The financially motivated FIN8 actor, in all probability, has resurfaced with a never-before-seen ransomware strain termed “White Rabbit” that was lately deployed against a area financial institution in the U.S. in December 2021.
That’s in accordance to new results published by Development Micro, contacting out the malware’s overlaps with Egregor, which was taken down by Ukrainian law enforcement authorities in February 2021.
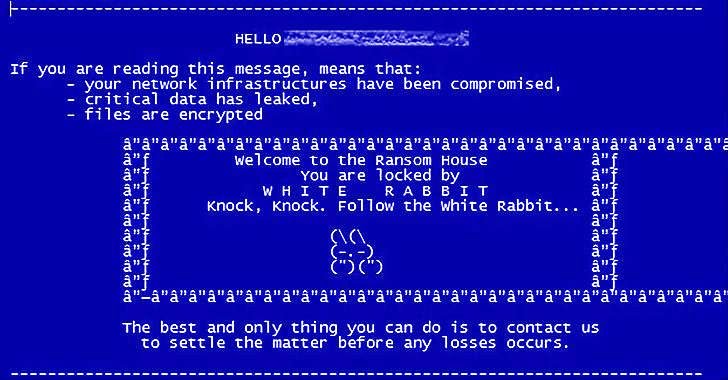
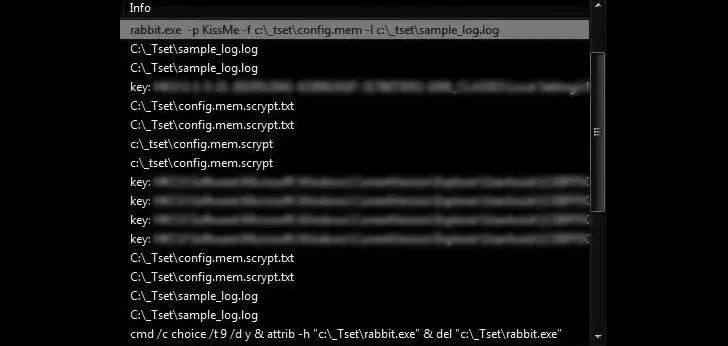
“One particular of the most notable factors of White Rabbit’s attack is how its payload binary involves a specific command-line password to decrypt its inner configuration and carry on with its ransomware program,” the scientists famous. “This method of hiding destructive exercise is a trick that the ransomware family Egregor works by using to conceal malware methods from analysis.”
Egregor, which commenced functions in September 2020 until its functions took a large strike, is broadly believed to be a reincarnation of Maze, which shut down its criminal company afterwards that yr.
In addition to having a leaf out of Egregor’s playbook, White Rabbit adheres to the double extortion scheme and is believed to have been shipped via Cobalt Strike, a write-up-exploitation framework that is place to use by danger actors to reconnoiter, infiltrate, and fall destructive payloads into the affected process.
Double extortion, also identified as fork out-now-or-get-breached, refers to an increasingly well known ransomware strategy in which valuable info from the targets is exfiltrated prior to launching the encryption routine, adopted by pressurizing the victims into shelling out up to prevent the stolen details from currently being printed on the internet.
Certainly, the ransom note displayed soon after the completion of the encryption approach warns the target that their details will be posted or offered the moment the four-working day deadline to meet up with their calls for elapses. “We will also send the info to all intrigued supervisory companies and the media,” the note provides.
While authentic-planet attacks involving White Rabbit have obtained awareness only not long ago, digital forensic clues piecing collectively its trail factors to a string of malicious routines commencing as early as July 2021.
What is actually far more, evaluation of the ransomware samples dating again to August 2021 reveals that the malware is an updated model of the Sardonic backdoor, which Bitdefender described final year as an actively formulated malware encountered in the aftermath of an unsuccessful attack concentrating on a economic establishment in the U.S.
“The specific romantic relationship among the White Rabbit group and FIN8 is now mysterious,” cybersecurity company Lodestone explained, including it observed a “number of TTPs suggesting that White Rabbit, if working independently of FIN8, has a near marriage with the extra established menace team or is mimicking them.”
“Presented that FIN8 is known mainly for its infiltration and reconnaissance resources, the relationship could be an sign of how the group is increasing its arsenal to incorporate ransomware,” Craze Micro explained. “So considerably, White Rabbit’s targets have been few, which could indicate that they are nevertheless tests the waters or warming up for a massive-scale attack.”
Identified this article exciting? Follow THN on Fb, Twitter and LinkedIn to browse additional exclusive content material we put up.
Some parts of this article are sourced from:
thehackernews.com