Consumer Conversation part will become critical.
To start, we can use Chat Alerts to notify the security group in a Slack channel that a phishing email has arrived and a monitoring issue has been created, with various enrichment information added as additional context is prepared for review.
That usually takes care of informing the security group, but what about updating any users who might be impacted or who documented the email? Phishing response processes, in distinct, are special due to the fact lots of businesses actively train people to report emails they may well establish as suspicious. Informing these customers with a self-assured verdict within a shorter timeframe is a fantastic way to empower operations such as having delicate documents signed promptly or protecting against mass malware outbreaks.
To do this, we can use the Person Notification ability to determine the person who noted the email and deliver them with the results of the email examination. In the circumstance of User Interaction, it is not only about added notification of the security group but also extending the attain and empowering other individuals with serious-time facts to make the proper decisions.
At this position, a good deal of activity has taken put, and we have a whole lot of expertise at our disposal. Whilst a lot more data is normally beneficial, performing on it properly is what finally counts most, ensuing in the remediation section. Lots of of the details details (indicators) we collected in advance of can be used for remediation motion. Depending on how the scenario has performed out, we could consider some of the adhering to steps:
- Domain blocklist: Increase any domains and URLs recognized as suspicious to a blocklist.
- File hash blocklist: Insert any file hashes recognized as malicious to a blocklist.
- Email deletion: Take away e-mail associated to an attack campaign from inboxes.
- Password invalidation: Change the passwords of any customers identified to have submitted credentials to a phishing web page.

The essential to any remediation is figuring out what’s attainable and starting off smaller, specifically when making use of automation to create self confidence. A single way to do this is to provide backlinks or buttons that want to be manually clicked to consider remediation steps, but in a repeatable way. If you want to introduce total automation, retaining lists of suspicious domains that can be blocked delivers you with terrific utility, minor risk, and can be mounted speedily with small general effect when errors happen.
Seeking at the course of action end-to-conclusion, we have utilized the subsequent capabilities to help automate critical actions for many cybersecurity teams:
- Phishing alerts
- Tracking locale
- File hash examination
- Area assessment
- Email attributes
- Chat alerts
- Consumer notification
- Domain blocklist
- File hash blocklist
- Email deletion
- Password invalidation
A important profit of building these capabilities in your group to address a single system, this sort of as phishing, is that numerous of these capabilities are now obtainable to be reused for additional reasons like malware detection or handling suspicious logins, making each subsequent automation option less difficult.
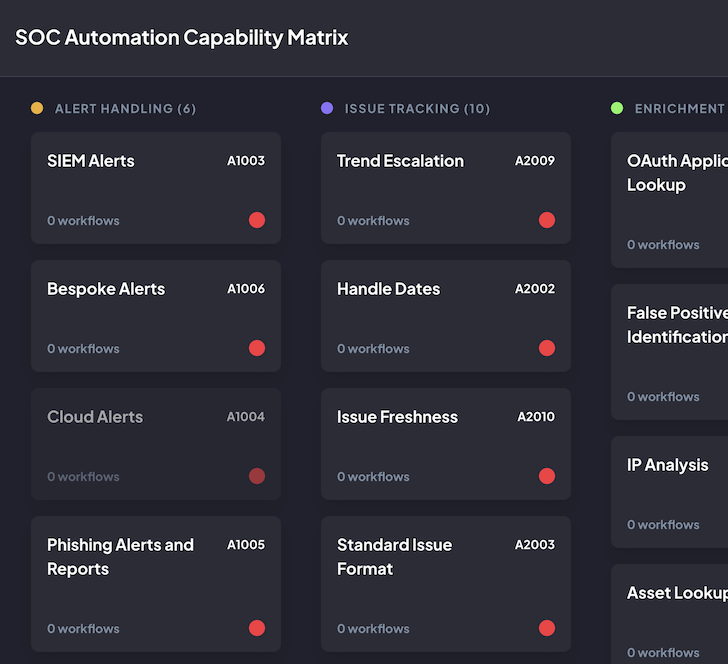
Customizing the matrix
The SOC ACM is also readily available on GitHub for those people who prefer to operate it by themselves or lead.
This way, the SOC ACM can be absolutely tailored to match your requires. This incorporates:
- Adding new classes and abilities
- Reorganizing in accordance to your priorities
- Monitoring automation workflows that align with these abilities
- Exporting the configuration
- Dark and light manner
You can also assess distinctive environments or distinctive companies in a different way by generating individual boards. For illustration, if your corporation acquires a firm with diverse capabilities from yours, you can use the matrix to visualize that setting absolutely in different ways.
All of this configuration can be saved domestically in your browser for privacy. As properly as exporting the configuration, you can import it to revive past assessments, all without the need of a login account, and devoid of any monitoring.
The SOC ACM as a reporting instrument
Teams accessing the SOC ACM on GitHub can also use the matrix to visually reveal exactly where they are in their automation journey and connect the value of their automation plan to leadership and other essential stakeholders.
Quickly after utilizing a several abilities, teams will recognize which capabilities they are employing most, the connected routines, and their value, such as time saved or lowered reaction time. This enables them to share outcomes with pertinent groups and make your mind up what to prioritize subsequent.
Circumstance study: monitoring time saved and executions to clearly show benefit with the SOC ACM
At the Tines Roadshow: San Francisco, the creator of the SOC Automation Functionality Matrix, John Tuckner, shared how he worked with a Fintech business to assess and increase their automation application using the matrix. They told Tuckner, “The Automation Capacity Matrix assists us manage our workflows, establish which workflows are saving us the most time, and spotlight long run regions of chance.”
Highlights:
- 25 abilities carried out and tagged
- 10 workflows making use of Slack slash commands with 2,000 executions
- Send out multifactor prompt workflows ran 721 moments for 6.5 hours of time savings per month
Recommendations:
- Look at controlling lists of IOCs for reaction capabilities, “IP record,”https://thehackernews.com/2024/02/”area record,” and “hash listing.”
- Document and spotlight the endeavours created in time saved when utilizing scenario management.
Long run point out – what they will do differently:
- Tackling distributed alerting, consumer interaction through Slack
- Person notification
- User reaction
- Updating security Slack channel and incident reporting to use a Slack bot and route reports and asks to the proper subteam
- Notify crisis resources
- Timed escalations
- Slash commands
- Add a lot more response actions through Tines automation as a result of our Slack bot
- Artifact collecting
- Disabling MFA machine
- Asset lookup (not just endpoints, need to include cloud property)
The SOC Automation Ability Matrix is a valuable resource for groups at all phases in their automation journey, offering inspiration for their up coming automation builds and a suggests to assess their automation software.
If you’d like to discover the SOC Automation Ability Matrix in far more detail, you will obtain it on Idea, hosted by the Tines team.
Observed this post exciting? This posting is a contributed piece from one of our valued associates. Comply with us on Twitter and LinkedIn to read through a lot more unique written content we put up.
Some parts of this article are sourced from:
thehackernews.com

 Researchers Detail Apple’s Recent Zero-Click Shortcuts Vulnerability
Researchers Detail Apple’s Recent Zero-Click Shortcuts Vulnerability