A zero-day flaw in a WordPress plugin referred to as BackupBuddy is currently being actively exploited, WordPress security enterprise Wordfence has disclosed.
“This vulnerability will make it probable for unauthenticated buyers to obtain arbitrary documents from the impacted website which can incorporate sensitive details,” it reported.
BackupBuddy enables people to back up their whole WordPress set up from in the dashboard, like theme documents, web pages, posts, widgets, users, and media files, among other people.

The plugin is approximated to have close to 140,000 energetic installations, with the flaw (CVE-2022-31474, CVSS rating: 7.5) influencing variations 8.5.8. to 8.7.4.1. It is been tackled in version 8.7.5 unveiled on September 2, 2022.
The issue is rooted in the operate named “Area Listing Duplicate” which is designed to retailer a community copy of the backups. In accordance to Wordfence, the vulnerability is the end result of the insecure implementation, which enables an unauthenticated danger actor to download any arbitrary file on the server.
More details about the flaw have been withheld in light-weight of energetic in-the-wild abuse and its relieve of exploitation.
“This vulnerability could enable an attacker to perspective the contents of any file on your server that can be browse by your WordPress installation,” the plugin’s developer, iThemes, claimed. “This could consist of the WordPress wp-config.php file and, dependent on your server setup, sensitive data files like /etc/passwd.”
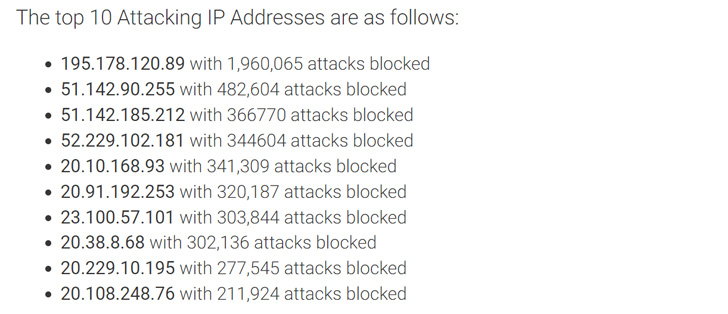
Wordfence noted that the concentrating on of CVE-2022-31474 commenced on August 26, 2022, and that it has blocked nearly 5 million attacks in the intervening time period. Most of the intrusions have attempted to examine the under data files –
- /and many others/passwd
- /wp-config.php
- .my.cnf
- .accesshash
Users of the BackupBuddy plugin are encouraged to update to the most recent edition. Really should consumers figure out that they could have been compromised, it really is recommended to reset the database password, transform WordPress Salts, and rotate API keys stored in wp-config.php.
Discovered this write-up fascinating? Adhere to THN on Fb, Twitter and LinkedIn to browse far more unique content we submit.
Some parts of this article are sourced from:
thehackernews.com


 YouTube will let creators offer paid video courses next year
YouTube will let creators offer paid video courses next year