A cyberespionage threat actor acknowledged for targeting a wide range of critical infrastructure sectors in Africa, the Middle East, and the U.S. has been observed utilizing an upgraded edition of a distant obtain trojan with facts stealing abilities.
Contacting TA410 an umbrella group comprised of 3 teams dubbed FlowingFrog, LookingFrog and JollyFrog, Slovak cybersecurity firm ESET assessed that “these subgroups function rather independently, but that they might share intelligence prerequisites, an obtain group that operates their spear-phishing strategies, and also the workforce that deploys network infrastructure.”
TA410 — claimed to share behavioral and tooling overlaps with APT10 (aka Stone Panda or TA429) — has a history of focusing on U.S-based mostly organizations in the utilities sector as well as diplomatic entities in the Middle East and Africa.
Other victims of the hacker collective incorporate a production firm in Japan, a mining organization in India, and a charity in Israel, in addition to unnamed victims in the instruction and armed forces verticals.

TA410 was 1st documented by Proofpoint in August 2019 when the menace actor unleashed phishing campaigns that contains macro-laden files to compromise utility vendors throughout the U.S. with a modular malware called LookBack.
Approximately a year later, the team returned with a new backdoor codenamed FlowCloud, also shipped to U.S. utilities companies, that Proofpoint explained as malware that presents attackers complete command over contaminated techniques.

“Its distant accessibility trojan (RAT) features incorporates the capacity to obtain put in apps, the keyboard, mouse, monitor, information, expert services, and procedures with the skill to exfiltrate information and facts by using command-and-handle,” the corporation noted in June 2020.
Industrial cybersecurity firm Dragos, which tracks the action team underneath the moniker TALONITE, pointed out the group’s penchant for blending procedures and strategies in order to guarantee a prosperous intrusion.
“TALONITE focuses on subverting and having edge of have faith in with phishing lures concentrating on engineering-particular themes and principles, malware that abuses normally genuine binaries or modifies these binaries to contain added performance, and a mixture of owned and compromised network infrastructure,” Dragos claimed in April 2021.
ESET’s investigation into the hacking crew’s modus operandi and toolset has get rid of gentle on a new variation of FlowCloud, which will come with the means to record audio applying a computer’s microphone, check clipboard functions, and manage attached camera equipment to just take photographs.
Specifically, the audio recording functionality is created to be automatically triggered when sound stages in close proximity to the compromised pc cross a 65-decibel threshold.
TA410 is also known to get benefit of both equally spear-phishing and susceptible internet-dealing with programs these types of as Microsoft Trade, SharePoint, and SQL Servers to attain first access.
“This suggests to us that their victims are specific precisely, with the attackers picking out which entry approach has the very best possibility of infiltrating the target,” ESET malware researcher Alexandre Côté Cyr explained.
Every single group inside of the TA410 umbrella is stated to use various toolsets. Whilst JollyFrog depends on off-the-shelf malware these kinds of as QuasarRAT and Korplug (aka PlugX), LookingFrog takes advantage of X4, a barebones implant, and LookBack.
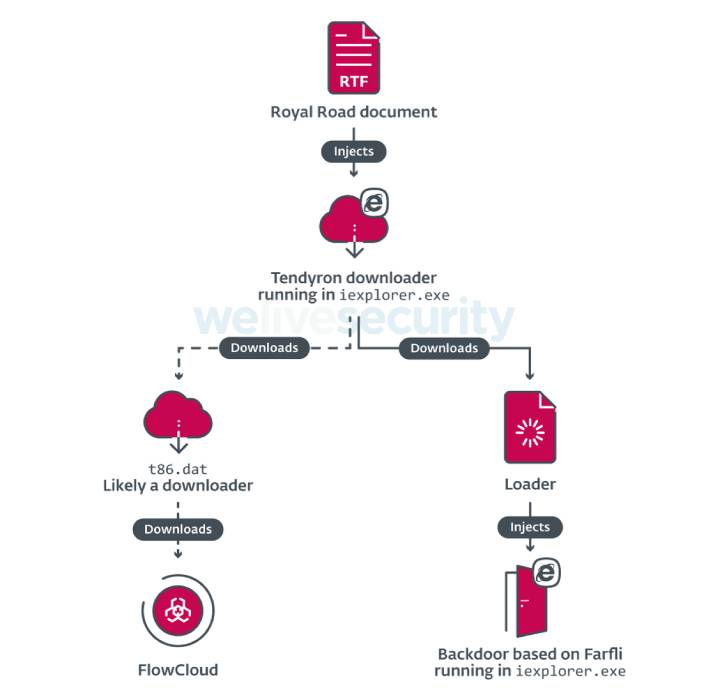
FlowingFrog, in contrast, employs a downloader termed Tendyron that is shipped by signifies of the Royal Highway RTF weaponizer, making use of it to down load FlowCloud as nicely as a next backdoor, which is primarily based on Gh0stRAT (aka Farfli).
“TA410 is a cyberespionage umbrella targeting higher-profile entities these types of as governments and universities globally,” ESET claimed. “Even even though the JollyFrog staff takes advantage of generic instruments, FlowingFrog and LookingFrog have access to complex implants these as FlowCloud and LookBack.”
Identified this write-up attention-grabbing? Observe THN on Facebook, Twitter and LinkedIn to read far more exceptional material we write-up.
Some parts of this article are sourced from:
thehackernews.com

