Threat actors have been exploiting the recently disclosed zero-day flaw in Palo Alto Networks PAN-OS software package courting again to March 26, 2024, practically three months right before it came to light yesterday.
The network security firm’s Unit 42 division is monitoring the exercise less than the title Procedure MidnightEclipse, attributing it as the operate of a one threat actor of unknown provenance.
The security vulnerability, tracked as CVE-2024-3400 (CVSS score: 10.), is a command injection flaw that enables unauthenticated attackers to execute arbitrary code with root privileges on the firewall.
It’s worthy of noting that the issue is relevant only to PAN-OS 10.2, PAN-OS 11., and PAN-OS 11.1 firewall configurations that have GlobalProtect gateway and device telemetry enabled.
Procedure MidnightEclipse entails the exploitation of the flaw to build a cron task that runs just about every minute to fetch instructions hosted on an exterior server (“172.233.228[.]93/plan” or “172.233.228[.]93/patch”), which are then executed using the bash shell.
The attackers are mentioned to have manually managed an obtain handle list (ACL) for the command-and-regulate (C2) server to make certain that it can only be accessed from the device communicating with it.

While the correct mother nature of the command is unfamiliar, it can be suspected that the URL serves as a shipping and delivery automobile for a Python-based mostly backdoor on the firewall that Volexity – which discovered in-the-wild exploitation of CVE-2024-3400 on April 10, 2024 – is tracking as UPSTYLE and is hosted on a distinctive server (“144.172.79[.]92” and “nhdata.s3-us-west-2.amazonaws[.]com”).
The Python file is created to produce and start yet another Python script (“process.pth”), which subsequently decodes and operates the embedded backdoor element that’s liable for executing the threat actor’s instructions in a file called “sslvpn_ngx_error.log.” The final results of the operation are penned to a independent file named “bootstrap.min.css.”
The most fascinating facet of the attack chain is that both of those the information used to extract the commands and generate the effects are genuine information related with the firewall –
- /var/log/pan/sslvpn_ngx_error.log
- /var/appweb/sslvpndocs/world-secure/portal/css/bootstrap.min.css
As for how the commands are composed to the web server mistake log, the menace actor forges specifically crafted network requests to a non-existent web page containing a particular pattern. The backdoor then parses the log file and queries for the line matching the similar typical expression (“img[([a-zA-Z0-9+/=]+)]”) to decode and operate the command in just it.
“The script will then create a further thread that operates a function identified as restore,” Unit 42 stated. “The restore purpose will take the first content material of the bootstrap.min.css file, as perfectly as the original access and modified occasions, sleeps for 15 seconds and writes the unique contents back to the file and sets the obtain and modified periods to their originals.”
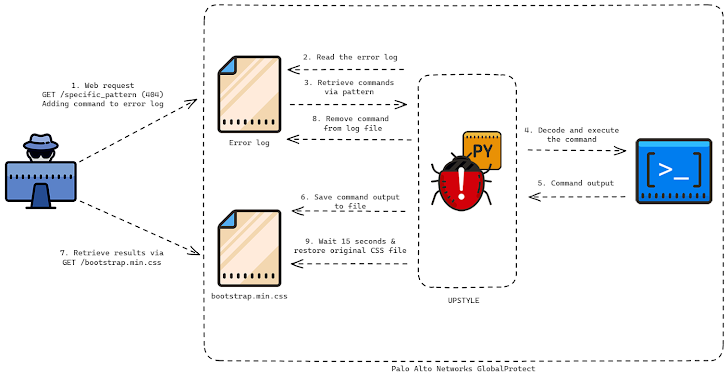
The major aim seems to be to keep away from leaving traces of the command outputs, necessitating that the benefits are exfiltrated in just 15 seconds before the file is overwritten.
Volexity, in its personal investigation, stated it noticed the menace actor remotely exploiting the firewall to build a reverse shell, download supplemental tooling, pivot into inner networks, and finally exfiltrate data. The actual scale of the campaign is presently unclear. The adversary has been assigned the moniker UTA0218 by the firm.

“The tradecraft and pace used by the attacker suggests a highly capable menace actor with a crystal clear playbook of what to entry to even further their aims,” the American cybersecurity business reported.
“UTA0218’s preliminary goals were being aimed at grabbing the area backup DPAPI keys and focusing on lively directory credentials by acquiring the NTDS.DIT file. They even further targeted consumer workstations to steal saved cookies and login data, along with the users’ DPAPI keys.”
Businesses are advised to look for indications of lateral motion internally from their Palo Alto Networks GlobalProtect firewall unit.
The advancement has also prompted the U.S. Cybersecurity and Infrastructure Security Agency (CISA) to increase the flaw to its Known Exploited Vulnerabilities (KEV) catalog, requiring federal organizations to utilize the patches by April 19 to mitigate prospective threats. Palo Alto Networks is anticipated to release fixes for the flaw no afterwards than April 14.
“Targeting edge products remains a popular vector of attack for capable menace actors who have the time and resources to commit into exploring new vulnerabilities,” Volexity mentioned.
“It is remarkably probable UTA0218 is a point out-backed menace actor based mostly on the assets needed to create and exploit a vulnerability of this character, the variety of victims focused by this actor, and the capabilities exhibited to set up the Python backdoor and further more access target networks.”
Observed this report fascinating? Abide by us on Twitter and LinkedIn to read through a lot more special articles we article.
Some parts of this article are sourced from:
thehackernews.com

 Popular Rust Crate liblzma-sys Compromised with XZ Utils Backdoor Files
Popular Rust Crate liblzma-sys Compromised with XZ Utils Backdoor Files