The economically inspired FIN7 cybercrime gang has masqueraded as nevertheless yet another fictitious cybersecurity firm termed “Bastion Secure” to recruit unwitting software program engineers beneath the guise of penetration screening in a probably lead-up to a ransomware scheme.
“With FIN7’s hottest faux company, the criminal team leveraged real, publicly out there information and facts from numerous legit cybersecurity organizations to develop a skinny veil of legitimacy about Bastion Protected,” Recorded Future’s Gemini Advisory device explained in a report. “FIN7 is adopting disinformation techniques so that if a prospective hire or intrigued party ended up to fact test Bastion Protected, then a cursory lookup on Google would return ‘true’ facts for corporations with a very similar title or sector to FIN7’s Bastion Safe.”

FIN7, also recognised as Carbanak, Carbon Spider, and Anunak, has a track history of placing restaurant, gambling, and hospitality industries in the U.S. to infect position-of-sale (POS) systems with malware built to harvest credit and debit card quantities that are then applied or marketed for financial gain on underground marketplaces. The newest advancement shows the group’s expansion into the really worthwhile ransomware landscape.
Environment up pretend entrance organizations is very little new for FIN7, which has been previously connected to one more sham cybersecurity firm dubbed Combi Security that claimed to offer penetration tests expert services to consumers. Seen in that light, Bastion Protected is no distinctive.
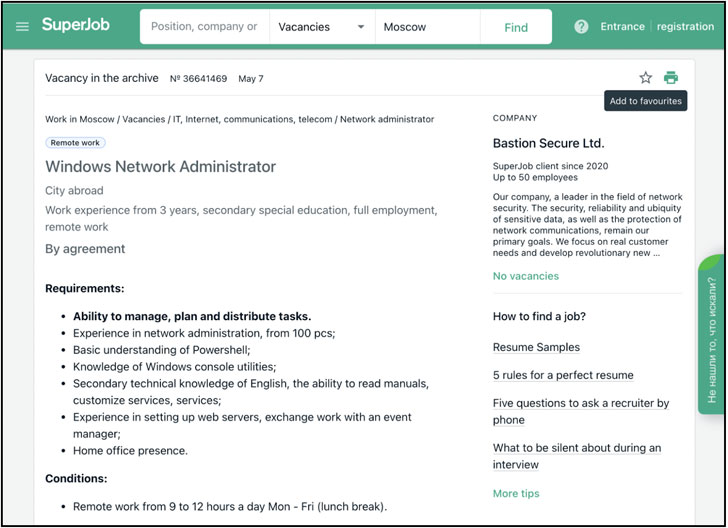
Not only does the new web-site characteristic stolen material compiled from other reputable cybersecurity companies — primarily Convergent Network Alternatives — the operators marketed seemingly legitimate hiring options for C++, PHP, and Python programmers, process directors, and reverse-engineers on well-liked job boards, featuring them numerous instruments for observe assignments throughout the job interview course of action.
These tools were being analyzed and identified to be parts of the article-exploitation toolkits Carbanak and Lizar/Tirion, each of which have been previously attributed to the group and can be leveraged to compromise POS devices and deploy ransomware.
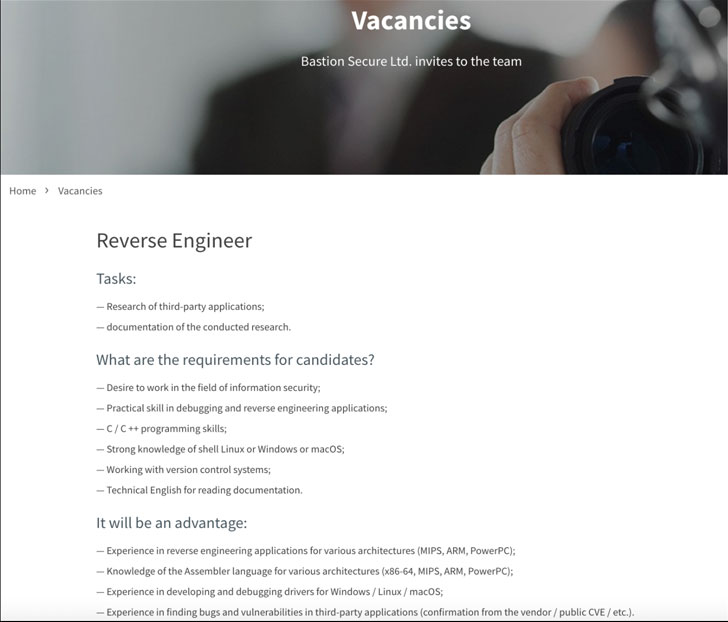
It really is, even so, in the subsequent stage of the using the services of process that Bastion Secure’s involvement in criminal exercise became evident, what with the firm’s reps delivering access to a so-referred to as consumer firm’s network and asking prospective candidates to assemble information and facts on domain administrators, file units, and backups, signalling a sturdy inclination towards conducting ransomware assaults.
“Bastion Secure’s career delivers for IT specialist positions ranged among $800 and $1,200 USD a thirty day period, which is a feasible starting up wage for this style of situation in put up-Soviet states,” the scientists claimed. “However, this ‘salary’ would be a smaller portion of a cybercriminal’s portion of the criminal income from a productive ransomware extortion or substantial-scale payment card-stealing procedure.”
By spending “unwitting ’employees’ significantly a lot less than it would have to pay back knowledgeable criminal accomplices for its ransomware schemes, […] FIN7’s fake organization plan permits the operators of FIN7 to attain the talent that the group requires to have out its felony activities, whilst at the same time retaining a larger share of the profits,” the scientists extra.
Moreover posing as a company entity, an further stage taken by the actor to give it a ring of authenticity is the point that just one of the firm’s business addresses is the identical as that of a now-defunct, U.K.-dependent company named Bastion Security (North) Constrained. Web browsers this kind of as Apple Safari and Google Chrome have considering that blocked accessibility to the deceptive site.
“Even though cybercriminals searching for unwitting accomplices on reputable job websites is nothing new, the sheer scale and blatancy with which FIN7 operates continue on to surpass the actions revealed by other cybercriminal groups,” the scientists reported, including the group is “attempting to obfuscate its correct identification as a prolific cybercriminal and ransomware team by making a fabricated web presence via a mainly genuine-showing website, specialist task postings, and company data web pages on Russian-language business enterprise growth web sites.”
Located this post intriguing? Adhere to THN on Fb, Twitter and LinkedIn to study additional unique material we submit.
Some parts of this article are sourced from:
thehackernews.com


 Researchers Discover Microsoft-Signed FiveSys Rootkit in the Wild
Researchers Discover Microsoft-Signed FiveSys Rootkit in the Wild