DevOps system GitLab has unveiled program updates to tackle a critical security vulnerability that, if potentially exploited, could permit an adversary to seize manage of accounts.
Tracked as CVE-2022-1162, the issue has a CVSS score of 9.1 and is said to have been identified internally by the GitLab group.
“A hardcoded password was established for accounts registered utilizing an OmniAuth provider (e.g., OAuth, LDAP, SAML) in GitLab CE/EE variations 14.7 prior to 14.7.7, 14.8 prior to 14.8.5, and 14.9 prior to 14.9.2 allowing attackers to possibly take in excess of accounts,” the enterprise mentioned in an advisory posted on March 31.
GitLab, which has addressed the bug with the most current release of versions 14.9.2, 14.8.5, and 14.7.7 for GitLab Group Version (CE) and Enterprise Version (EE), also reported it took the step of resetting the password of an unspecified variety of buyers out of an abundance of caution.
“Our investigation displays no sign that customers or accounts have been compromised,” it extra.

The organization has also printed a script that directors of self-managed cases can operate to single out accounts likely impacted by CVE-2022-1162. After the afflicted accounts are determined, a password reset has been recommended.
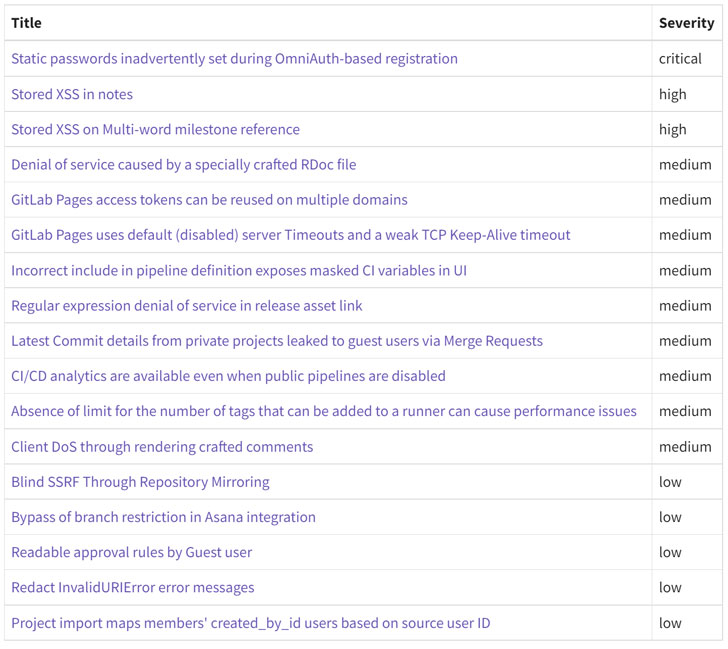
Also resolved by GitLab as element of the security update are two large-severity stored cross-web site scripting (XSS) bugs (CVE-2022-1175 and CVE-2022-1190) as effectively as 9 medium-severity flaws and 5 issues that are rated low in severity.
In gentle of the criticality of some of the issues, end users jogging influenced installations are remarkably encouraged to upgrade to the most current model as quickly as feasible.
Located this article intriguing? Adhere to THN on Facebook, Twitter and LinkedIn to browse more exceptional content material we submit.
Some parts of this article are sourced from:
thehackernews.com


 ASUS ZenBook laptops are up to $250 off at Amazon today only
ASUS ZenBook laptops are up to $250 off at Amazon today only