The risk actor at the rear of the prolific Emotet botnet is testing new attack methods on a small scale before co-opting them into their larger sized quantity malspam campaigns, probably in response to Microsoft’s shift to disable Visible Simple for Apps (VBA) macros by default across its solutions.
Contacting the new action a “departure” from the group’s standard behavior, ProofPoint alternatively raised the chance that the newest established of phishing email messages distributing the malware display that the operators are now “engaged in a lot more selective and confined assaults in parallel to the regular substantial scale email strategies.”

Emotet, the handiwork of a cybercrime team tracked as TA542 (aka Mummy Spider or Gold Crestwood), staged a revival of sorts late last 12 months soon after a 10-month-long hiatus pursuing a coordinated regulation enforcement operation to take down its attack infrastructure.
Because then, Emotet strategies have qualified 1000’s of clients with tens of 1000’s of messages in a number of geographic areas, with the message quantity surpassing around 1 million per marketing campaign in pick cases.
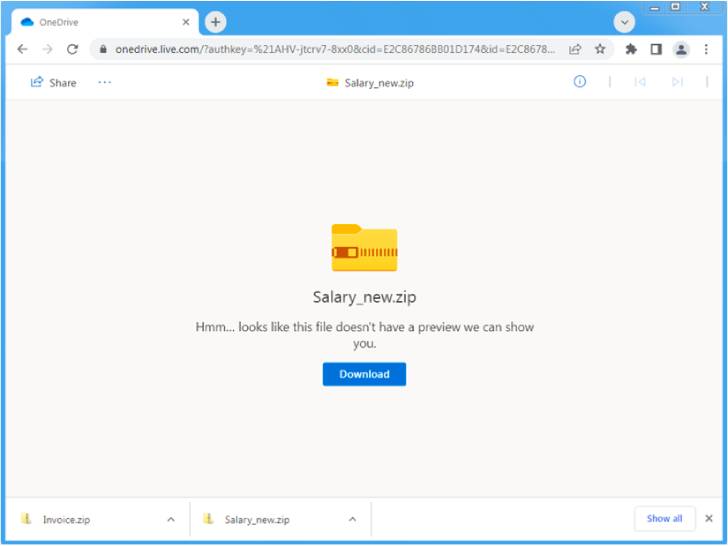
The new “reduced quantity” email marketing campaign analyzed by the enterprise security agency concerned the use of salary-themed lures and OneDrive URLs hosting ZIP archives that contain Microsoft Excel Include-in (XLL) information, which, when executed, drop and operate the Emotet payload.
The new set of social engineering assaults is mentioned to have taken put concerning April 4, 2022, and April 19, 2022, when other common Emotet campaigns were put on keep.

The absence of macro-enabled Microsoft Excel or Word doc attachments is a sizeable change from formerly observed Emotet attacks, suggesting that the threat actor is pivoting away from the technique as a way to get about Microsoft’s plans to block VBA macros by default beginning April 2022.
The growth also arrives as the malware authors final 7 days preset an issue that prevented possible victims from receiving compromised on opening the weaponized email attachments.
“After months of reliable exercise, Emotet is switching matters up,” Sherrod DeGrippo, vice president of menace investigation and detection at Proofpoint, explained.
“It is likely the risk actor is testing new behaviors on a compact scale before delivering them to victims extra broadly, or to distribute by way of new TTPs together with its current higher-volume strategies. Businesses should be mindful of the new techniques and make sure they are applying defenses accordingly.”
Identified this article fascinating? Follow THN on Fb, Twitter and LinkedIn to go through a lot more unique content material we put up.
Some parts of this article are sourced from:
thehackernews.com


 Firms Push for CVE-Like Cloud Bug System
Firms Push for CVE-Like Cloud Bug System